Post Exploitation – Discovering Network Information In Windows
In network infrastructure penetration tests if we manage to exploit one system then it is easy to obtain information for the network that this system is part of.This information is important because in almost every network penetration test the ultimate goal is to become domain administrator and in order to achieve that it is necessary to know the appropriate commands that will help us to gather information about the network that we are already inside.In this article we will see how we can gather information about windows networks that we are conducting the penetration test from the system that we have already exploited.
Lets say that we have exploited a windows system and we want to know more about the network that this system belongs to.The first and most common command is of course the ipconfig /all which it will display to us all the information about the network adapters of the host and the Windows IP configuration as the picture below is showing:

Another command is the ipconfig /displaydns which it will display the contents of local DNS cache.

Systems in internal networks most of the times contain shared folders which can be listed with the command net share.

We might also want to discover other internal networks that exist by examining the machine routing table with the command route print.

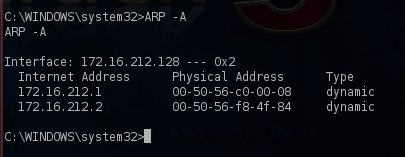
The ARP -A command will list all the systems that are currently in the machine’s ARP table helping us to discover other valid hosts.
We can also use the network diagnostic command of the system to obtain information about operating system,network adapters,network clients and other network configuration with the command netsh diag show all.

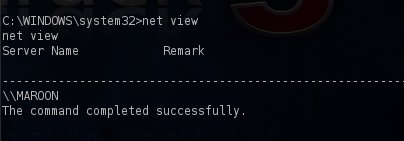
Another information that is important to learn about the host that we have exploited is to see which other hosts are on the same workgroup.The command that we will need to type is the net view.
Last but not least the netstat command can be used with the parameters -n -a -o to display all the active connections along with the IP addresses and process ID of each connection.

Conclusion
In this article we saw some common commands and their output that can be used for post exploitation activities in Windows networks.The majority of these commands will help us to identify new hosts and network shares which can lead us to compromise further systems on the network.