Nmap – Techniques for Avoiding Firewalls
As a penetration tester you will come across with systems that are behind firewalls and they are blocking you from getting the information that you want.So you will need to know how to avoid the firewall rules that are in place and to discover information about a host.This step in a penetration testing called Firewall Evasion Rules.
Nmap is offering a lot of options about Firewall evasion so in this article we will explore these options.
Fragment Packets
This technique was very effective especially in the old days however you can still use it if you found a firewall that is not properly configured.The Nmap offers that ability to fragment the packets while scanning with the -f option so it can bypass the packet inspection of firewalls.

In the next image we can see that Nmap is sending packets 8-bytes size when we are doing a scan with the -f option.

Specify a specific MTU
Nmap is giving the option to the user to set a specific MTU (Maximum Transmission Unit) to the packet.This is similar to the packet fragmentation technique that we have explained above.During the scan that size of the nmap will create packets with size based on the number that we will give.In this example we gave the number 24 so the nmap will create 24-byte packets causing a confusion to the firewall.Have in mind that the MTU number must be a multiple of 8 (8,16,24,32 etc). You can specify the MTU of your choice with the command –mtu number target.

Use Decoy addresses
In this type of scan you can instruct Nmap to spoof packets from other hosts.In the firewall logs it will be not only our IP address but also and the IP addresses of the decoys so it will be much harder to determine from which system the scan started.There are two options that you can use in this type of scan:
- nmap -D RND:10 [target] (Generates a random number of decoys)
- nmap -D decoy1,decoy2,decoy3 etc. (Manually specify the IP addresses of the decoys)

In the next image we can see that in the firewall log files exist 3 different IP address.One is our real IP and the others are the decoys.
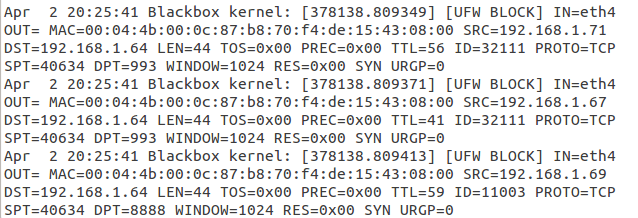
You need to have in mind that the host that you will use as decoys must be online in order this technique to work.Also using many decoys can cause network congestion so you may want to avoid that especially if you are scanning the network of your client.
Idle Zombie Scan
This technique allows you to use another host on the network that is idle in order to perform a port scan to another host.The main advantage of this method is that it very stealthy because the firewall log files will record the IP address of the Zombie and not our IP.However in order to have proper results we must found hosts that are idle on the network.
Metasploit framework has a scanner that can help us to discover hosts that are idle on the network and it can be used while implementing this type of scan.

As we can see from the above image the scanner has discovered that the IP addresses 192.168.1.67 and 192.168.1.69 are idle on the network and are potential candidates for use on an Idle Zombie Scan.In order to implement an Idle Zombie scan we need to use the command nmap -sI [Zombie IP] [Target IP]

We can see the effectiveness of this scan just by checking the firewall logs.As we can see the log files record the IP address of the Zombie host (SRC=192.168.1.69) and not our IP address so our scan was stealthy.

Source port number specification
A common error that many administrators are doing when configuring firewalls is to set up a rule to allow all incoming traffic that comes from a specific port number.The –source-port option of Nmap can be used to exploit this misconfiguration.Common ports that you can use for this type of scan are: 20,53 and 67.

Append Random Data
Many firewalls are inspecting packets by looking at their size in order to identify a potential port scan.This is because many scanners are sending packets that have specific size.In order to avoid that kind of detection you can use the command –data-length to add additional data and to send packets with different size than the default.In the image below we have changed the packet size by adding 25 more bytes.

The size of a typical packet that nmap sends to the target is 58 bytes as you can see in the image below.

With the command that we have used –data-length 25 we changed that value to 83 in order to avoid being discovered by firewalls that will check for the default packet size that nmap generates.

Scan with Random Order
In this technique you can scan a number of hosts in random order and not sequential.The command that you use to instruct Nmap to scan for host in random order is –randomize-hosts.This technique combined with slow timing options in nmap command can be very effective when you don’t want to alert firewalls.

MAC Address Spoofing
Another method for bypassing firewall restrictions while doing a port scan is by spoofing the MAC address of your host.This technique can be very effective especially if there is a MAC filtering rule to allow only traffic from certain MAC addresses so you will need to discover which MAC address you need to set in order to obtain results.
Specifically the –spoof-mac option gives you the ability to choose a MAC address from a specific vendor,to choose a random MAC address or to set a specific MAC address of your choice.Another advantage of MAC address spoofing is that you make your scan more stealthier because your real MAC address it will not appear on the firewall log files.
Specify MAC address from a Vendor —-> –spoof-mac Dell/Apple/3Com
Generate a random MAC address —-> —spoof-mac 0
Specify your own MAC address —-> —spoof-mac 00:01:02:25:56:AE

Send Bad Checksums
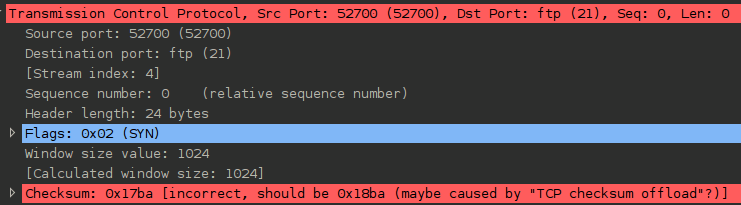
Checksums are used by the TCP/IP protocol to ensure the data integrity.However sending packets with incorrect checksums can help you to discover information from systems that is not properly configured or when you are trying to avoid a firewall.
You can use the command nmap –badsum IP in order to send packets with bad checksums to your targets.In the image below we didn’t get any results.This means that the system is suitable configured.

You can see below a sample of a packet with bad checksum that we have sent:
Conclusion
We have seen that Nmap offers a variety of methods that it can be used to avoid a firewall that exists on the network that we are scanning and to get proper results from the target host.The problem in many of the cases that we have seen is the bad configuration of Firewalls that allowed us to get results from the target.So in a network that have IDS and firewalls properly configured many of the techniques may not work.Every situation is different so you need to decide which one will work for you.