Metasploit Metsvc Backdoor
Metasploit offers the ability to place a backdoor on the remote system in order to maintain access after your exploitation.In this article we will see how we can work with the metsvc backdoor and what are the limitations of it.
Lets say that we have already compromised the target by using a meterpreter service payload.We can have a look at the available options of the metsvc backdoor by executing the command run metsvc -h

As we can see there are only 2 options:The -A which automatically starts the multi/handler and the -r which uninstalls the service that the backdoor has created.
So we will execute the command run metsvc -A.This command will upload some files and it will create a windows service on the remote machine which will run on the port 31337.

As you can see from the image above we now have 2 sessions open on the remote machine.From the other hand on the remote machine we can notice that there is a process name metsvc-server.exe.This process is the backdoor.

If you want to remove the backdoor from the target machine you can use the command run metsvc -r in order to achieve that.

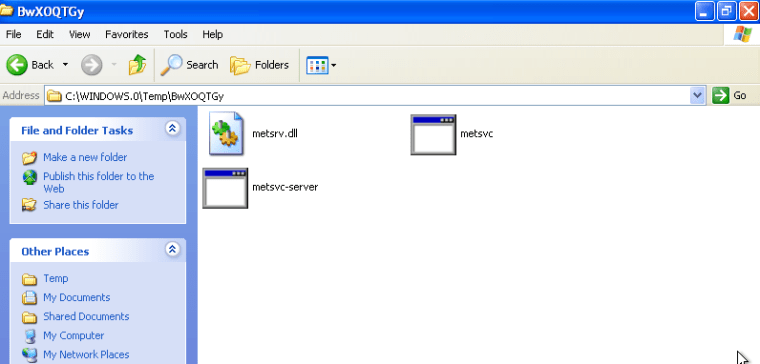
This command is stopping the backdoor from running but it doesn’t delete the files that had created when we ran the backdoor the first time so we need to remove it manually in order to clean up the system.The files that we need to remove are the following:
Conclusion
The metsvc backdoor runs as service on the remote system and requires no authentication so anyone that will find the backdoor can connect through it to our target.Also it can be discovered easily by using a simple port scanner so it is risky to use.From the other hand it is less noisy compared to the persistence backdoor.
Don’t try this backdoor in real systems.If you want to use it in order to expand your knowledge about backdoors use it on a safe and isolated environment.