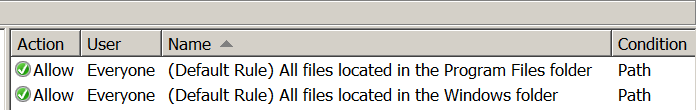
AppLocker rules by default are allowing all the files that are inside in the Windows folder and Program files to be executed as otherwise the system will not operate as normal. If appropriate permissions are not set in these folders an attacker could exploit this in order to bypass AppLocker.
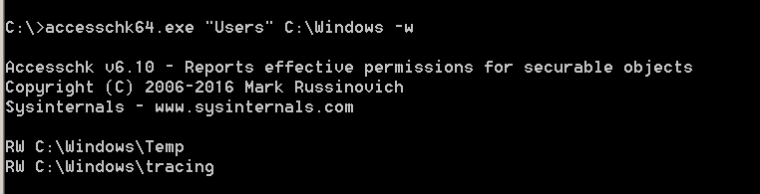
Windows environments (check was done in Windows Server 2008 R2) by default allowing standard users of the system to have read and write access in these folders:
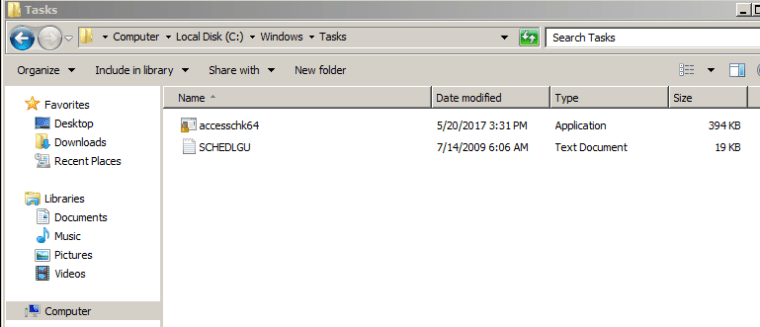
- C:\Windows\Tasks
- C:\Windows\Temp
- C:\Windows\tracing
The accesschk tool can be used to identify if the group “Users” have RW permissions inside the Windows folder.
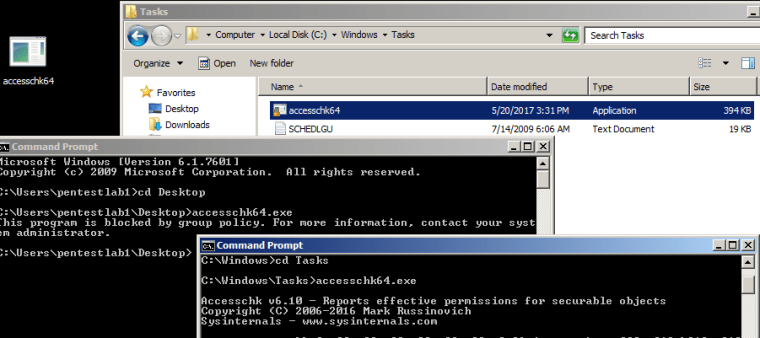
The next step is to drop the binary into the folder that has weak permissions and execute it. In this case the executable is the legitimate application accesschk64.
Since the AppLocker rules are allowing files that are contained inside the Windows folder to be executed then the utility would run as normal. Otherwise it will be blocked by the AppLocker rules.
Conclusion
Implementing AppLocker by default doesn’t really provide any security measure since it can be bypassed easily. As AppLocker by default trusts Microsoft signed binaries and Windows folders it is essential to evaluate permissions and trusted binaries that can execute code in order to protect effectively the Windows ecosystem.
Thanks!
In this case, changing by GPO NTFS permissions for this folders could be a solution?
Best regards!
Correct! Read only permissions to these folders will disallow them to bypass the default AppLocker rule.
1. Users do have write permission to C:\Windows\tracing, but no execution permission on files located there.
2. Users do not have read permissions to C:\Windows\temp but users can write files into it and also run them if they know there exact path. So this folder should still be added to the exclusions list of the default rule.
3. The folder tasks should also be added to the exclusions list of that rule.
Reblogged this on Cybersecurity .