SMTP is a service that can be found in most infrastructure penetration tests.This service can help the penetration tester to perform username enumeration via the EXPN and VRFY commands if these commands have not been disabled by the system administrator.There are a number of ways which this enumeration through the SMTP can be achieved and there will be explained in this article.
The role of the EXPN command is to reveal the actual address of users aliases and lists of email and VRFY which can confirm the existance of names of valid users.
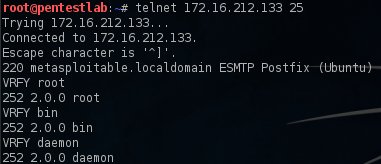
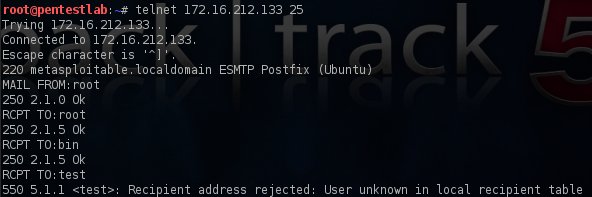
The SMTP enumeration can be performed manually through utilities like telnet and netcat or automatically via a variety of tools like metasploit,nmap and smtp-user-enum.The following 2 screenshots are showing how we can enumerate users with the VRFY and RCPT commands by using the telnet service.
Metasploit
The module that can perform user enumeration via SMTP in Metasploit Framework is the following:
auxiliary/scanner/smtp/smtp_enum
The only thing that this module requires is to enter the IP address of the remote host and to execute it with the run command as the other options have been filled automatically from metasploit.

We can see the results of the metasploit in the next image:

smtp-user-enum
Another tool that can be used is the smtp-user-enum which provides 3 methods of user enumeration.The commands that this tool is using in order to verify usernames are the EXPN,VRFY and RCPT.It can also support single username enumeration and multiple by checking through a .txt list.So in order to use this tool effectively you will need to have a good list of usernames.Below is an example of a scan with the VRFY command which discovered the following usernames.

Also smtp-user-enum can be used for discovery valid email addresses instead of usernames.The next image indicates this usage.

Nmap
SMTP enumeration can be implemented through the Nmap as well.There is a script in the NSE (Nmap Scripting Engine) that can be used for SMTP user enumeration.The generic usage of the script is the following:
nmap –script smtp-enum-users.nse 172.16.212.133
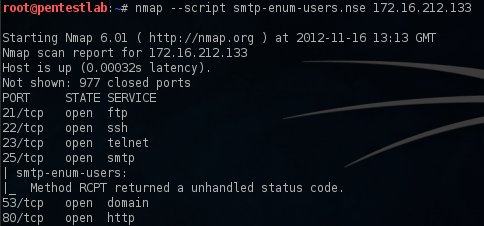
As we can see from the above image the enumeration didn’t succeed in this case.
Conclusion
SMTP is a common service that can be found in every network.Administrators need to properly configured the mail servers by disallowing the execution of the commands EXPN,VRFY and RCPT in order to avoid this leakage.From the other side penetration testers can use the usernames that have been obtained from this enumeration to conduct further attacks on other systems.
Malicious use of EXPN and VRFY was known at least as far back as 1997 (see the link below). Maybe this calls attention to an easy, slick GUI doing it, but people have been scripting it for many, many years. This isn’t exactly news.
http://www.gossamer-threads.com/lists/qmail/users/432?do=post_view_threaded
That’s true,it isn’t something new but it can still be found in some systems (I had this experience recently)and of course in penetration test certifications as part of a practical component.
I don’t think this post is claiming to introduce us to a new SMTP enumeration technique but it gives a nice overview of all the tools you can use to enumerate SMTP users.
Though i agree with Paco Hope, people have been scripting this enumeration technique since many years so a GUI would still be welcome.
However, I think the most expected feature is to make it this scripts modular and metasploit brought us this.
In the end, when doing a pentest, you can always run an nmap NSE script so you can find out what SMTP commands are available on the remote server, then run the metasploit auxilary module to find users.
Anywyas, thanks to the author for this post.
Have you compared the results given by the three methods when using the same input lists? Do they all find the same results?
Good question Robin!I have tested all these methods on the same box so no,the results are different.The smtp-user-enum effectively enumerate it all the users without any errors while the metasploit as you can see from the screenshot stopped but I haven’t investigate it yet why it happened.
If it’s not a matter of dictionnary, then maybe the smtp-user-enum Metasploit module is querying too fast so it gets RST packets after a short while of guessing, hence “error – connection reset by peer”.
Usually with metasploit you can set the delay between each request the module sent. I guess it’s worth giving it a shot.
If you can get the SMTP server to log all requests then that could show what is happening otherwise sniff the traffic and check each username and response.
Reblogged this on CoreNumb Security.
This is awesome man.. complete tutorial thank you so much bro.