Microsoft Office is a common application that is deployed in every organisation. This wide usage transforms office into a tool that can be utilized to perform attacks that would allow the red team to gather domain hashes or execute arbitrary code.
Historically execution of code in Microsoft office was performed through the use of Macros. However SensePost discovered another method of executing arbitrary code by using the DDE (Dynamic Data Exchange) protocol. There are various places inside products of office that execution of code is accepted via DDE and this article will demonstrate the majority of these attack vectors. The article DDE Payloads can be used in conjunction with this post for the production of payloads.
Word
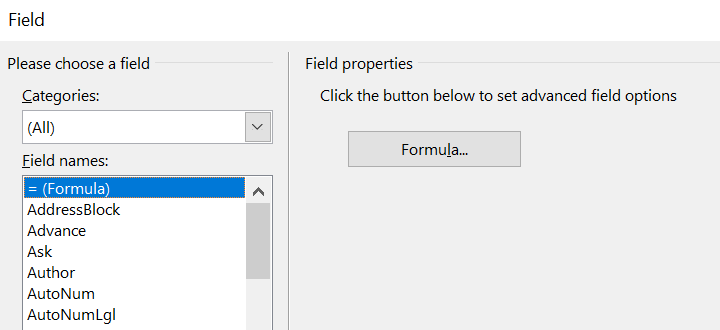
In Microsoft Word the easiest method is to insert a field code as it has been described in the original post by SensePost and embed the payload inside the formula.
Insert-> Quick Parts-> Field
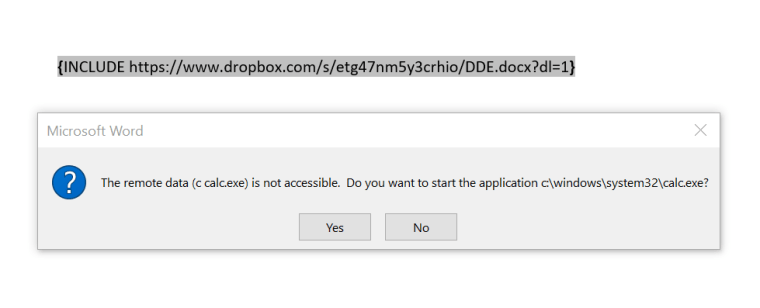
Adding the following payload inside the brackets will produce some dialog box the next time that the file is opened. If the user chooses the Yes option the payload will be executed.
{DDEAUTO c:\\windows\\system32\\cmd.exe "/k calc.exe"}

Alternatively it is possible to use a Macro to insert a payload into a field code as it was described by Paul Ritchie in his blog.
''' Programmatically inserts a new field code into a word document at the current selection index. ''' This is of type "wdFieldDDEAuto" which is a field code which executes Dynamic Data Exchange (DDE) ''' When the document is opened. This includes an example PoC which launches calc.exe Public Sub FieldCodeFun() ' Payload String Dim payload As String payload = """c:\\windows\\system32\\calc.exe"" ""/c calc.exe""" ' Insert our payload as a field code Selection.Collapse Direction:=wdCollapseEnd ActiveDocument.Fields.Add Range:=Selection.Range, _ Type:=wdFieldDDEAuto, Text:=payload End Sub

The payload will just execute calculator but it can be modified to contain any other payload.
Mike Czumak did a great discovery which has been discussed in his blog regarding loading the malicious DDE from another Word document which is externally hosted. The INCLUDE field code can be used with this attack vector combined with the external URL.
Excel
In Microsoft Excel DDE payloads can be utilized through the use of formulas. The following two formulas wiill execute code (calculator in this case) with the second formula to obfuscate the dialog box message to make it more legitimate.
=cmd|'/c calc.exe'!A1 =MSEXCEL|'\..\..\..\Windows\System32\cmd.exe /c calc.exe'!''

The following dialog box will appear when the user opens the malicious Excel spreadsheet.

The second formula will still execute code but the message in the dialog box will be modified and instead of asking the user to start CMD.EXE it will ask him to start MSEXCEL.exe.

Outlook
In Outlook there are various locations that execution of DDE payloads can happen. Depending on the situation every method could be useful. For example if domain credentials have been obtained it might be easier to weaponise an email message and to send to multiple other users in order to obtain more shells inside the organisation.
Message
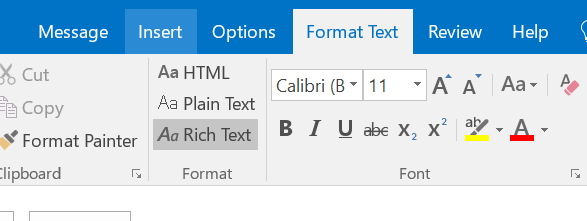
Sending an outlook message that contains a DDE can also execute code automatically. The same applies and for email messages that are sent as attachments.

However the email message needs to be sent as Rich Text Format (RTF) and delivered as RTF since some mail services convert all emails to HTML which will make the DDE payload to not work.
When the message arrive in the inbox of the user the DDE will execute upon browsing in that message.

Contact
Creation of a new contact or modification of an existing one and placing the DDE payload into the notes area can lead to execution of code.
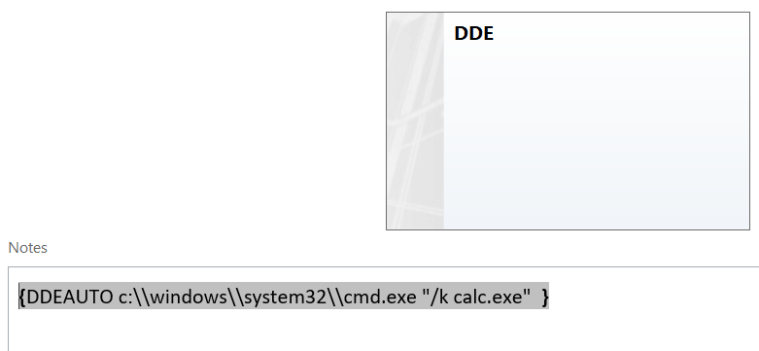
The contact needs to be sent to the target user.

When the user opens the contact it will execute the embedded DDE payload.

Calendar Invite
The same concept applies and via calendar invitations. Sending a meeting invitation with a DDE payload will result in code execution if the user interacts with that invite (open or cancel).

Great article like Always. You Can find à good article too here: https://null-byte.wonderhowto.com/how-to/hide-dde-based-attacks-ms-word-0180784/
It does not works in Word 2016 and excel 2016 when you open the sheet again it cleans this formulas
It is working on Word 2016 for sure. It has been tested and verified. In excel it is true that this is happening. However you can use Word or Outlook as alternative methods during assessments.
Well I followed every step and nothing happened. Word shows me the warning about external references but it dont execute calc.
In that case check if your version of office is patched. The following registry needs to have the value 2 which means enable. Computer\HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Word\Security\AllowDDE
Yeah you got it! There is no AllowDDE entry! I’m gonna try to create it later! Thank you!