Unquoted Service Path
In Windows environments when a service is started the system is attempting to find the location of the executable in order to successfully launch the service. If the executable is enclosed in quote tags “” then the system will know where to find it. However if the path of where the application binary is located doesn’t contain any quotes then Windows will try to find it and execute it inside every folder of this path until they reach the executable.
This can be abused in order to elevate privileges if the service is running under SYSTEM privileges.
Method 1 – Manual Exploitation
The first step is to try and discover all the services that are running on the target host and identify those that are not enclosed inside quotes.
The following command can be used as a quick way for this identification:
wmic service get name,displayname,pathname,startmode |findstr /i “auto” |findstr /i /v “c:\windows\\” |findstr /i /v “””

The next step is to try to identify the level of privilege that this service is running. This can be identified easily:

Since the service is running as SYSTEM and is not enclosed in quote tags the final check is to determine if standard users have “Write” access in the directory of where the service is located or in any previous directory like C:\ or C:\Program Files (x86)\. Folder permissions can be identified with the use of a Windows built-in tool called icacls (Integrity Control Access Control Lists):

The users in the Lenovo folder have the ability to write content which means that it is possible to generate a malicious binary and plant this executable inside that folder. In that way when the service will be restarted, Windows will launch this executable instead of the legitimate one by giving SYSTEM privileges to the user.
Metasploit can be used in order to generate the binary that needs to be dropped into the target system.


From Metasploit a listener needs to be configured so the payload can establish a connection back to the system of the attacker:

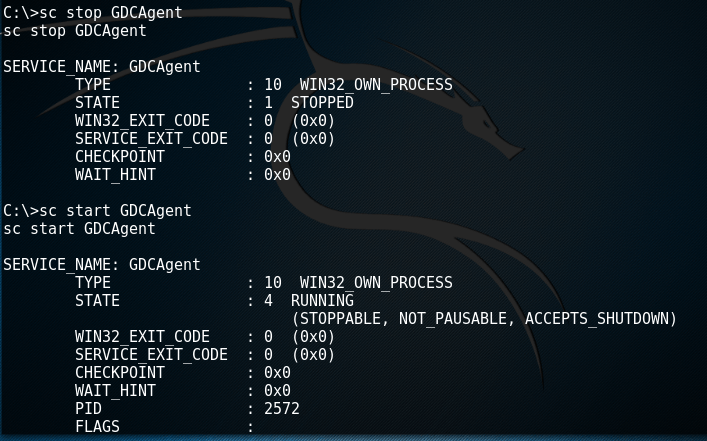
From the moment that the service will be restarted the payload will be executed and it will return a Meterpreter session with the privileges that the original service had which in this case it was SYSTEM:

Method 2 – Metasploit
Metasploit Framework provides a module that can automatically check the target system for any vulnerable services, generate the payload, drop the binary into the target folder that has Write access, restart the service and remove the binary as soon as the payload is executed and a session is created.
In order to be able to use this module an existing Meterpreter session is needed.


Method 3 – PowerSploit
PowerSploit can be used as well as a tool for discovery and exploitation of this issue as except of the script that it can identify all the services running on the system without quote tags it can also generate a binary that will add a user into the local administrator group.

As it can be seen above the Get-ServiceUnquoted script not only discovered the service but it does all the other necessary checks as well like: identification of the path that users have Write access, discovery of the privileges that the service is running (which in this case is LocalSystem) and determination of whether a user can restart the service. Additionally it gives the PowerShell function to generate the binary in order to exploit this issue.
By executing the Write-ServiceBinary function PowerSploit will generate an executable into the specified path with a simple payload that it will try to add the user “john” into the local administrators group when the service will be restarted.


The verification that the user has been created and added into the local administrator group can be done with the following command:

Conclusion
In nowadays the majority of the applications are enclosed quote tags. However there are some major vendors that still release application configured that way. Additionally it should be noted that in internal penetration tests a lot of custom applications are vulnerable to this issue and it is always a good practice to check for them.
So in order to be able to successfully exploit this issue for privilege escalation the following requirements needs to be in place into the target host:
- An application executable that is not enclosed in quote tags
- The application needs to run under the privileges of SYSTEM
- Users should have Write access in one of the directories of the original binary path
- Users should be able to restart the service