Command and Control – Browser
Red Teams are always focused in the discovery of innovative ways to establish connections back to their command and control infrastructure. The main reasons that leads red teams to use standard protocols or native system functionality for command and control operations is to bypass some sort of restrictions and to stay of the radar of the blue team. 0x09AL developed Browser-C2 in Go which uses the browser (Chrome) as a communication channel and can bypass host based firewalls. 0x09AL described the idea and the operation of the tool in his blog.
The tool requires the following two components in order to operate successfully.
go get -u github.com/gorilla/mux go get -u github.com/chzyer/readline
The implant can be compiled to executable with the following command. However prior to that activity the agent.go file needs to be changed to contain the IP address of the C2 server.
go build agent.go

The jquery file needs to modified to contain the IP of the command and control server in the var url parameter.

The main command and control application can be compiled with the following:
go build
When the implant will executed on the target host Chrome browser will initiate and automatically will reach the Command and Control server endpoint.

A connection will establish with the C2 server and commands can be executed to retrieve host information.

The Windows Management Instrumentation command line utility can be also used for additional host recon.
wmic useraccount list full

Browser-C2 doesn’t support encryption for communication between the server and the compromised host and has limited functionality since it cannot execute PowerShell scripts and it can only used for basic command execution. For additional operations an alternative channel such as Meterpeter or PoshC2 can be considered. The Metasploit Framework module web delivery will generate and host a scriptlet automatically.
exploit/multi/script/web_delivery

The regsvr32 is a common method discovered by Casey Smith which bypasses AppLocker policies and it is a reliable technique to execute arbitrary code remotely. The scriptlet can be executed from an existing Browser-C2 agent session.

When the payload will delivered a Meterpreter session will open which will provide enhanced capabilities.

Usage of the same method can also establish a connection with PoshC2 for post-exploitation activities based in PowerShell.

The implant handler of PoshC2 will receive the connection.

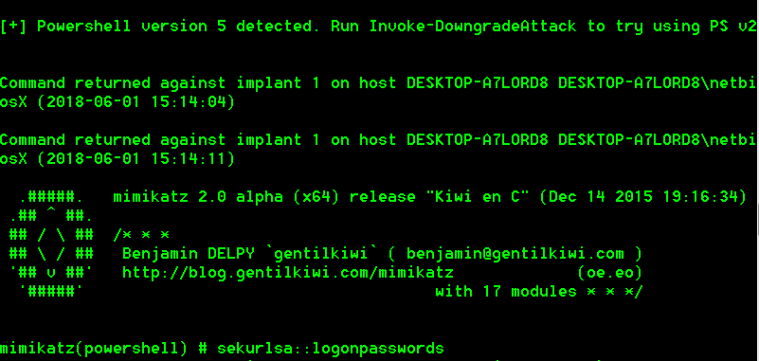
Interaction with the implant will start by selecting the associated ID. PoshC2 contains various PowerShell modules which can be used for extensive host recon credential grabbing like Mimikatz.

Mimikatz output will appear in the PoshC2 console.