FTP is a service that is commonly used in Web Servers from Webmasters for accessing the files remotely.So it is almost impossible not to find this service in one of our clients systems during an engagement.
For that reason we will try to cover in this article a scenario of a possible attack against the FTP Server.
The first thing that we need to do is of course to identify which systems are running the FTP service (for the needs of this tutorial I have put only one system). We can do a simple scan with Nmap in order to find the open ports.

We can see that the FTP port is open. Now the next logical step that we have to do is to identify which version the FTP application is running by using a method which called FTP banner grabbing.
Of course we can use the Nmap for the discovery of the remote operating system and the service fingerprinting but in this tutorial we will not take advantage of that.
Banner Grabbing is a technique that someone can use in order to extract information from application banners.For example if the remote host is a web server,we can try to connect through telnet.The banner results will give us an indication about the operating system and the type of the web server (Apache or IIS).
Command: telnet target_IP 80
In order to do a banner grabbing in the FTP service we will just try to connect through our console to the FTP server.

From the above image we can see that the version is 1.3.1 and the operating system is Debian.There are many things that we can do from here.First we can try to find if there is any public exploit for the ProFTPD 1.3.1 version.If there is then we can launch it against the FTP Service.
If there is not any public exploit for the specific version then we can try to find a valid username and password by using a dictionary attack.We can use any tool like THC Hydra for this job but in this article we will see how it could be achieved through metasploit.
Metasploit Framework has a specific module for attacking FTP servers.So we will search on the metasploit for the module ftp_login.

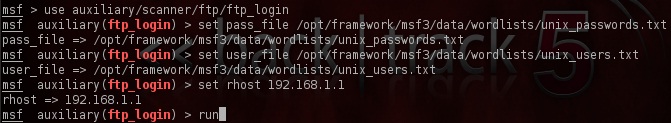
Now that we have found the FTP scanner it is time to configure it.Of course we will need some good wordlists for the usernames and the passwords.If we don’t have then there is no problem because metasploit has a folder with various wordlists.Here we will use the wordlists that contains Unix usernames and passwords.
We are setting the scanner according to the following image and we type run in order to the scanner to start:
The scanner has discovered 3 valid login credentials as you can see from the next 3 images.



So now we have three valid logins to choose in order to connect to the FTP server.Lets try the last one which is the user as username and user as password.

We can see that we have successfully managed to login to the FTP server.Now we can execute the command ls -lat to the server in order to display the list with the current directories and subdirectories and the permissions that we have on the directories.
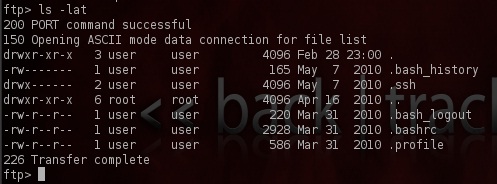
There are two directories that are important here.The SSH because it may contain private SSH keys and the bash_history because it keeps a history of all the commands that the user has run.For example you can find information about user ID,passwords,confidential file names,locations,server names and shared folders.
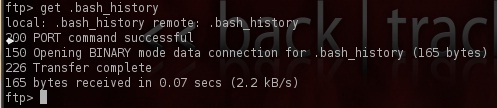
We will download the bash_history file to our computer with the command get as you see it in the image below:
Except of the console for the connection to the FTP server we can use also our browser.We will try to login with the same credentials user/user

After some searching in the directories we have found a directory which contained the following:

We can see that there are 4 folders.A folder named user, a folder named service and a folder named msfadmin.
This is an indication that another account exists under the username msfadmin which probably is an administrator’s account and has more privileges.The reason that we assumed that is because the folders names are the same with the usernames that we have discovered previously.
The previous accounts had passwords same with the usernames.So we will try to login with the following credentials:
Username: msfadmin
Password: msfadmin
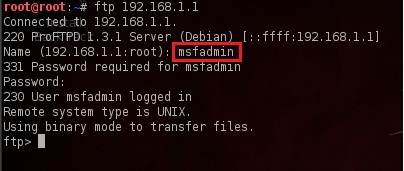
The image above is showing that our try to login with the username/password msfadmin was successful.If the password was different then we could have tried another dictionary attack against the FTP server in order to find and the password.
So we have managed to login to the FTP server with an administrator’s account.
Conclusions
There are some conclusions that we can make regarding this scenario.First of all the banner grabbing allow us to discover valuable information about the FTP server and the target operating system.This means that if the administrator had changed the FTP banner then it would be much harder for us to disclose these information.
In addition we have noticed the weak credentials of the 3 accounts that we discovered.Also the administrator’s account password is the same with the username.This account policy is unacceptable in most of the companies and probably you will not meet something similar.However even large organizations are suffering from weak passwords so eventually it can happen.It is important for that reason to have a good password policy.
On the other hand if a malicious user was trying brute force or dictionary attacks (like this scenario) against the FTP server then it would probably flooded the log files.A security solution that would block the IP address after 3 unsuccessful logins would be the most effective.
Very Nice tutorial!
Thanks Panagiotis for the nice post. Will the scenario be same in case vsftp is running because vsftp encrypts the logon data before transferring into the network. Let us see.
Well written
Hey I keep getting the following error message…
Auxiliary failed: Msf::OptionValidateError The following options failed to validate: RHOSTS.
I’m using BT5 R3 please contact me asaply
@jon
Try the command SET RHOSTS IP in the metasploit module in order to set the IP of the remote host and the problem will be resolved.
Hi,
Could you please help me..? I’m having this error. I just updated metasploit.
[-] Unknown command: SET.
msf auxiliary(ftp_login) > set rhosts ip 10.10.0.40
rhosts => ip 200.74.207.40
msf auxiliary(ftp_login) > run
[-] Auxiliary failed: SocketError getaddrinfo: Name or service not known
[-] Call stack:
[-] /opt/metasploit/msf3/lib/rex/socket.rb:220:in `gethostbyname’
[-] /opt/metasploit/msf3/lib/rex/socket.rb:220:in `getaddresses’
[-] /opt/metasploit/msf3/lib/rex/socket.rb:298:in `resolv_nbo_list’
[-] /opt/metasploit/msf3/lib/rex/socket.rb:312:in `resolv_nbo_i_list’
[-] /opt/metasploit/msf3/lib/rex/socket.rb:358:in `addr_atoi_list’
[-] /opt/metasploit/msf3/lib/rex/socket/range_walker.rb:115:in `block in parse’
[-] /opt/metasploit/msf3/lib/rex/socket/range_walker.rb:56:in `each’
[-] /opt/metasploit/msf3/lib/rex/socket/range_walker.rb:56:in `parse’
[-] /opt/metasploit/msf3/lib/rex/socket/range_walker.rb:26:in `initialize’
[-] /opt/metasploit/msf3/lib/msf/core/option_container.rb:374:in `new’
[-] /opt/metasploit/msf3/lib/msf/core/option_container.rb:374:in `valid?’
[-] /opt/metasploit/msf3/lib/msf/core/option_container.rb:660:in `block in validate’
[-] /opt/metasploit/msf3/lib/msf/core/option_container.rb:659:in `each_pair’
[-] /opt/metasploit/msf3/lib/msf/core/option_container.rb:659:in `validate’
msf auxiliary(ftp_login) >
Hi Robert,it seems that you haven’t configured properly the ftp_login module.As you can see from the screenshot above the correct command is set RHOST IP (IP=the IP address of the remote ftp server) and not set RHOSTS IP xxx.xxx.xxx.xxx.
Hi Netbiox,
Thank you for your answered I tried set RHOSTS because if I do it like above I have this error:
msf auxiliary(ftp_login) > set rhost 200.74.X.X
rhost => 200.74.X.X
msf auxiliary(ftp_login) > run
[-] Auxiliary failed: Msf::OptionValidateError The following options failed to validate: RHOSTS.
msf auxiliary(ftp_login) >
Kind Regards
I had never received any answered from you netbioX. If you don’t mind could you please solve my answer?
Thanks.
I think Robert I have already answered you above as from your output in the first example you put SET RHOSTS IP 10.x.x.x where it should be set RHOSTS 10.x.x.x.In the second output that you have paste it it is obvious that the scanner needs to configure RHOSTS and you set RHOST.Try to do a show options first to see if the metasploit module has the proper configuration.If there is a problem let me know and paste the show options output here.
BT5 R3
File location = /opt/metasploit/msf3/data/wordlists/unix_passwowd.txt
/opt/metasploit/msf3/data/wordlists/unix_users.txt
and as netbiosX suggest > use show options to clarify ideas!
Awsym tut!!! . .admin. . Detailed xplained. . .it wud be gr8 if u show procedure of ftp login via hydra instead of dict attacks. . .
hahahahah @ robert go to linux learn basic linux command… all be solved… n00b
For some reason the result is this! 😕 Someone help? Using backtrack 5R3 and there is no framework but metasploit folder, so the only thing i changed is this. eg.PASS_FILE /opt/metasploit/msf3/data/wordlists/unix_passwords.txt. It sure EXISTS 😀
msf auxiliary(ftp_login) > run
[*] 195.251.193.156:21 – Starting FTP login sweep
[*] Connecting to FTP server 195.251.193.156:21…
[*] Scanned 1 of 1 hosts (100% complete)
[*] Auxiliary module execution completed
looks like there is no password – user combo to test… what exactly is going on?
Thank you m8s 🙂
Great post and explanation, honestly if you can’t understand this article then you shouldn’t even be using Metasploit, no disrespect but learn basic Linux commands and how to navigate around in console and using Metasploit will be a walk in the park!!!
I don’t think i have the default login names and passwords, i don’t see a frameworks folder in my opt. Is this something I download?
In case you haven’t figured this out – it should be in the opt folder – keep digging through your metasploit folder it’s under something like msf3/opt/data/wordlists – I had to dig for it and jump through a shortcut but it is in there.
Vasilis: Did you ever figure out that issue? I’m having the same trouble.
on my kali rolling you will fine the wordlists on /usr/share/metasploit-framework/data/wordlists