During Microsoft Exchange installation a number of security groups are created in the Active Directory related to Exchange. Some of these groups are linked to each other and could allow domain escalation via abuse of access control lists. Specifically user accounts that are a member of Organisation Management security group can escalated to domain administrator by adding themselves to the Exchange Trusted Subsystem group.
This group is a member of Exchange Windows Permissions security group which by default has writeDACL permissions on the domain and therefore these permissions will inherited to the account. Obtaining these permissions on the domain can allow modification of the ACL in order to get replication level privileges. This escalation technique has been discovered by Rindert Kramer and Dirk-Jan Mollema and demonstrated in the blog of Fox-IT.
The following image demonstrates the relevant Microsoft Exchange Security Groups that are required for the domain escalation.

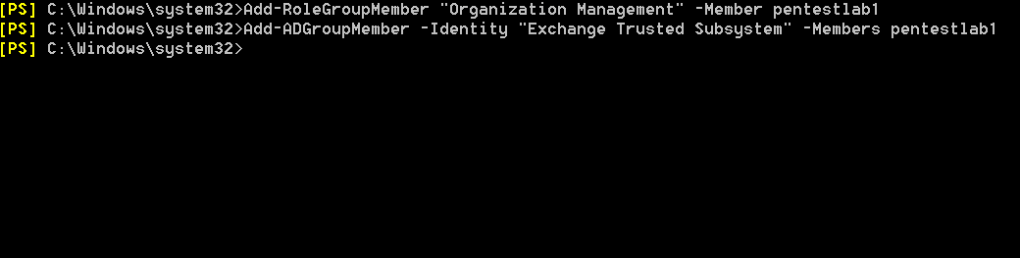
The user can be added to the relevant groups by executing the following commands from the Exchange Management Shell. Since the user is already a member of the Organization Management security group he should be able to access the Exchange server with his domain credentials.
Add-RoleGroupMember "Organization Management" -Member pentestlab1 Add-ADGroupMember -Identity "Exchange Trusted Subsystem" -Members pentestlab1
Running the following command in the Windows command prompt will verify that the user was added to the Exchange Security Groups.
whoami /groups

The Invoke-ACLpwn PowerShell script can be used to perform the modification in the ACL of the domain in order the user to obtain the following privileges:
- Replicating Directory Changes
- Replicating Directory Changes All
The script requires SharpHound for retrieving Access Control Entries (ACE’s) and enumeration of domain objects and Mimikatz for DCSync operations (dumping the password hash of Kerberos account). The following command can be executed to retrieve the hash of the Kerberos account (krbtgt).
.\Invoke-ACLPwn.ps1 -SharpHoundLocation .\SharpHound.exe -mimiKatzLocation .\mimikatz.exe -userAccountToPwn krbtgt

It should be noted that adding the user to the Exchange Trusted Subsystem security group manually from the Exchange Management Shell is not required as the script will attempt to find the chain and will add the user automatically.

Obtaining the hash of the Kerberos account can be used to create a Golden ticket which can access any resource on the domain by impersonating any user on the network (even users that doesn’t exist).
Leave a comment