VSFTPD is an FTP server that it can be found in unix operating systems like Ubuntu, CentOS, Fedora and Slackware. By default this service is secure however a major incident happened in July 2011 when someone replaced the original version with a version that contained a backdoor. The backdoor exists in the version 2.3.4 of VSFTPD and it can be exploited through metasploit.
So let’s assume that we have scanned a host and we have discovered the version 2.3.4 of VSFTPD running on the system.

We can open the metasploit framework in order to search for the vsftpd module.

As we can see there is only one module that we can use. So we will start the configuring the module appropriately. In the next screenshot you can see the configurations that we need to do in this exploit in order to be executed successfully.

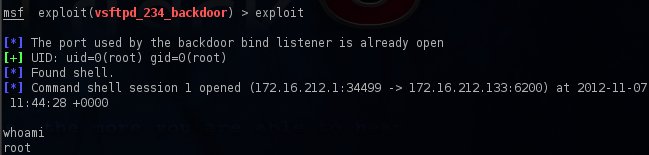
We will execute the module with the exploit command and we will notice that it will return a shell to us with root privileges.
Conclusion
This version of course has become obsolete so don’t expect to discover it in real world systems. However if you want to play with this vulnerable service you can find it in the metasploitable 2 virtual machine.
Hello, I have one question, I performed this attack and I got this:
Banner: 220 Hello
User: 331 Please specify the password.
I thing that it is really secure and goot protect.
What do you mean?
Hello Filip
First of all this exploit applies only to versions 2.3.4 that have the backdoor.if you tried it in different versions it will not work.The reason that you got this message is because the metasploit module just passes a smiley face to the FTP server instead of a username to trigger the backdoor.After this message you can use the netcat utility in order to connect.You can try netcat -vv IP 6200.