HTML Injection is a vulnerability which occurs in web applications that allows users to insert html code via a specific parameter for example or an entry point. This type of attack can be used in combination with some sort of social engineering in order to trick valid users of the application to open malicious websites or to insert their credentials in a fake login form that it will redirect the users to a page that captures cookies and credentials. In this tutorial we are going to see how we can exploit this vulnerability effectively once it is discovered. For the needs of the article the Mutillidae will be used as the vulnerable application.
Let’s say we have a page like the following:
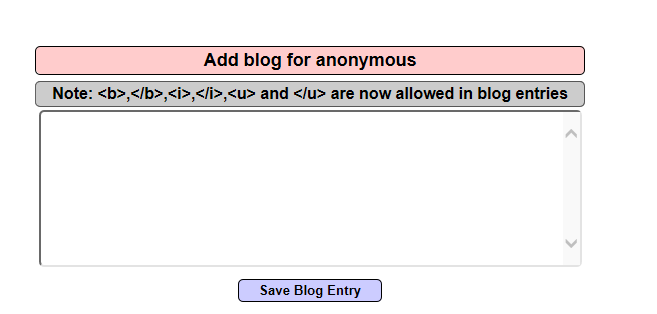
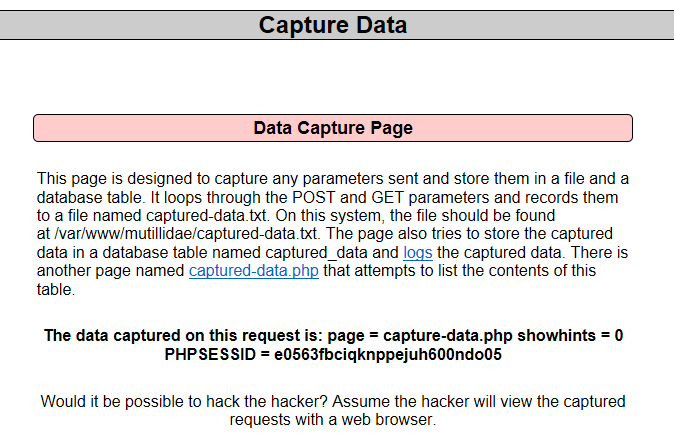
Of course in this example there is an indication that this form is accepting HTML tags as it is part of the functionality of the application. A malicious attacker will think that he can exploit the users of this application if he set up a page that is capturing their cookies and credentials in his server. If he has this page then he can trick the users to enter their credentials by injecting into the vulnerable page a fake HTML login form. Mutillidae has already a data captured page so we are going to use this page for our tutorial.
Now we can inject HTML code that it will cause the application to load a fake login form.

The next image is showing the fake login form:

Every user that will enter his credentials it will redirected to another page where his credentials will stored. In this case the credentials can be found at the data capture page and we can see them below:

Conclusion
As we saw in this article HTML injection vulnerabilities are very easy to exploit and can have large impact as any user of the web application can be a target. System admins must take appropriate measures for their web applications in order to prevent these type of attacks.
Thanks for your article, a question: The data captured is stored in a file in the same server o can be transfer to another server??
Regards
The data capture page is stored on the web server that you control.
Hi! Thanks for your article but the use of Mutillidae (a learning plateform, done to be vulnerable as much as possible) makes this article low level. The same thing on a real website would be better.
Nevertheless, your example is good 🙂
Nice one (y) and very nice this site
Great