During a penetration testing engagement we might come across with the NetBIOS service.In the past the NetBIOS protocol was enabled in almost every network that was running Windows.In nowadays system administrators are disabling this service due to the fact that plenty of information can be unveiled regarding shares,users and domain controllers.However NetBIOS can still be found on default configurations of Windows Server 2008 and Windows Vista so in a penetration testing this protocol can be abused if we discover it.
Generally the NetBIOS provides the following three services:
- Name Service: UDP/137
- Datagram Service: UDP/138
- Session Service: TCP/139
In systems that have this service enabled we can use some tools in order to discover information about the hostnames and domains especially in windows networks.In some cases this protocol can be found and in Linux systems.
The two basic tools are nbtstat and nbtscan.The nbtstat is a command line utility that is integrated in windows systems and it can unveil information about the netbios names and the remote machine name table or local but only for one host.From the other hand the nbtscan is a netbios nameserver scanner which has the same functions as nbtstat but it operates on a range of addresses instead of one.
The next image is showing the usage of the nbtstat:
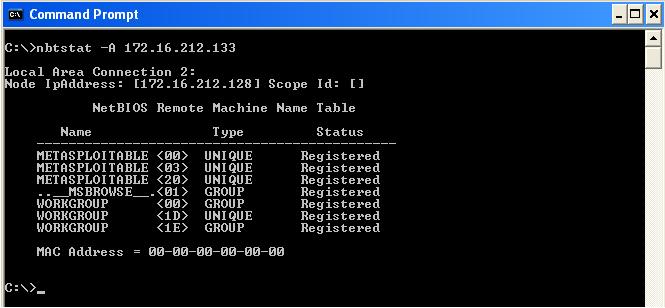
The numeric values are called suffixes.For example the <01> and <1D> suffixes indicates the Master Browser,the <20> that the machine is running File Server service,the <03> that a messenger service is running and the <00> means that a workstation service is running as well.The <1E> is the Browser Service Elections.
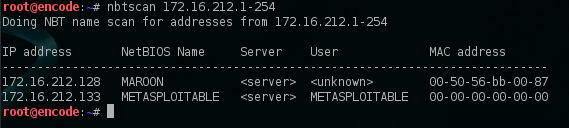
The nbtscan is by default installed on backtrack but there is a version as well for windows platforms.We can use the nbtscan in order to scan the whole network.As we can see from the next image we have discovered the IP addresses,the NetBIOS names,the users that are logged in and the MAC addresses from the hosts that are running the NetBIOS service on the network.
We can use also the -v option in order to produce a verbose output.
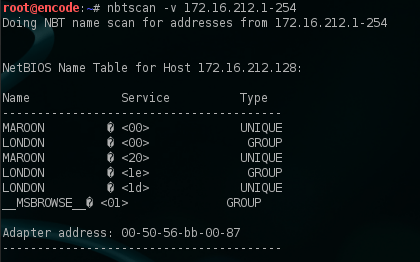
With the verbose option the output format is similar to the nbtstat.Again the <01> indicates the Master Browser service,the <00> the workstation,the <20> the File Server service and the <1e> and <1d> the Browser Service Elections and the Master Browser.Also we can see that the domain that this workstation belongs is London.
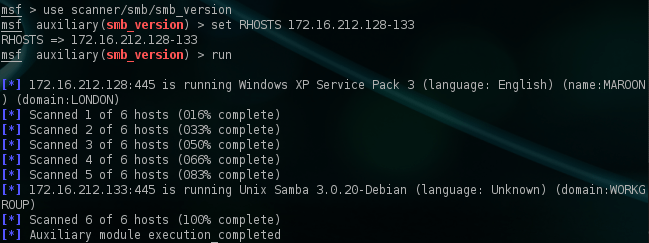
As an alternative option we can use the metasploit module smb_version which will unveil additional information like the operating system name and version,the service pack level,the language,the system and domain name.
Conclusion
As we saw in this article from systems that had enabled the netbios service we have managed to discover plenty of information including the domain names,users,operating systems versions,MAC addresses and other.This service if found enabled can be used in the information gathering stage of a penetration test.So from the security point of view it is recommended this service to be disabled.
“The nbtstat is a DOS utility”
WHAT!?! 🙂 Did you mean “command line utility” ? 🙂
Yes you are right!I just want it to say that it is a utility that is running via the command prompt.Thank you for the notice 😉
Just a couple of points:
1. The inclusion of “MAC addresses” in the list of discoverable items is a bit of a red herring. That can be found just by listening for ARP requests when on the same segment. That is never a private piece of data.
2. What is important concerning the nbtscan results is that since it uses a different protocol from listening to requests other than ICMP it provides a means to find servers that may have the ICMP (echo request) listening capability firewalled and thus show possibly “hidden” servers.
3. It is one thing to say “So from the security point of view it is recommended this service to be disabled”. However, what also needs to be stated to make this article even better is a) how to disable the services providing this functionality and b) the operational impact of doing so. Security does not and cannot operate in a vacuum and must take in consideration the real world requirements.
First of all thank you very much Ken for your comment.
For the first point you are right.This piece of information can be retrieved easily just by doing an arp scan.Also of course I am not consider the discovery of a MAC address as a private piece of data but it is an information that you can obtain along with other results from a netbios scan so that’s why I have mentioned that as well.
For the third point I will slightly disagree because the purpose of this article was to introduce what kind of information can be obtained from a netbios scan and not how to fix the issue.I agree that when we are talking about security we always have to look about the right balance between security and functionality but the job of a penetration tester is to exploit services in order to collect information and to gain access.How to fix something is the job for a security engineer.The operational impact is another discussion 😉
Thank you very much for the feedback and the comment.It can help in the creation of a discussion about this matter!
You can use smbclient-L xxx.xxx.xxx.xxx (iP)
Thank you for this. It should be noted that nbtscan only works in Linux but nbtstat works in both DOS/Windows and Linux.
I don’t know why Microsoft doesn’t include a utility like nbtscan in their OS, or why I keep asking questions like that.