DNSenum – Gathering DNS Information
DNSenum is a tool that it was designed with the purpose of enumerating DNS information about a domain.Then information that you can obtain from this tool is useful for the phase of information gathering when you are conducting especially a penetration test.
So lets say that you want to obtain information about a specific domain.In this article we will use different domains as an example in order to see the different responses that we can get.First you will need to go to the directory that the DNSenum is located.In backtrack 5 this in the /pentest/enumeration/dns/dnsenum and in order to run it you can use the command: perl dnsenum.pl [host]
The DNSenum will start querying the DNS servers of scanme.org.The first information that we will get is the host address which for scanme.org is the 74.207.244.221.Next we will see the name servers which will give us an idea of the hosting provider that the scanme.org is using and after that is the MX record where we can see the mail server of our target host.

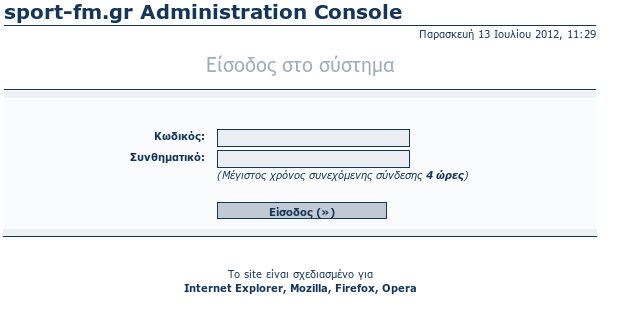
After that the DNSenum will start the DNS Zone Transfer.Performing a Zone Transfer you can discover more information about a domain like any sub-domains that are included in the same zone, SOA records etc.In the screenshot below you can see the results after performing a zone transfer for the domain sport-fm.gr.

By reviewing the results we can see that the SOA record is the http://www.sport-fm.gr.This means that this DNS name server is the best source of information for the data within this domain.Also we have a list with all the sub-domains and the interesting thing is that we have located the administration panel which is on the sub-domain admin.sport-fm.gr.
Another option that DNSenum offers is the Google Scraping which it queries google search pages to discover various domain names of the target domain.This can be particular helpful when the zone transfer is disabled.Basically what it does is trying to get results from google by using the following command:
allinurl: -www site:target.com
Conclusion
DNSenum is a great tool to be used in the information gathering stage of a penetration testing.As we saw in this article we obtained a lot of information about our targets and we even discovered an administration panel from the early stage of our penetration test which can help us to perform further attacks on the target.