The main purpose of port forwarding while performing a penetration test is to help us reach a specific port on a system that doesn’t exist on the same network.In order to understand this better let’s assume that we have compromised a system which belongs to two networks.The one network is the public that we managed to gain access and the other one is the private that other systems exists as well.
All we have to do is to set up a local listener to our machine that would communicate with the meterpreter session that we have opened from the compromised system.This meterpreter session will actually forward the port to the machine that is running the service and is not accessible directly from our system.
Let’s say that we have successfully exploited the system through a vulnerability and we have opened a meterpreter session.The first thing that we have to do is to use the route command in order to be able to communicate with the internal network (private) through the compromised machine.The 192.168.2.2 is the private IP of the system that we have exploited,the 255.255.255.0 is the subnet mask and the 1 is the number of the meterpreter session.You can see the command and the routing table in the image below:

Now that we can reach the internal network through the compromised system we can use the TCP scanner of metasploit framework in order to discover any open ports on the remote target.
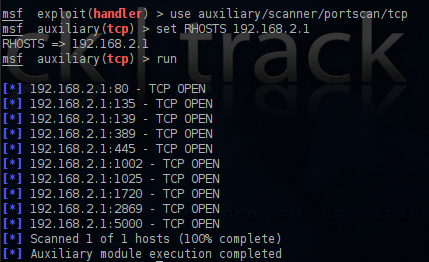
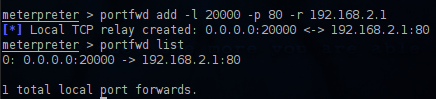
We can see that the port 80 is open.This is an indication that probably a web server is running on that port. In order to reach that port from our machine we need to set up port forwarding to the machine that we have exploited.So lets connect again to our meterpreter session and use the command portfwd -h in order to see the available options.

The option -L is optional as you can see so this means that if we don’t set a specific IP it will listen to all the adapters of our machine.For the -l (local port) we can specify any port of our choice,for the -p the remote port that we want to reach which in this case is the port 80 and for the -r the IP of the remote target.So the command will be as it appears on the next screenshot.
Now we can use our browser in order to access the remote web server.

Conclusion
In this article we saw how we can set up port forwarding in order to access a specific port on a system that exists on an internal network by using another system that has been exploited.The same method can be implemented and for any other service that we want to reach (SSH,Telnet,FTP etc).
Reblogged this on CoreNumb Security and commented:
Nice article about post port forwarding on post exploit